Account & Session Takeover Prevention
29%
$17B
46%
23K+
Why ATO is Getting Harder to Stop
Two ways in. One is invisible.
Stolen username + password
Organizations need to address both
Why Existing Tools Leave Consumer Platforms Exposed
Infostealers move faster than detection tools
46% of compromised devices are outside your controls
Long session lifetimes create a wide attack window
Fraud hits before you know the session was stolen
Flare ASTP: Intelligence From The Source
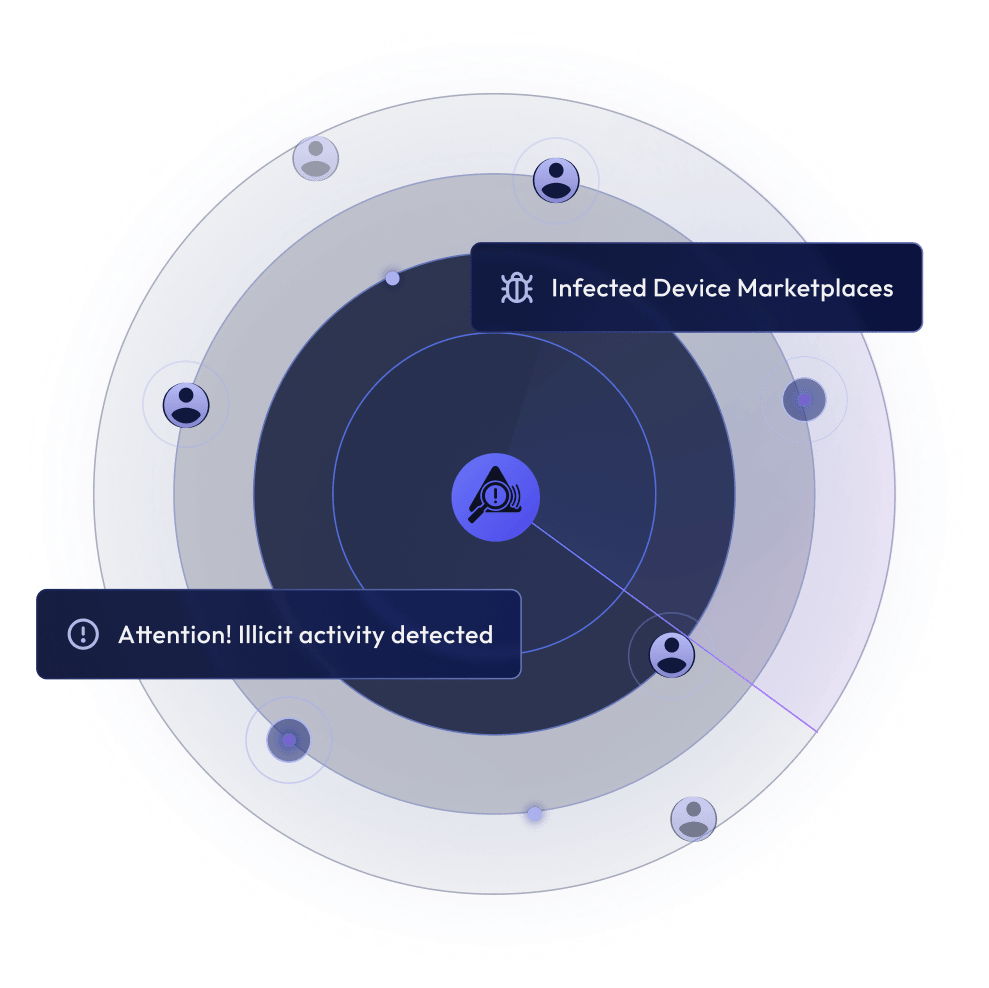
Stolen session cookie detection
Stolen credential detection

Real-time criminal market monitoring
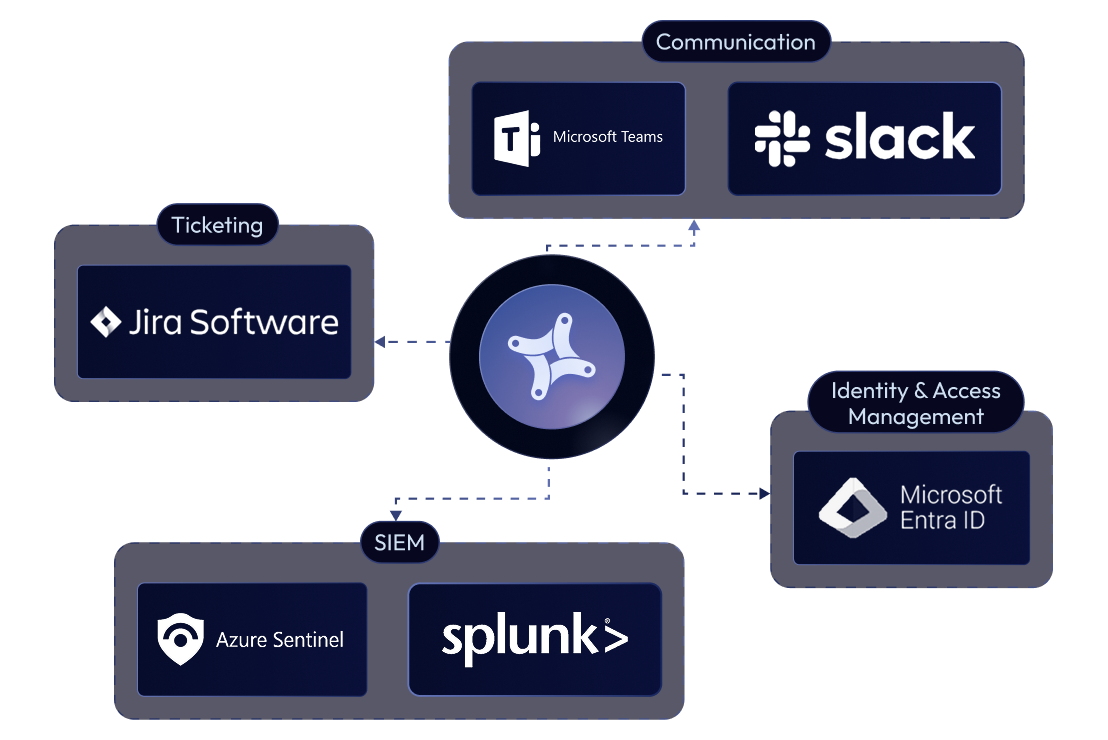
API-first, fits your existing workflows
What Prevention Looks Like at Scale
$17B
54%
< hrs
29% of US adults have experienced account takeover. The number has risen every year since 2021 — and the attack methods are getting harder to detect.
Built For Consumer Platforms at Scale
E-Commerce & Retail
Gaming & Entertainment
Social Media
Fintech & Crypto
Travel & Hospitality
News & Media
Banking & Insurance
Sports Betting & Gaming
Resources on Account and Session Takeover
Frequently Asked Questions
What is the difference between credential theft and session cookie theft?
Credential theft uses stolen usernames and passwords to log in. The attacker must pass authentication, MFA can stop this, and the login attempt generates signals your tools can act on. Session cookie theft is different: the attacker loads a stolen session token directly into a browser, bypassing login entirely. No password, no MFA, no login event. They arrive as a trusted, authenticated user with nothing for your tools to detect.
How does Flare ASTP work?
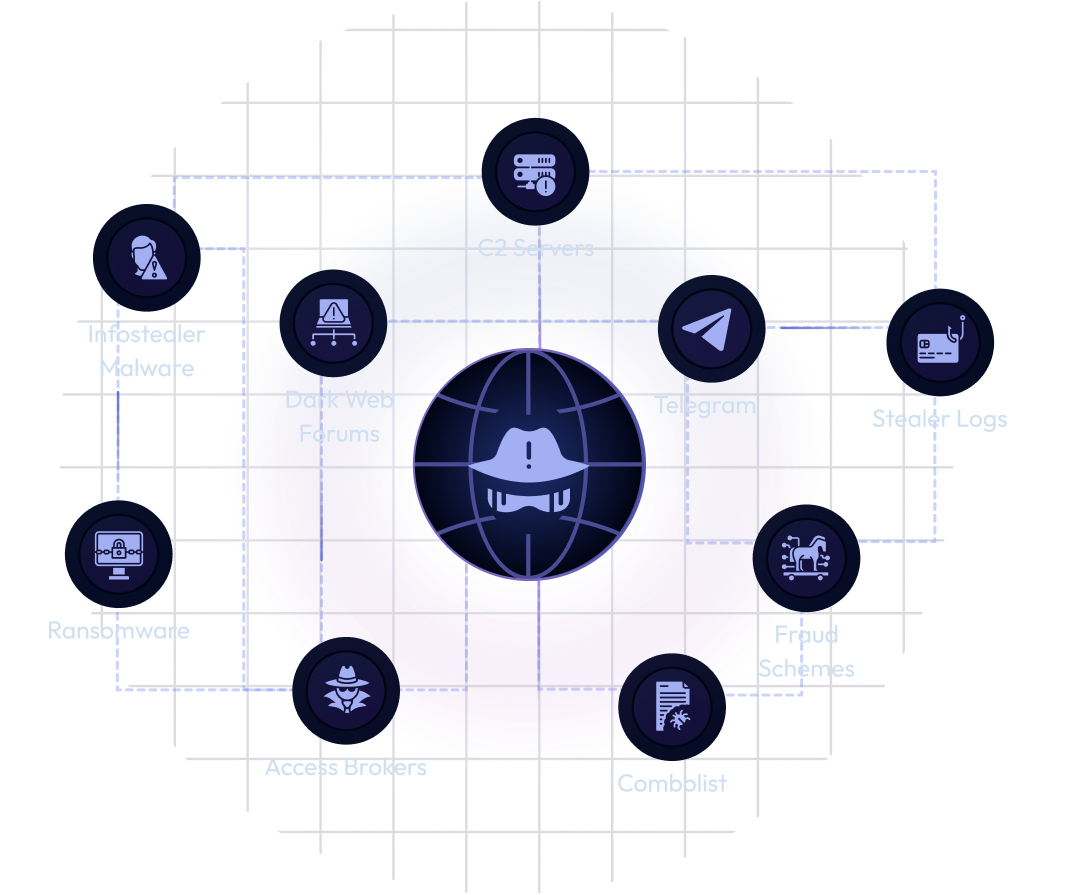
Flare continuously monitors dark web forums, Telegram channels, criminal marketplaces, and stealer log databases for stolen session cookies and credentials associated with your platform. Customers query the ASTP API by domain or URL. When Flare surfaces an exposure, your team receives an alert and can revoke the session, force a password reset, or trigger workflows through your existing SIEM or SOAR. Flare provides the intelligence. Your team executes the remediation.
Does Flare ASTP replace my existing fraud tools?
No. ASTP fills the gap upstream of existing tools. Behavioral analytics and payment fraud detection operate after a session is established. ITDR and IAM operate inside your environment. None have visibility into criminal markets before an attacker acts. ASTP is the intelligence layer that feeds signal into those tools before fraud occurs.
What do I need in place to act on ASTP intelligence?
Your team needs the ability to verify a session cookie’s validity and revoke it programmatically, or trigger forced password resets for affected accounts. ASTP integrates via API into fraud workflows, SIEM, and SOAR platforms. Teams without full automation can still act manually on high-priority alerts.
How is ASTP priced?
Based on total active user account volume on your platform, not employee headcount. A platform with 200 million daily active users is priced accordingly, because consumer exposure scale drives the scope of the problem ASTP solves.
Is ASTP part of the core Flare platform?
ASTP is a separately licensed add-on within the Flare platform: same interface, same underlying data, no second tool to learn. Organizations that start with ASTP have a simple path to Flare’s broader capabilities including dark web monitoring, brand protection, Telegram surveillance, and domain impersonation detection, all in one place.