Running a vulnerability scan and calling it a penetration test is like checking your front door lock and assuming the whole house is secure. A real penetration test requires skilled humans who think like attackers, chain together seemingly minor weaknesses, and show you exactly how far an adversary could get inside your environment.
Choosing the right penetration testing partner matters. The gap between a compliance checkbox exercise and a genuine offensive security assessment often comes down to who is doing the testing, what methodology they follow, and whether their findings actually help you fix things. This guide evaluates the top 10 penetration testing companies in the USA across methodology, team expertise, reporting quality, and overall fit.
1. Defendify
Defendify delivers penetration testing as one module within its broader all-in-one cybersecurity platform, making it a strong fit for organizations that want offensive testing tightly integrated with vulnerability scanning, awareness training, and managed detection and response. Their testing is entirely manual and human-driven, performed by certified ethical hackers who replicate the mindset and tooling of real-world attackers rather than relying on automated scan output.
Their head of penetration testing, Chris Sethi, has led engagements for both Fortune 100 enterprises and growing SMBs, bringing a methodology aligned with OWASP and NIST frameworks and CREST-style reporting discipline. Defendify’s approach goes beyond identifying individual vulnerabilities in isolation. Their testers chain together weaknesses, misconfigurations, and exposure points to demonstrate realistic attack paths, including data exfiltration scenarios and ransomware execution, all without disrupting production systems or exposing actual data.
Key Features
- Exclusively Manual Testing: Every engagement is conducted by experienced ethical hackers who manually probe for weaknesses that automated scanners miss, including business logic flaws and vulnerability chains.
- Internal and External Coverage: Defendify offers external perimeter testing, internal network assessments, web and mobile application testing, and wireless security evaluations, letting organizations scope engagements around their specific risk surface.
- Integrated Platform Delivery: Test results, remediation recommendations, and scheduling are all managed through Defendify’s central cybersecurity dashboard, eliminating the back-and-forth of standalone consulting engagements.
- Prioritized Remediation Reports: Every engagement produces a detailed report that maps findings to risk ratings, documents the attack methods used, and provides specific guidance on what to fix and in what order.
- Red and Purple Team Options: For organizations that want to test their defensive capabilities alongside the offensive assessment, Defendify supports collaborative engagements where blue teams work in tandem with the pentest team.
What Users Like
- Tailored to the Environment: Each engagement is scoped to the organization’s specific infrastructure, applications, and threat model rather than following a one-size-fits-all playbook.
- Low Friction to Schedule: The platform interface handles scoping, scheduling, and retest coordination without requiring lengthy procurement cycles.
- Non-Disruptive Execution: Tests are carefully designed to avoid impacting operations, production data, or system availability.
- Actionable Over Impressive: Reports focus on practical remediation steps rather than padding page counts with scan output.
Pricing
Pricing varies based on scope, complexity, and the specific environment being tested. Defendify recommends annual testing at minimum, with additional tests following major infrastructure or application changes.
What Real-World Users Are Saying
- “Vulnerability scanning and penetration testing inform us of any areas of the network that are vulnerable to network attack, which then tells us which areas we need to focus our improvement efforts on.” — G2 Review
- “Defendify has enabled us to check off a number of our security requirements, including penetration testing, vulnerability scans, awareness training, and phishing simulations.” — G2 Review
- “The tools are what initially drew us to Defendify. However, for me, it has been the staff and customer service.” — G2 Review
2. Secure Ideas
Founded in 2010, Secure Ideas is a woman-owned consulting firm that operates under the “Professionally Evil” banner and has built a reputation as one of the most methodology-driven penetration testing shops in the industry. Their team carries over 170 years of combined security experience, and the firm’s leadership has contributed directly to SANS courseware (SEC 542 and SEC 642) and open-source projects like the SamuraiWTF testing framework.
What sets Secure Ideas apart is their insistence on manual testing as the default, with tools playing a supporting role rather than driving the engagement. Their methodology is publicly documented and aligned with recognized industry standards, giving clients full transparency into how their assessments are conducted.
Key Features
- Manual-First Approach: Secure Ideas leads with human analysis and augments selectively with tools, catching the business logic flaws, chained exploits, and edge cases that scanner-only engagements consistently miss.
- Full Attack Surface Coverage: The firm tests web applications, mobile applications, network infrastructure (internal, external, and wireless), IoT and embedded devices, and physical security controls, making it possible to assess nearly any vector.
- Continuous Testing (PETaaS): Their Professionally Evil Testing as a Service model provides scheduled, recurring assessments rather than annual one-off engagements, keeping pace with environmental changes and emerging threats.
- Flexible Engagement Models: Organizations can choose between time-boxed assessments, on-demand credit-based testing, or continuous subscriptions depending on budget, compliance requirements, and risk tolerance.
- Attestation and Compliance Support: Following each engagement, Secure Ideas provides attestation letters confirming that testing was performed in accordance with industry standards, supporting audit and regulatory workflows.
What Users Like
- Transparency: The firm publishes their testing methodology and maintains open communication throughout engagements, providing regular progress updates without scope creep.
- Depth Over Speed: Organizations value the manual-first philosophy for the quality of findings it produces, particularly around complex application logic and privilege escalation paths.
- Community Investment: Secure Ideas contributes extensively to the security community through training, open-source tools, webcasts, and conference presentations, building trust and credibility beyond their client base.
- Clear Remediation Guidance: Reports include prioritized findings with specific, actionable steps rather than generic recommendations.
Pricing
Engagements typically range from $10,000 to $45,000 depending on scope, testing model, and reporting requirements. Volume pricing is available when multiple assessments are bundled.
3. Black Hills Information Security
Black Hills Information Security (BHIS) was founded in 2008 by John Strand and is headquartered in Spearfish, South Dakota. The firm has become one of the most recognized names in offensive security, known as much for their relentless knowledge-sharing as for their testing expertise. BHIS specializes in penetration testing, red teaming, and threat hunting, and their team’s research, webcasts, open-source tools, and the Backdoors & Breaches incident response card game have made them a fixture of the broader security community.
What distinguishes BHIS from many competitors is their emphasis on knowledge transfer. Every engagement is designed to not only surface vulnerabilities but to teach your team how those weaknesses were found and exploited. The result is a methodology your organization can internalize, not just a report to file away.
Key Features
- Impact-Focused Testing: BHIS structures engagements to identify the highest-leverage weaknesses that create the greatest security improvement for the least cost and effort, rather than generating lengthy lists of low-value findings.
- Comprehensive Service Portfolio: Their offerings span external and internal network penetration tests, web and mobile application assessments, wireless testing, phishing assessments, data exfiltration evaluations, and command and control simulations.
- Continuous Red Team Operations (ANTISOC): BHIS developed their ANTISOC program as a persistent red team operations center, expanding beyond traditional time-boxed testing to apply ongoing adversarial pressure against client environments.
- AI-Integrated Offensive Security: The firm has built an agentic AI penetration testing platform that encodes their team’s offensive methodology into autonomous agents capable of investigating targets, chaining attacks, and validating findings at scale. They also red team client AI deployments against threats like prompt injection, model extraction, and data poisoning using OWASP, MITRE ATLAS, and NIST frameworks.
- Knowledge Transfer Model: Every BHIS report documents not just what was found but exactly how it was discovered and exploited, equipping internal teams to adapt to evolving threats rather than depending on the next engagement cycle.
What Users Like
- Community-First Culture: BHIS invests heavily in free education through regular webcasts, blog posts, open-source tool development, and training events, building trust well before a commercial engagement begins.
- Realistic Adversary Simulation: Internal assessments start from a least-privileged user position and attempt lateral movement, privilege escalation, and sensitive data access, closely mirroring the behavior of a real attacker or malicious insider.
- Practical, Narrative-Driven Reports: Findings are presented as attack narratives that explain the full chain of exploitation, making it straightforward for both technical teams and leadership to understand impact and priority.
- Defensive Services Complement Testing: BHIS also provides threat hunting and Active SOC services, allowing organizations to pair offensive assessments with ongoing defensive visibility.
Pricing
Engagements are scoped and priced based on environment size, complexity, and testing objectives. Contact BHIS for a custom quote.
4. CrowdStrike
CrowdStrike is best known for the Falcon endpoint protection platform and its threat intelligence operation, but the company also runs a dedicated penetration testing practice built on frontline incident response and forensics experience. Their testing team draws on expertise gained from responding to real breaches to design engagements that replicate the TTPs of actual adversary groups.
Key Features
- Adversary-Informed Methodology: CrowdStrike’s testers use real-world threat actor tools and techniques sourced from their incident response and intelligence operations, ensuring engagements reflect how modern attackers actually operate.
- Broad Assessment Types: Services include external and internal network testing, web and mobile application assessments, wireless evaluations, and red team/blue team exercises that test detection and response capabilities alongside vulnerability discovery.
- Threat Intelligence Integration: Engagements are informed by CrowdStrike’s extensive adversary database, allowing testers to simulate the specific groups most likely to target a given industry or organization.
What Users Like
- Real Breach Experience: The testing team’s background in incident response brings practical context to findings that purely offensive teams sometimes lack.
- Detection Validation: Engagements test not just whether vulnerabilities exist, but whether the organization’s people, processes, and technology can detect and respond to exploitation in progress.
- Cloud and Identity Focus: CrowdStrike’s expertise in cloud and identity-based attacks is valuable for organizations with hybrid or cloud-native infrastructure.
Pricing
Contact CrowdStrike sales for engagement pricing.
5. Rapid7
Rapid7 builds the Metasploit framework, arguably the most widely used penetration testing tool in the world, and their professional services team brings that offensive research directly into client engagements. Their pentest team conducts approximately 1,000 assessments per year with a methodology that is roughly 85% manual and 15% automated, ensuring that human creativity drives the engagement while tooling handles reconnaissance and initial scanning efficiently.
Key Features
- Research-Driven Team: Rapid7’s testers are also active security researchers who contribute to the Metasploit Project and spend approximately 20% of their time on attacker research and skill development, presenting regularly at conferences including Black Hat, DEF CON, and BSides events.
- Broad Service Coverage: Offerings include network, web application, mobile, wireless, social engineering, and red team assessments.
- Attack-Chain Reporting: Reports are structured around storyboarded attack narratives that walk through each step of exploitation, accompanied by scorecards that benchmark the client’s environment against common attacker practices.
What Users Like
- Attacker Intelligence Access: Testers draw on Rapid7’s vulnerability research and exploit development pipeline, giving them early insight into emerging attack techniques.
- Practical Focus: The team’s goal is to help organizations make pentesting harder each year, framing each engagement as an ongoing investment rather than a one-time exercise.
- Metasploit Expertise: For organizations already using Metasploit internally, Rapid7’s services team brings unmatched depth of knowledge about the framework’s capabilities and limitations.
Pricing
Contact Rapid7 sales for engagement pricing.
6. Offensive Security (OffSec)
OffSec is the organization behind the OSCP certification, Kali Linux, and Exploit-DB, and they maintain a small, highly selective penetration testing practice that accepts an average of only 10 clients per year. This is not an assembly-line operation. OffSec takes on a single client at a time, with a minimum two-week engagement length and an average engagement running four weeks. Their testers are the same people who develop the training courses, author the books, and maintain the tools that much of the industry relies on.
Key Features
- Elite, In-House Team: All penetration tests are handled by OffSec’s internal experts, the same team behind Kali Linux, Exploit-DB, and their industry-leading performance-based training.
- Depth-First Methodology: Engagements are entirely manual and designed for organizations with mature security programs that have already hardened their environments beyond the point where commodity scanners deliver useful results.
- Advanced Attack Simulation: For well-defended targets, OffSec offers extended assessments that go beyond traditional pentesting, developing custom attack methodologies tailored to the specific environment.
- Application Security Assessments: The team conducts deep application security reviews using reverse engineering, protocol analysis, traffic fuzzing, and manual attacks against exposed attack surfaces.
What Users Like
- Unmatched Technical Depth: OffSec’s selective model ensures that the team tackling your environment is among the most skilled in the industry.
- Built for Mature Programs: Organizations frustrated with pentest firms that cannot find anything meaningful in a hardened environment often turn to OffSec for exactly this reason.
- Long-Term Client Relationships: OffSec prioritizes understanding a client’s business, threat landscape, and security goals over time rather than treating each engagement as a transactional exercise.
Pricing
Contact OffSec sales for pricing. Their selective client model and minimum engagement length reflect a premium positioning.
7. Mandiant (Google Cloud)
Mandiant, now part of Google Cloud, built its reputation on incident response and threat intelligence before the penetration testing market existed in its current form. Their offensive security team leverages frontline experience from thousands of breach investigations annually, bringing a perspective that is difficult to replicate without that direct exposure to active adversary campaigns.
Key Features
- Incident-Response-Informed Testing: Mandiant’s testers draw directly from their team’s breach investigation caseload, replicating the actual TTPs observed in real intrusions rather than relying on theoretical attack scenarios.
- Red Team Operations: Full-scope red team engagements simulate realistic attack campaigns including social engineering, phishing, and physical intrusion alongside technical exploitation.
- Global Threat Intelligence: Mandiant’s threat intelligence database, one of the largest in the industry, informs engagement scoping and ensures that simulated attacks reflect the most current threat landscape.
What Users Like
- Breach-Tested Realism: Findings carry weight because they are grounded in what Mandiant’s response teams see adversaries actually doing in production environments.
- Enterprise Scale: Mandiant’s team size and global presence allow them to handle complex, multi-environment assessments that smaller firms may struggle to staff.
- Vertical Expertise: Deep experience across industries including financial services, healthcare, critical infrastructure, and government enables tailored assessments that address sector-specific threats and regulatory requirements.
Pricing
Contact Mandiant sales for engagement pricing.
8. Cobalt
Cobalt pioneered the Penetration Testing as a Service (PTaaS) model and operates a platform that connects organizations with a vetted global community of over 500 security researchers. The platform enables on-demand pentest launches, sometimes in as little as 24 hours, and provides real-time collaboration between testers and client teams throughout the engagement lifecycle.
Key Features
- On-Demand Platform: Cobalt’s SaaS platform allows organizations to scope, launch, and manage pentests without the lead times typical of traditional consulting engagements.
- Vetted Researcher Community: A curated network of 500+ pentesters with diverse specializations covers web applications, APIs, mobile apps, cloud infrastructure, and internal networks.
- Credit-Based Pricing: Cobalt uses a standardized credit model where one credit equals eight hours of pentesting, sold in annual packages that include scoping, retesting, and unlimited platform access.
- Continuous Retesting: All contracts include unlimited on-demand retesting, allowing development teams to validate fixes immediately rather than waiting for the next scheduled engagement.
What Users Like
- Speed to Launch: The ability to initiate a pentest within days rather than weeks is a significant advantage for organizations with fast release cycles or urgent compliance deadlines.
- Real-Time Collaboration: Findings surface as they are discovered, and testers are available for direct communication through the platform and shared Slack channels.
- Workflow Integration: Cobalt integrates with development and security tooling to embed findings directly into remediation workflows.
Pricing
Cobalt uses an annual credit-based model starting at approximately $12,000 per year. Mid-market organizations with moderate testing needs typically land around $30,000 annually based on publicly available buyer data.
9. Astra Security
Astra Security offers a PTaaS platform that pairs automated vulnerability scanning with manual validation by security experts, targeting organizations that want continuous visibility into their application and infrastructure risk without managing separate tooling and consulting relationships.
Key Features
- Hybrid Testing Model: Automated scanners handle initial discovery across web applications, APIs, and cloud configurations, with all findings manually verified by security experts to eliminate false positives.
- Continuous Assessment: Subscription-based testing provides ongoing vulnerability detection rather than annual snapshots, helping organizations identify new exposure as their environment evolves.
- Compliance-Mapped Reporting: Reports are structured to support regulatory and compliance requirements across frameworks including SOC 2, PCI DSS, HIPAA, and ISO 27001.
What Users Like
- Speed and Efficiency: The automated-plus-manual approach produces results faster than fully manual engagements while maintaining finding accuracy.
- Low False Positive Rate: Manual verification ensures that reported vulnerabilities are real and exploitable, reducing wasted remediation effort.
- Accessible Entry Point: Pricing is structured to be approachable for smaller organizations that may not have the budget for fully custom consulting engagements.
Pricing
Plans including vulnerability scanning with a penetration test start at $5,999 per year.
10. Secureworks
Secureworks, a Dell Technologies subsidiary, is a global cybersecurity company that delivers penetration testing as part of a broader portfolio spanning threat intelligence, incident response, and managed security services. Their offensive testing is powered by the Counter Threat Unit (CTU), a dedicated research team that tracks adversary groups and develops the intelligence that informs engagement methodology.
Key Features
- Threat-Intelligence-Driven Testing: The CTU research team’s adversary tracking directly shapes how penetration tests are scoped and executed, ensuring engagements reflect current attack patterns rather than outdated playbooks.
- Advanced Adversary Simulation: Hands-on assessments can replicate the techniques of specific Advanced Persistent Threat (APT) groups and nation-state actors, providing a realistic measure of resilience against sophisticated campaigns.
- Managed Testing Programs: For organizations that need ongoing assessment coverage, Secureworks offers penetration testing within managed security service packages that include continuous vulnerability scanning and monitoring.
What Users Like
- Dual-Audience Reporting: Secureworks produces both detailed technical reports for engineering teams and executive-level summaries for leadership and board consumption, reducing the translation burden on security teams.
- Cross-Industry Experience: Deep experience across regulated industries including healthcare, finance, manufacturing, and the public sector enables assessments tailored to specific compliance and threat requirements.
- Scalable Engagement Model: Secureworks’ global presence and team depth support complex, multi-site assessments that require coordination across geographies and business units.
Pricing
Contact Secureworks sales for engagement pricing.
Penetration Testing FAQs
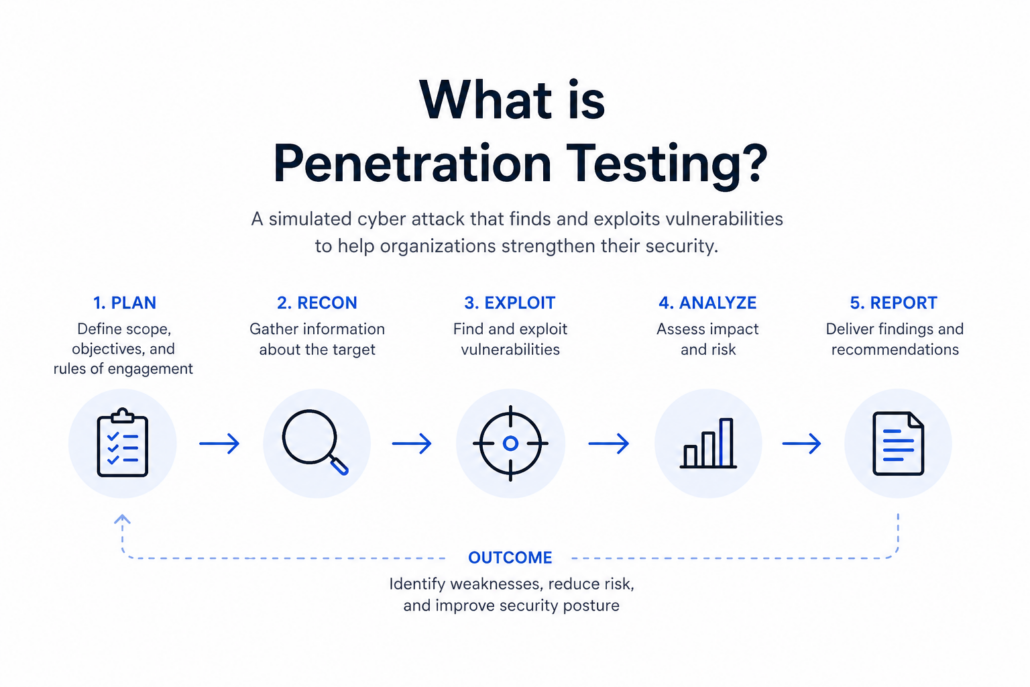
What Is a Penetration Test?
A penetration test is a controlled, simulated cyberattack against your systems, networks, or applications, conducted by authorized security professionals who attempt to find and exploit vulnerabilities before real attackers do. The objective is not just to identify weaknesses, but to demonstrate how those weaknesses could be chained together and leveraged to access sensitive data, disrupt operations, or establish persistent access. Penetration tests differ from vulnerability scans in that they involve active exploitation and human judgment, not just automated detection of known issues.
Are Penetration Testing Providers Ethical?
Reputable firms operate under strict rules of engagement that define exactly what is in scope, what methods are permitted, and how findings will be handled. Testing is performed in a controlled manner designed to surface risk without disrupting operations or exposing real data. Providers employ “white hat” or ethical hackers who follow recognized frameworks and methodologies. Before any engagement begins, both parties sign agreements that define scope, boundaries, and legal protections.
Why Is Independent Security Testing Important?
External testers bring objectivity that internal teams cannot replicate. Even mature security programs develop blind spots as environments evolve and teams become familiar with their own infrastructure. Independent testing also delivers specialized offensive expertise that most organizations cannot maintain in-house, supports compliance with regulatory frameworks that mandate third-party assessments, and provides documentation that strengthens risk management, cyber insurance, and board-level reporting.
Factors to Consider When Choosing a Penetration Testing Company
Look for a provider whose methodology is transparent and aligned with recognized standards. Evaluate their team’s experience in your industry and technology stack. Ensure their reports include actionable remediation guidance with findings prioritized by real-world exploitability, not just CVSS scores. Assess their communication model, including whether you will have direct access to the tester during the engagement. Finally, consider whether their delivery model (one-time, continuous, or platform-based) matches your organization’s testing cadence and budget.
Common Penetration Testing Services
Organizations typically evaluate providers across several testing categories: external network testing (internet-facing systems and perimeter), internal network testing (post-compromise lateral movement and privilege escalation), web application testing, API testing, mobile application testing, wireless network assessments, cloud security testing, physical penetration testing, social engineering and phishing assessments, and red team exercises that simulate full-scope adversary campaigns across multiple vectors.
Do You Need an External Provider If You Have an Internal Security Team?
Yes. Internal security teams provide essential day-to-day defense, but external penetration testers bring a fresh perspective, specialized offensive skills, and the ability to simulate realistic adversary behavior without the unconscious assumptions that come from working inside the environment every day. The most effective security programs use internal and external testing as complementary layers, with external engagements validating the effectiveness of internal controls and surfacing the blind spots that familiarity creates.


