By Tammy Harper, Senior Threat Intelligence Researcher
A sophisticated new macOS malware called ATLAS has emerged on underground forums, positioning itself as a premium infostealer framework rather than a commodity threat. Currently in pre-release with a commercial launch scheduled for December 31th, 2025, ATLAS represents a significant evolution in mac malware capabilities, combining browser credential theft, cryptocurrency wallet extraction, and persistent reverse shell access into a single polished package.
What is ATLAS Stealer?
ATLAS is a newly advertised macOS-focused stealer malware marketed toward operators conducting targeted phishing and click-fix campaigns against Mac users. Unlike commodity stealers that focus on bulk credential harvesting, ATLAS presents itself as a modular malware-as-a-service (MaaS) platform with features typically associated with more sophisticated post-exploitation frameworks.
The stealer malware offers a comprehensive feature set including a polished web panel, flexible exfiltration infrastructure using legitimate cloud services, geo-blocking capabilities, encrypted reverse shell access, and native support for both Intel and Apple Silicon systems. This cross-architecture compatibility is particularly notable as more organizations adopt M-series Macs.
With tiered pricing reaching up to $50,000 for a white-label enterprise license, ATLAS is clearly targeting professional cybercriminal operators rather than opportunistic attackers.
Browser and Credential Theft Capabilities
ATLAS supports extraction of credentials, cookies, autofill data, browsing history, and session artifacts from an extensive list of browsers. This breadth of coverage suggests the malware is designed to capture authenticated sessions, enabling account takeover without immediate credential reuse.
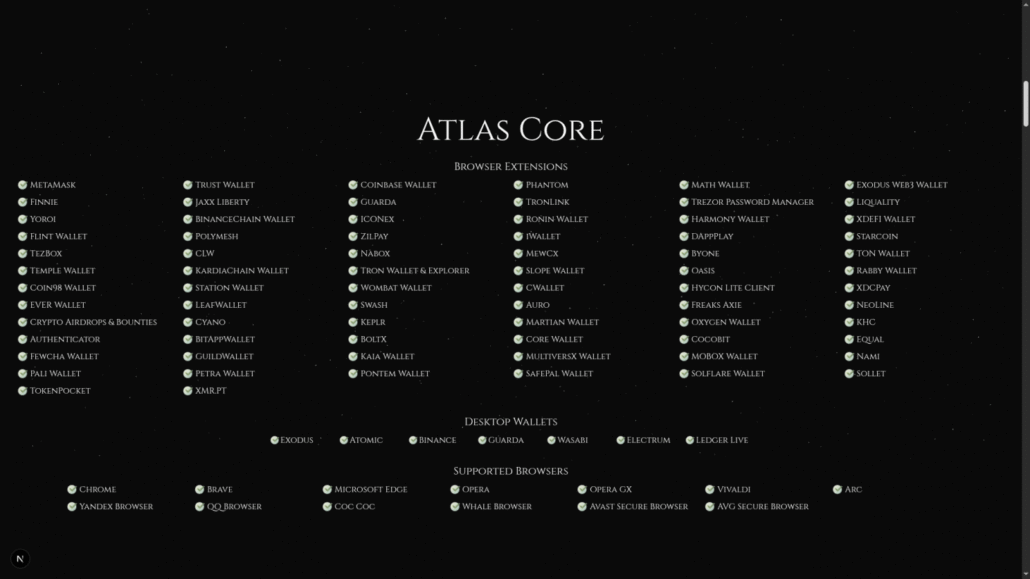
ATLAS supports credential theft from dozens of browsers and over 70 cryptocurrency wallet extensions
Supported browsers include Chrome-based browsers (Chrome, Brave, Edge, Opera, Opera GX, Vivaldi, Arc), privacy and regional browsers (Yandex, QQ Browser, Cốc Cốc, Whale), and security-branded browsers (Avast Secure Browser, AVG Secure Browser).
Cryptocurrency Wallet Targeting
One of the most significant capabilities of this macOS malware is its extensive support for cryptocurrency wallet theft. ATLAS targets both browser-based extensions and desktop wallet applications, covering the majority of popular crypto wallets used by retail and professional traders.
Browser Extension Wallets: MetaMask, Phantom, Trust Wallet, Coinbase Wallet, Exodus, Atomic, Binance Wallet, and dozens of others including Solana-specific wallets (Sollet, Solflare, Slope).
Desktop Wallets: Exodus, Atomic, Binance, Guarda, Wasabi, Electrum, and Ledger Live.
Hardware Wallet Interfaces: ATLAS also targets hardware wallet managers including Ledger Live and Trezor Password Manager, which could expose recovery phrases or transaction signing capabilities.
macOS Keychain Attacks
ATLAS explicitly advertises Keychain phishing and master password handling capabilities, targeting one of macOS’s core security features. The malware can prompt users for Keychain credentials through social engineering dialogs, dump stored secrets where system permissions allow, and attempt to decrypt locally stored credentials.
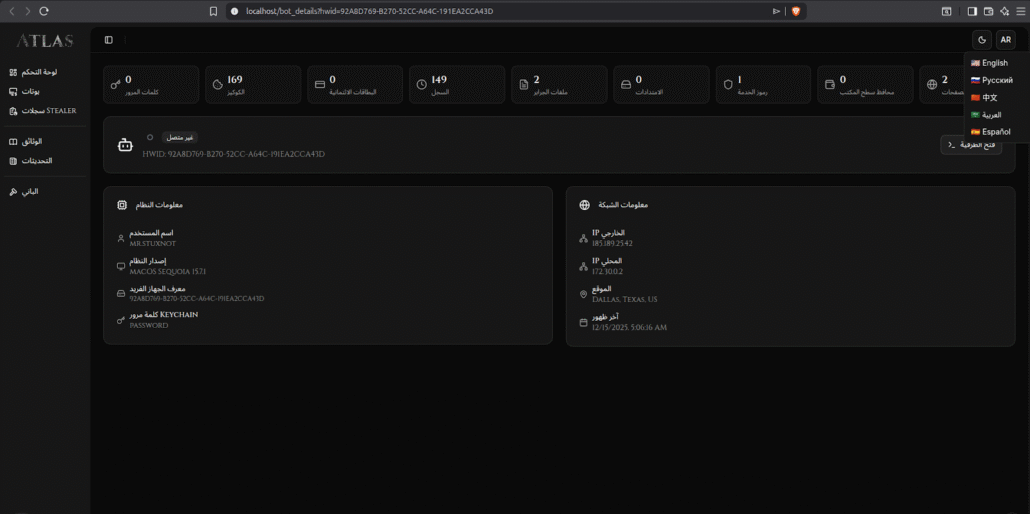
ATLAS panel showing captured victim details including Keychain password and system information
Encrypted Reverse Shell for Persistent Access
What distinguishes ATLAS from typical stealer malware is its end-to-end encrypted asynchronous reverse shell capability. This feature blurs the line between infostealer and post-exploitation framework, enabling operators to maintain persistent access beyond the initial credential theft.
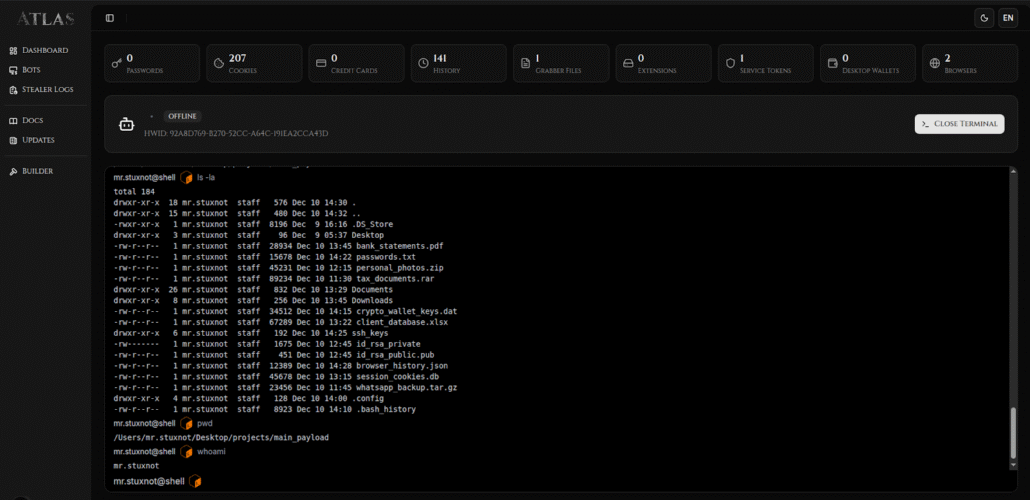
ATLAS includes an embedded reverse shell allowing operators to browse victim file systems and execute commands
The reverse shell enables live system enumeration, manual data collection beyond automated theft, arbitrary command execution, and long-term access if persistence mechanisms are maintained. This design choice aligns ATLAS more closely with hands-on-keyboard campaigns than automated botnet-style operations.
Cloud-Based Exfiltration Infrastructure
ATLAS supports indirect exfiltration via legitimate cloud services including Dropbox, Uploadcare, and Gyazo. By abusing trusted platforms for data exfiltration, operators can bypass network security controls that might block connections to known malicious infrastructure.
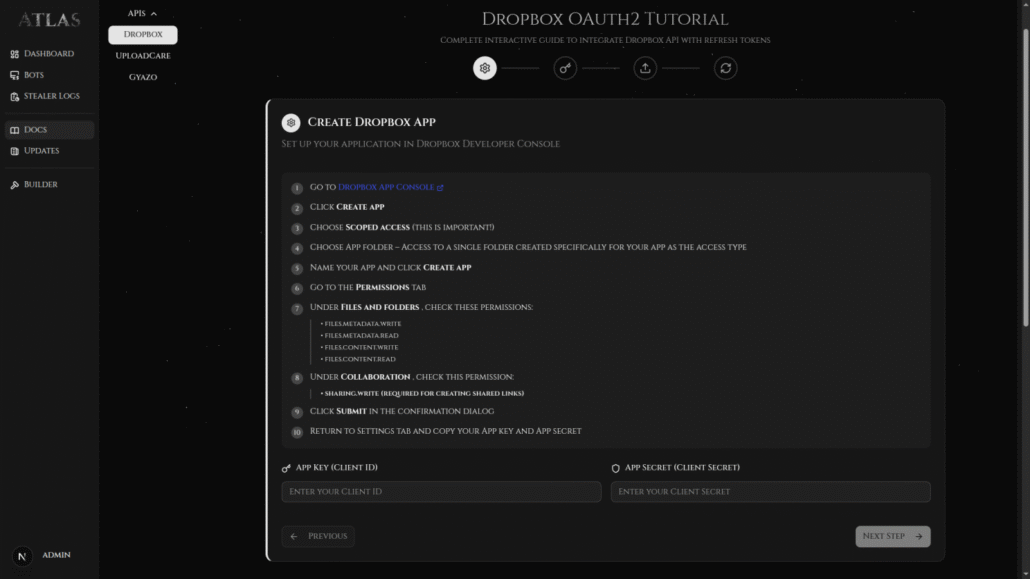
ATLAS includes step-by-step OAuth2 setup guides for abusing Dropbox as an exfiltration channel
The panel includes detailed OAuth2 setup guides, lowering the technical barrier for operators unfamiliar with API abuse. This approach to exfiltration makes detection more challenging since traffic to Dropbox, Uploadcare, and similar services is typically allowed in enterprise environments.
Geo-Blocking and Target Filtering
ATLAS includes built-in geo-blocking controls that allow operators to exclude entire regions or country groupings from targeting. Available filters include CIS (Commonwealth of Independent States), BRICS, NATO, G7, and ASEAN nation groupings.
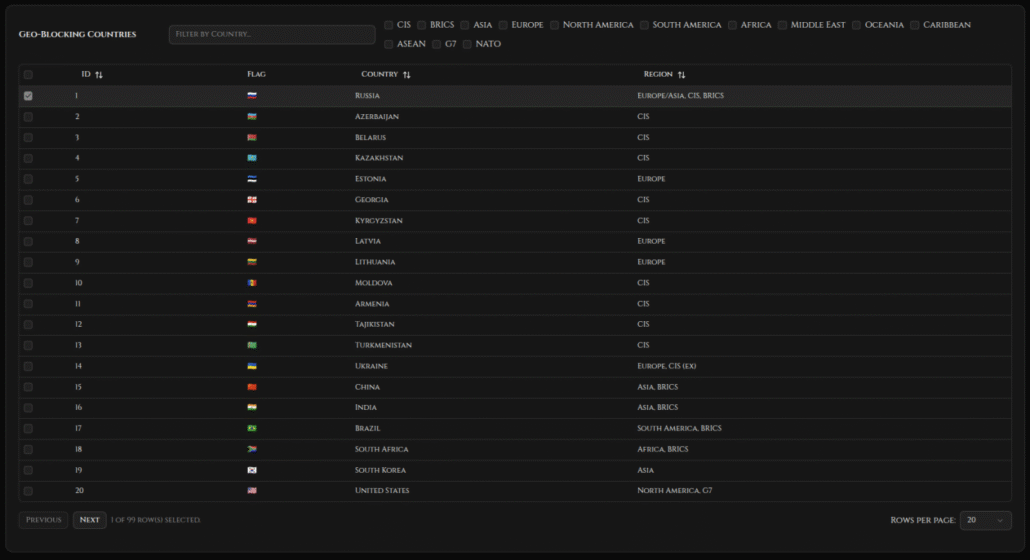
ATLAS allows operators to exclude specific countries or regional groupings from targeting
The presence of CIS geo-blocking options and Russian language support in the panel strongly suggests Eastern European origins for the malware developers. This pattern of excluding CIS countries from targeting is common among Russian-speaking cybercriminal groups to avoid domestic law enforcement attention.
Click-Fix Delivery Mechanism
ATLAS ships with a polymorphic Bash dropper designed for use in click-fix and social engineering campaigns. The builder automatically generates encrypted payloads suitable for deployment via fake error dialogs, CAPTCHA bypass prompts, “fix your system” phishing lures, and fake software update notifications.
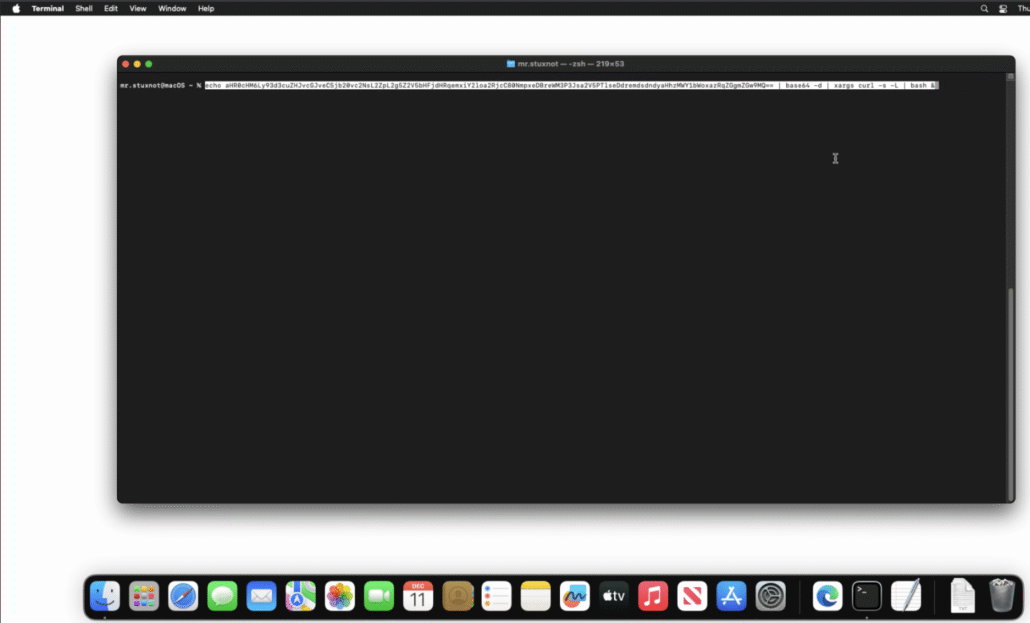
ATLAS uses polymorphic Bash droppers for click-fix style infection chains
Click-fix attacks have become increasingly common against macOS users, typically involving fake browser notifications or system alerts that instruct users to copy and paste terminal commands. The polymorphic nature of ATLAS droppers means each generated payload is unique, complicating signature-based detection.
Operator Panel and User Experience
The ATLAS web panel is unusually polished for macOS stealer malware, featuring victim dashboards with HWID tracking, system and network metadata, browser and wallet statistics, embedded terminal access for the reverse shell, and modular documentation for API integrations.
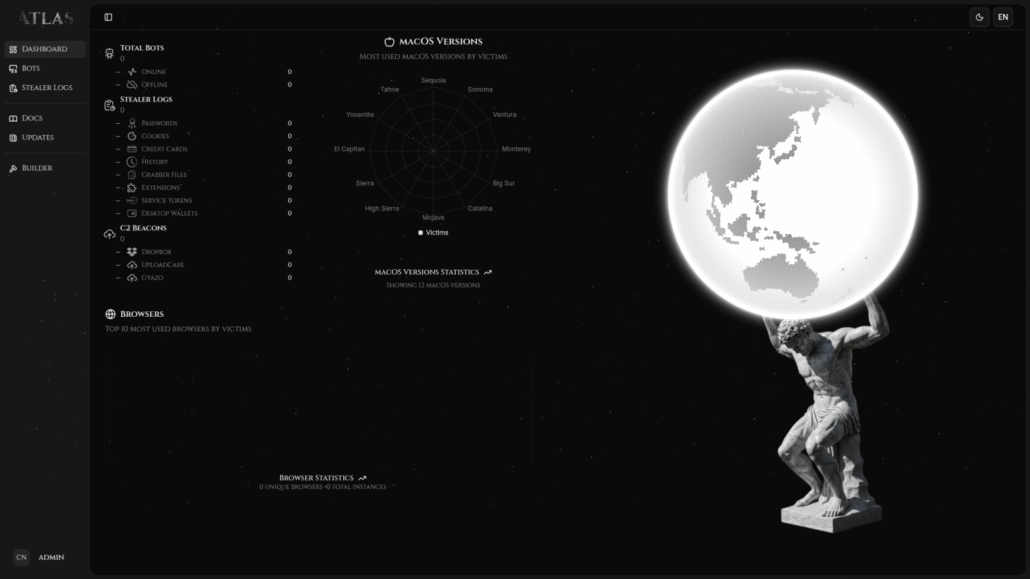
ATLAS main dashboard showing victim statistics, macOS version distribution, and exfiltration channel status
The dashboard displays macOS version statistics showing which Apple operating system versions are most represented among victims. The panel supports multiple languages including English, Russian, Chinese, Arabic, and Spanish, indicating the developers are marketing to a global operator base.
Pricing and Licensing Model
ATLAS operates under a tiered malware-as-a-service pricing model with three license options designed for different operator scales:
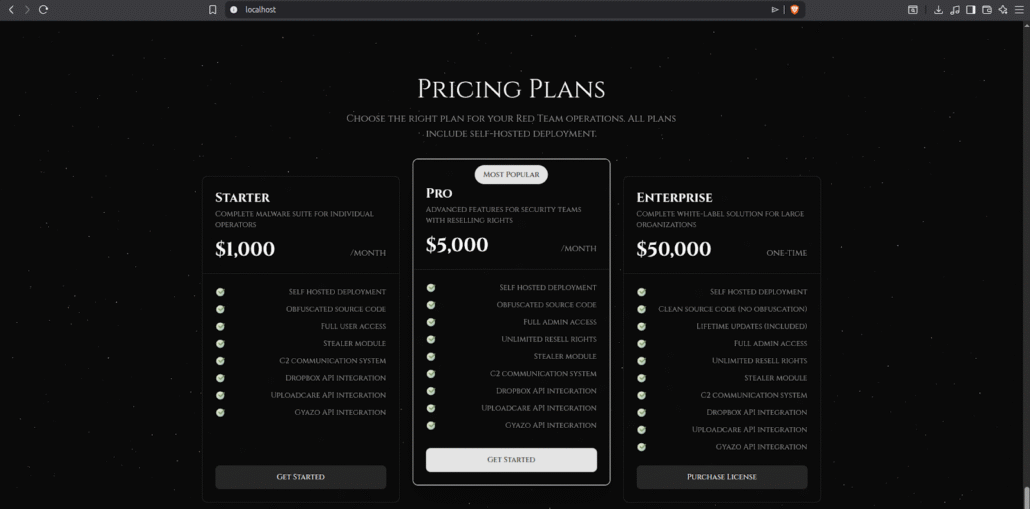
ATLAS pricing ranges from $1,000/month for individual operators to $50,000 for white-label enterprise licenses
- Starter ($1,000/month): Complete malware suite for individual operators. Includes self-hosted deployment, obfuscated source code, stealer module, C2 communication system, and API integrations for Dropbox, Uploadcare, and Gyazo.
- Pro ($5,000/month): Advanced features for “security teams” with unlimited reselling rights. Marked as “Most Popular” in the panel, suggesting this tier sees the most adoption among professional operators.
- Enterprise ($50,000 one-time): Complete white-label solution for large organizations. Includes clean (non-obfuscated) source code and lifetime updates, enabling buyers to rebrand and modify the malware as their own product.
Threat Intelligence Implications
ATLAS represents a significant maturation of the macOS malware ecosystem. Security teams should consider several implications:
- Apple Silicon Targeting: Native support for M-series Macs indicates threat actors are keeping pace with Apple’s hardware transition. Organizations deploying Apple Silicon should not assume they are protected by platform novelty.
- Cryptocurrency Focus: The extensive wallet support suggests operators will heavily target individuals and organizations with cryptocurrency exposure. Finance teams and developers working with crypto should be prioritized for security awareness training.
- Click-Fix Campaign Increase: The built-in support for click-fix style attacks indicates this delivery method remains effective against Mac users. User education about terminal command social engineering is essential.
- Cloud Service Abuse: Detection teams should monitor for unusual patterns in Dropbox, Uploadcare, and Gyazo traffic, particularly large uploads or frequent API calls from endpoints not normally using these services.
Recommendations for Security Teams
Organizations with Mac endpoints should implement the following controls to defend against ATLAS and similar macOS stealer malware:
1. User Education: Train users to recognize click-fix attacks and never paste commands into Terminal from untrusted sources.
2. Endpoint Detection: Deploy EDR solutions with macOS coverage that can detect suspicious Bash execution patterns and unauthorized Keychain access attempts.
3. Network Monitoring: Monitor for anomalous data transfers to cloud storage APIs, particularly Dropbox and similar services.
4. Browser Extension Auditing: Regularly audit browser extensions, especially cryptocurrency wallets, for unauthorized modifications or suspicious permissions.
5. Hardware Wallet Policies: For high-value cryptocurrency operations, require hardware wallets with air-gapped signing rather than browser extensions.
What Security Teams Can Keep in Mind About ATLAS
ATLAS represents a new tier of macOS malware sophistication, combining traditional infostealer capabilities with post-exploitation features typically seen in more advanced threat actor toolkits. The premium pricing, polished interface, and comprehensive feature set indicate this is a professionally developed malware-as-a-service platform targeting serious cybercriminal operators.
With the commercial launch scheduled for December 31th, 2025, security teams should prepare for increased infostealer activity targeting Mac environments. The combination of cryptocurrency wallet theft, browser credential harvesting, and persistent reverse shell access makes ATLAS a significant threat to organizations with Mac-heavy environments, particularly those in financial services, technology, and cryptocurrency sectors.
Organizations should use this pre-launch window to review their macOS security posture, update user awareness training for click-fix attacks, and ensure their endpoint detection capabilities extend to Apple Silicon systems.
Monitor for External Threats with Flare
The Flare Threat Exposure Management solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors. Our platform automatically scans the clear & dark web and prominent threat actor communities 24/7 to discover unknown events, prioritize risks, and deliver actionable intelligence you can use instantly to improve security.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. See what external threats are exposed for your organization by signing up for our free trial.





