By Tammy Harper, Senior Threat Intelligence Researcher
A new ransomware-as-a-service (RaaS) operation called Cry0 has emerged, introducing a novel approach to extortion infrastructure that leverages blockchain technology for resilience against law enforcement takedowns. While this ransomware group has yet to publicly claim any victims, their technical claims and operational model warrant attention from security teams monitoring the RaaS ransomware ecosystem.
What is Cry0 Ransomware?
Cry0 is a newly identified ransomware operation that has begun recruiting affiliates through underground cybercrime forums. The group claims their ransomware payload is written in Rust from scratch, featuring custom asymmetric and symmetric encryption. According to their promotional materials, the encryption implementation is approximately 40% faster on average compared to ChaCha20, though this claim remains unverified by independent researchers.
The group operates a data leak site (DLS) accessible via Tor at: cryoblogedawivdcknyd4jsjxkrx3xrqqltxla6wwjjnzm3f3jaxjzqd.onion
The group communicates in both Russian and English, suggesting operators with Eastern European ties, common among major ransomware groups.
Cry0 Data Leak Site Analysis
Cry0’s data leak site does not currently display any victims, suggesting the operation is in its early stages or still refining capabilities before conducting attacks.
Cry0’s data leak site currently shows no victims
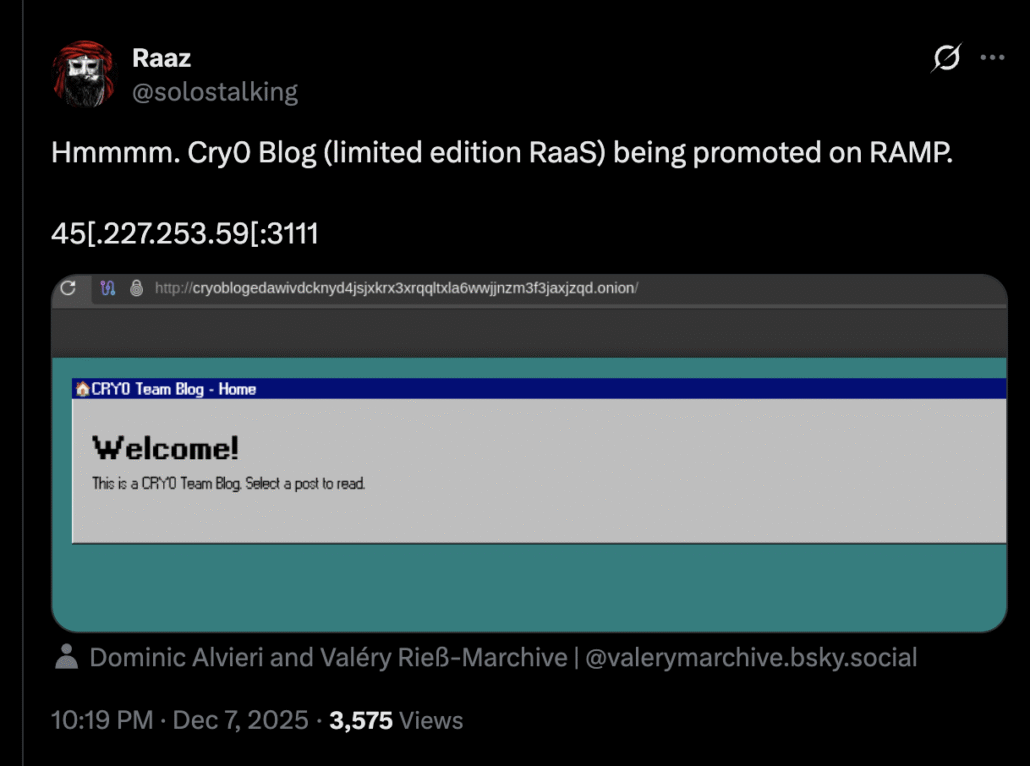
When the operation initially launched, the DLS was available via clearnet at IP address 45.227.253.59:3111, according to security researcher RaaZ. The group has since moved exclusively to Tor-based infrastructure for operational security.
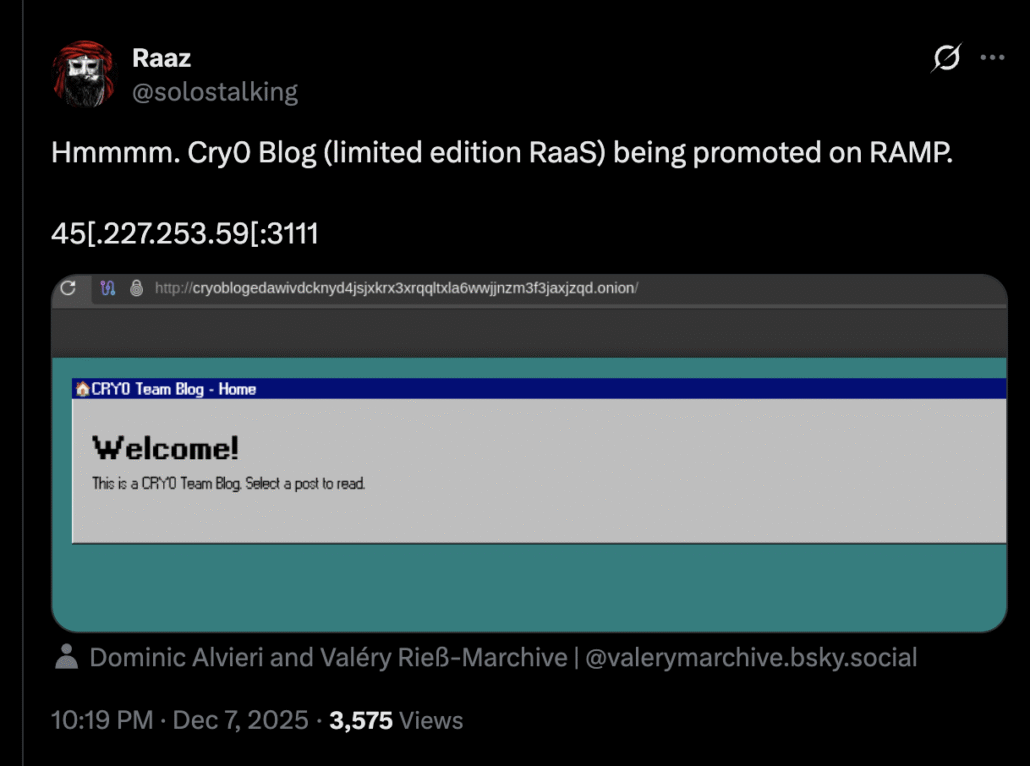
Security researcher RaaZ documented Cry0’s initial promotion on the RAMP cybercrime forum
The Cry0 Ransomware Affiliate Program
Like other ransomware-as-a-service operations, Cry0 employs an affiliate model. However, they have implemented a cryptographic trust system designed to prevent disputes between operators and partners.
Here is how the affiliate program works: Partners generate their own key pair on their local machine. Their public key is then used for build generation. This setup creates a trust model where neither party can act unilaterally. Cry0 cannot run the decryptor without the partner’s private key, but affiliates also cannot defraud Cry0 because their private key alone is insufficient. The decryptor requires two private keys: one from Cry0’s end and one from the partner’s end.
The revenue split is currently set at 90/10, with 90% of the ransom payment going to the affiliate and 10% going to the Cry0 operators. This split is significantly more favorable to affiliates than many competing RaaS programs, which typically offer 70/30 or 80/20 splits. The generous terms are likely an incentive to attract experienced ransomware operators to the new platform.
Blockchain-Based Double Extortion Infrastructure
Perhaps the most notable aspect of Cry0’s operation is their claimed approach to hosting extortion infrastructure. The group has developed what they describe as an “unerasable website” for double extortion ransomware operations that remains accessible through standard web browsers.
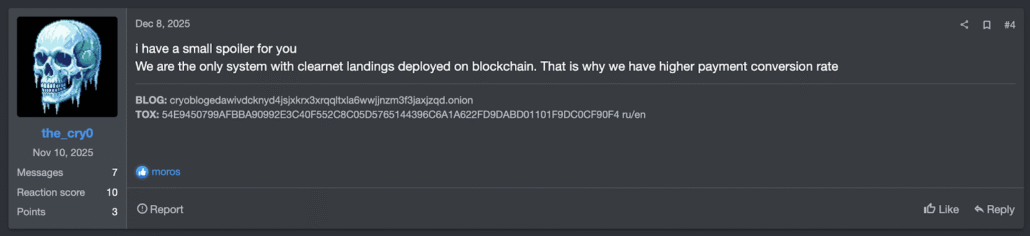
Cry0 operators advertise their blockchain-based payment infrastructure on cybercrime forums
Traditional ransomware groups face a dilemma when hosting payment portals. Clear web sites can be seized by law enforcement relatively quickly. Tor-based sites, while more resilient, present usability challenges for victims who may be unfamiliar with accessing .onion addresses. Both factors can reduce ransomware payment rates.
Cry0 claims to solve this problem by storing actual website files on a blockchain or decentralized network, creating a permanent repository that no single authority can delete or control. Victims receive a standard clear web link that acts as a gateway to these decentralized files. From the victim’s perspective, the site looks and functions like any normal webpage in Chrome or Safari.
How the Blockchain Extortion Infrastructure Works
The infrastructure operates through three components:
1. Decentralized Storage: The attackers upload their payment website files (HTML, images, chat scripts) to a decentralized network like IPFS (InterPlanetary File System) or Arweave. This gives the files a unique cryptographic fingerprint (hash) rather than a traditional location-based address.
2. Gateway Links: Victims receive what appears to be a normal link (such as https://payment-portal.com/…). This domain functions as a proxy or gateway. It does not host the files directly; instead, it requests content from the decentralized network that matches the specified fingerprint.
3. Resilient Backend: If authorities seize a gateway domain, the attackers maintain backup domains ready for deployment. They can simply email victims a new link while the backend infrastructure (payment processing, chat logs, proof of stolen files) remains untouched on the blockchain because it is immutable.
Evidence of Fabricated Claims
Despite the technical sophistication of their described infrastructure, there are significant reasons to approach Cry0’s claims with skepticism.
In their RaaS advertisement, the group displays what appears to be a ransom negotiation with Honeywell Manufacturing, allegedly resulting in a $12 million DAI payment.
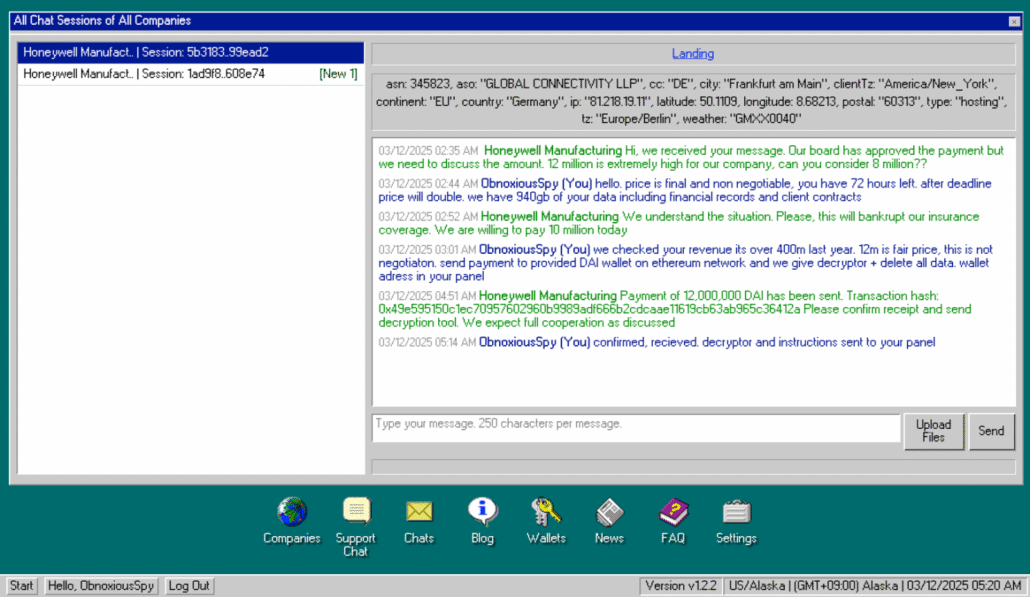
Cry0’s advertisement shows an alleged negotiation with Honeywell Manufacturing
However, the Ethereum transaction hash they provide does not exist on the blockchain:
0x49e595150c1ec70957602960b9989adf666b2cdcaae11619cb63ab965c36412a
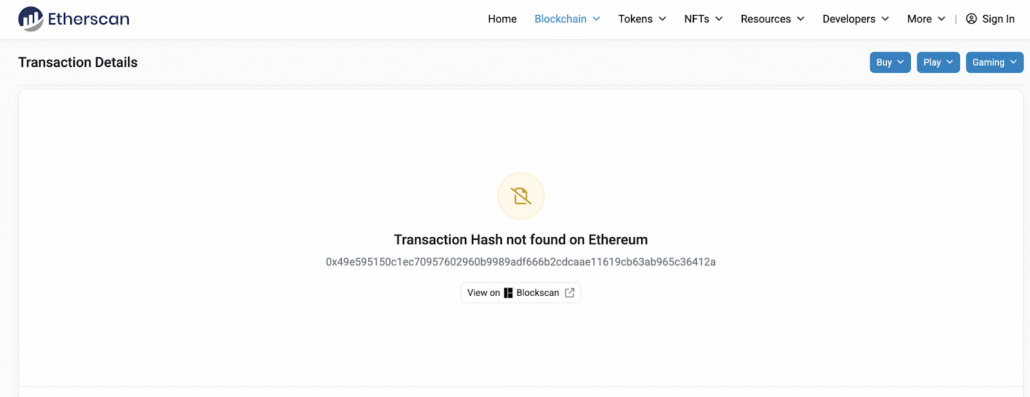
Etherscan confirms the alleged transaction does not exist on the Ethereum blockchain
This suggests the negotiation screenshot was fabricated to lend credibility to the operation. It is not uncommon for new RaaS operators to exaggerate their track record to attract affiliates, but this level of fabrication indicates the group may be less capable than their marketing suggests.
The group’s choice of DAI (a decentralized stablecoin pegged to $1.00 USD) over Bitcoin or Monero is notable. Unlike centralized stablecoins such as USDC or USDT, which are backed by fiat reserves, DAI is backed by other cryptocurrencies locked in smart contracts on Ethereum. This choice could indicate an attempt to reduce payment volatility for victims or could be part of a broader money laundering strategy.
Ransomware Threat Intelligence Implications
While Cry0 has not yet demonstrated active victim compromises, security teams should consider several implications for their ransomware threat intelligence programs:
Affiliate Competition: The 90/10 affiliate split may attract experienced ransomware operators from other groups looking for better compensation, potentially accelerating the operation’s development and increasing attack volume once they become operational.
Infrastructure Evolution: The blockchain-based extortion infrastructure, if implemented as described, could represent a significant evolution in ransomware operations that makes takedown efforts substantially more challenging for law enforcement.
Ecosystem Trends: The use of decentralized storage for extortion sites could become a trend across the ransomware ecosystem if Cry0 demonstrates it is effective at increasing payment rates.
Rust Adoption: More ransomware groups are adopting Rust for payload development due to its performance characteristics and the challenges it poses for reverse engineering. Cry0 continues this trend.
Indicators of Compromise (IOCs)
Organizations should monitor for the following indicators associated with Cry0:
Data Leak Site: cryoblogedawivdcknyd4jsjxkrx3xrqqltxla6wwjjnzm3f3jaxjzqd.onion
Historical IP: 45.227.253.59:3111 (no longer active)
TOX ID: 54E9450799AFBBA90992E3C40F552C8C05D5765144396C6A1A622FD9DABD01101F9DC0CF90F4
What Security Teams Can Keep in Mind About Cry0
Cry0 represents the latest addition to an already crowded ransomware-as-a-service market. While their technical claims around encryption speed and blockchain-based decentralized infrastructure are notable, the fabricated transaction evidence suggests their current capabilities may not match their marketing. The group appears to be in early development stages, with no confirmed victims and infrastructure that has already undergone changes.
Security teams should add Cry0 to their ransomware threat intelligence watchlists while maintaining focus on established ransomware groups with proven track records. The blockchain infrastructure claims, if eventually implemented, could set a concerning precedent for the broader ransomware ecosystem.
As always, the best defense against ransomware remains a combination of robust backup strategies, network segmentation, endpoint detection and response capabilities, and ongoing security awareness training for employees.
Monitor for External Threats with Flare
The Flare Threat Exposure Management solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors. Our platform automatically scans the clear & dark web and prominent threat actor communities 24/7 to discover unknown events, prioritize risks, and deliver actionable intelligence you can use instantly to improve security.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. See what external threats are exposed for your organization by signing up for our free trial.