By Tammy Harper, Senior Threat Intelligence Researcher
The name itself is a signal. Handala refers to the Palestinian cartoon figure drawn with his back turned, a long-standing symbol of resistance and displacement. It is instantly recognizable, and its use here is intentional. Before anything technical happens, the identity is already doing part of the work.
Handala, Palestinian cartoon symbol
The persona appeared in late 2023, right after the October 7 attacks and the escalation that followed. Like a number of hacktivist-branded groups that showed up around the same time, it positioned itself as part of the conflict. At the same time, the activity didn’t really look like typical grassroots hacktivism.
The group’s attack pattern consistently attacked targets closely seen in Iranian state-aligned operations. A lot of the behavior overlaps with clusters tracked as Void Manticore, and in some areas with activity Microsoft attributes to Red Sandstorm. The hacktivist framing helps with visibility, but it also creates some distance from direct attribution.
Early Targeting and Victimology (2024)
Most of the early activity in 2024 focused on Israeli organizations tied to infrastructure and logistics. That includes Ashdod Port and the HADAROM Container Terminal, both of which are central to maritime operations. Those are high-impact targets, but they’re also easy to frame publicly. Disrupting or exposing them carries both operational consequences and narrative value.
Other victims follow a similar pattern. Home Medics and Elitech, along with other healthcare and service-related entities, show up in their posts. On their own, these aren’t especially strategic targets, but they’re close enough to critical systems that they can be presented as part of something larger. Across different campaigns, Handala consistently ties its victims back to state infrastructure, even when that connection is indirect.
Exploitation and Disruption Techniques
There’s no strong indication of advanced exploitation. Most of it looks like exposed services, weak credential hygiene, and environments that were easier to get into than they should have been. Once inside, the activity becomes more controlled. They use legitimate administrative access, move carefully, and focus on collecting data early. Internal documents, communications, anything that can be used later.
In some cases, they go further and wipe systems. Not encrypt, not hold access, just delete everything. There’s no follow-up for payment, no attempt to negotiate. It lines up more with disruption than anything financially motivated.
The material they take is released in a way that already frames the story. Posts usually include selected screenshots, excerpts, and commentary that guide how the breach is interpreted. By the time a victim is responding externally, the narrative has already been set.
That’s consistent across their activity, and it’s probably the most deliberate part of what they do.
Shift in Scope and Targeting
This model held through most of 2024 and into 2025, before starting to shift in 2026. The clearest example is the claimed attack against Stryker, a U.S.-based medical technology company. In that case, the group reportedly used access to Microsoft Intune to wipe devices across the environment at scale. That’s a different level of impact, and it moves the targeting outside of a purely regional focus.
It also lines up more closely with broader state-aligned activity as the Iranian War lingers.
Analysis of Domain Seizure
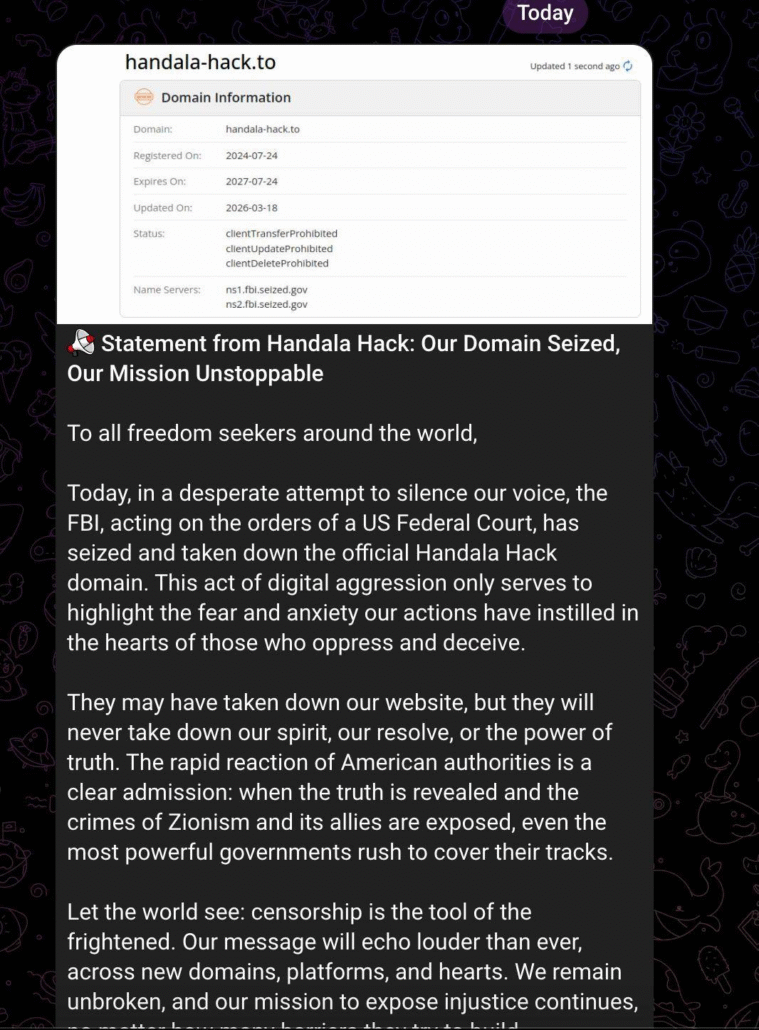
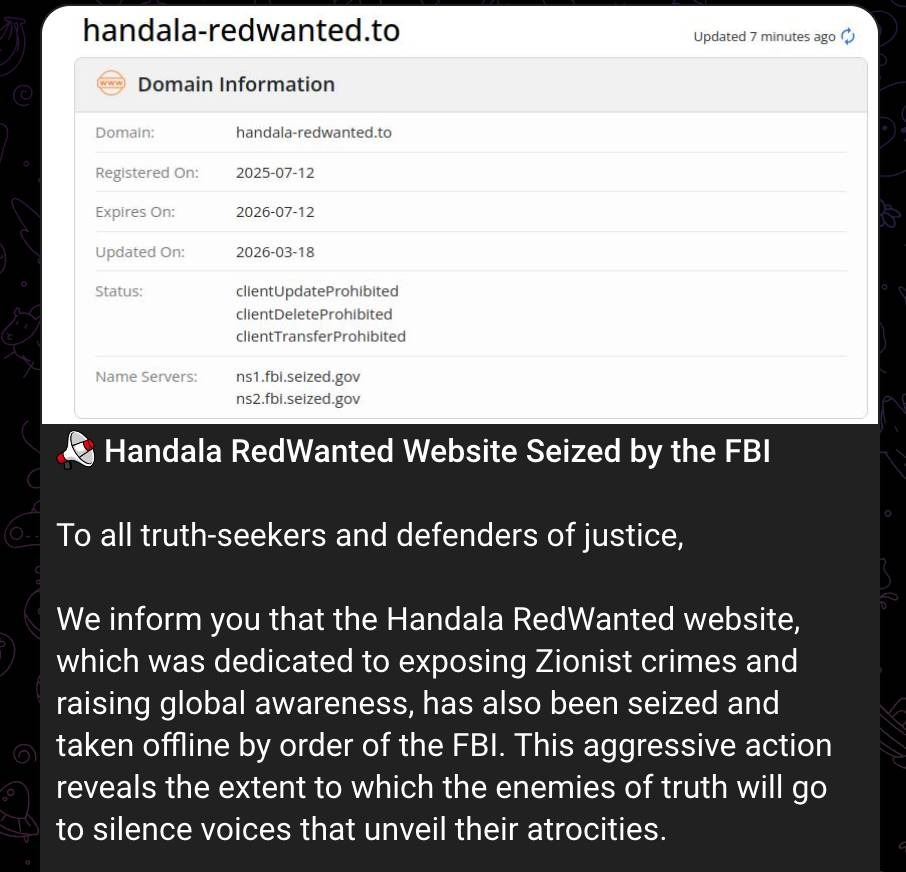
The seizure of handala-hack.to and handala-redwanted.to sits on top of all of this.
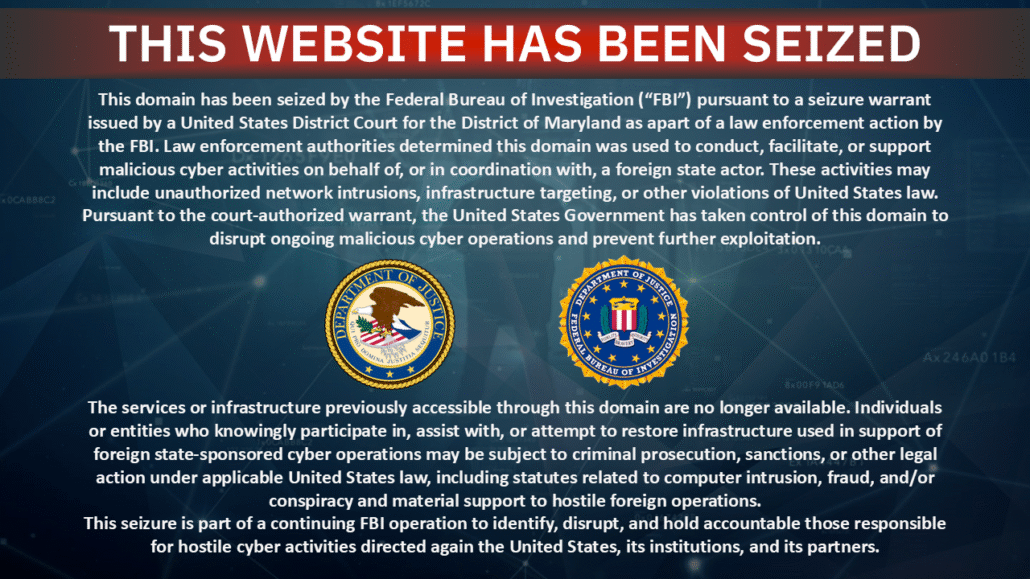
Seizure notice from the FBI
These domains were where everything came together. Claims, leaks, messaging, all of it flowed through them. Taking control of those domains removes their ability to publish in the same way, at least temporarily.
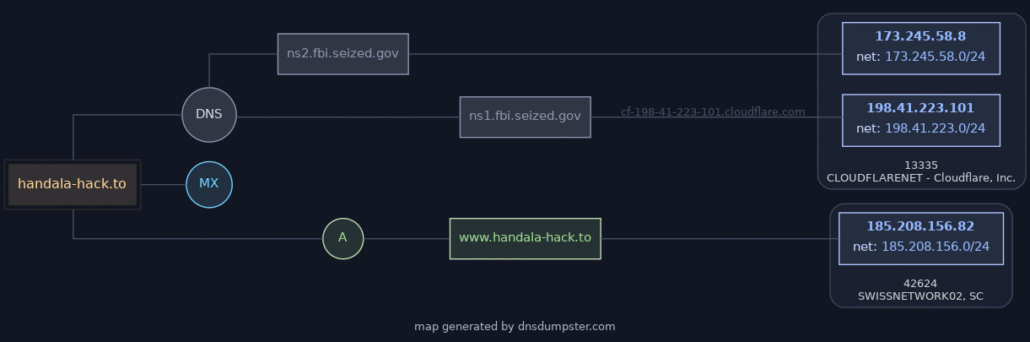
Map of domains seized
That matters, but only to a point.
There’s no indication that access has been removed or that previously collected data is gone. Replacing domains is relatively easy, and the group’s activity doesn’t depend on any single piece of infrastructure.
Their response reflects that. The messaging hasn’t changed. The seizure is framed as validation, not disruption, and there’s an expectation that they’ll continue elsewhere.
That’s probably accurate.
For this kind of actor, infrastructure is replaceable. The persona is what holds it together. As long as they can keep accessing targets and putting material out somewhere, the model still works.
Handala’s Response
Handala’s statements on their Telegram channel
In a statement issued on their Telegram channel, Handala asserted that the domain seizure would not stop their mission. The group framed the takedown as validation, not disruption, and communicated the expectation that they would continue operating elsewhere. This response is considered accurate because Handala’s operational model relies on its established persona, and its infrastructure is easily replaceable. Consequently, the seizure is viewed as a disruption of their distribution layer rather than a lasting impediment to their operations.
Outlook
So while the domains are down for now, this looks more like a disruption of their distribution layer than anything else.
And based on how they’ve operated so far, it’s unlikely to slow them down for long.
Monitor State-Aligned Threat Actors as They Shift Infrastructure
Domain seizures disrupt distribution, not operations. Flare continuously tracks threat actor personas like Handala across Telegram channels, leak sites, and replacement infrastructure — so your team maintains visibility even when domains go down and activity migrates.





