By Tammy Harper, Senior Threat Intelligence Researcher
On March 25th, 2026, user Snow from SnowTeam published an advertisement for a new kind of Leak Site concept on the Russian-speaking TierOne forum. The new service is called “Leak Bazaar” and appears to be an evolution in the extortion game.
What stood out to me about Leak Bazaar was not the branding, but instead it seemed to identify a real inefficiency inside the extortion economy and build its entire pitch around solving it. The problem it is trying to solve is straightforward. When an actor steals a large volume of corporate data, and the victim refuses to pay, that data does not always convert neatly into money. Public disclosure can still be useful as a pressure tactic, but a raw dump is often too large, too disorganized, and too uneven in quality to have much value beyond coercion. Anyone who has spent time looking at real exfiltrated datasets knows how much noise they contain. There are system files, duplicate material, outdated records, malformed exports, irrelevant binaries, and large database dumps that may contain valuable information in theory but require work before anyone can actually use them.
Leak Bazaar Hidden Service as of March 25th, 2026
Leak Bazaar is interesting because it starts from that reality rather than pretending all stolen data is immediately useful. The core of the pitch is not really about access or even about leakage. It is about being able to process all of that data. Imagine taking raw corporate data and turning it into something more legible, more selective and precise, and making it marketable for the general population to ingest.
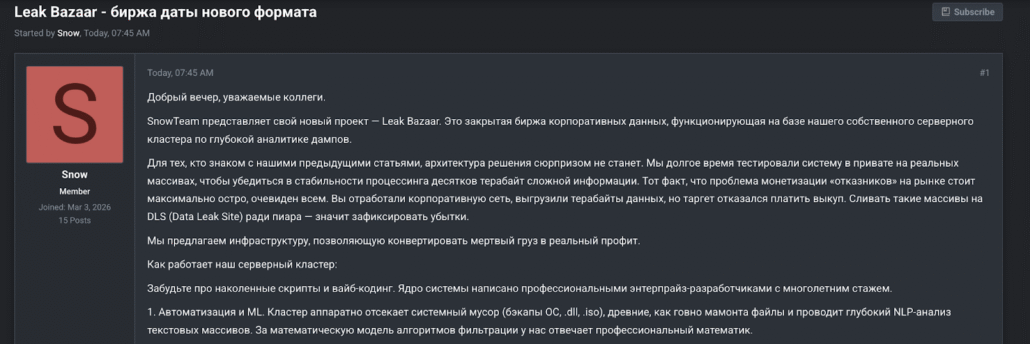
Leak Bazaar Advertisement on Tierone (T1) by Snow aka SnowTeam
A Processing Layer, Not a Leak Site
Whether every technical claim in Snow’s advertisement is true matters less than what the advertisement reveals about the business model it is trying to construct. What Leak Bazaar is really offering is not a DLS or Data or Dedicated Leak Site in the conventional sense, but a post-exfiltration service layer. The ad is written around the premise that the problem is no longer just access to data, but the inability to turn raw corporate theft into structured, repeatable revenue.
That is why the infrastructure section is so important. Snow does not describe the platform as a place to simply host stolen archives. He describes a server cluster built for “deep analytics” of large corporate dumps, with an emphasis on filtering, parsing, and extraction. The language around automated removal of system debris, ML-assisted text analysis, database reverse engineering, ERP parsing, and analyst validation is doing more than advertising technical sophistication. It is trying to reassure both suppliers and buyers that the platform can solve the most frustrating part of data theft, which is that a large percentage of exfiltrated material is too noisy, too unstructured, or too cumbersome to use without additional labor.
That part of the pitch deserves attention because it suggests Snow understands that the real bottleneck is often not collection, but refinement. Many actors can steal hundreds of gigabytes or several terabytes from a target. Fewer can turn that material into something a buyer actually wants. Groups like Anubis, for example, write extensive “investigative journalistic pieces” on their victims after sorting through the datasets.
Anubis Data Leak Site

Anubis Victim Investigative Data Breakdown
Anubis Victim Investigative Data Breakdown 2
A typical database dump may contain highly sensitive financial records, but if it sits in SQL, SAP, or Oracle exports without an environment to restore and interpret it, much of its value remains trapped. Leak Bazaar’s claim is that it can break open that trapped value by converting the hard parts into clean outputs like spreadsheets and structured extracts.
Organizing Stolen Data Around Demand
The categorization model in the ad reinforces that. Snow claims Leak Bazaar will divide the processed material into high-margin buckets such as quarterly financial reporting, M&A, R&D, and personal data. These are not arbitrary file groupings. They are buyer-oriented categories. Each one maps onto a different use case and a different imagined customer. Quarterly financial reporting is framed as useful for traders. R&D material is framed as useful for competitors or technically motivated buyers. Personal data remains the familiar downstream commodity of cybercrime markets. What Snow is really doing here is describing market segmentation. He is saying that stolen corporate data becomes more valuable once it is reorganized around demand rather than around the way it originally existed inside the victim environment.
That is also why the human analyst layer matters so much in the advertisement. Snow is careful not to present the system as fully automated. He explicitly says that algorithms and ML are not enough, and that staff analysts perform the final validation before material is placed on the “showcase.” That detail makes the pitch more credible because it acknowledges the obvious limit of automation in this context. At the same time, it reveals something important about how the platform wants to position itself. Leak Bazaar is not trying to look like a crude warehouse for stolen files. It is trying to look like a managed service, one in which machine processing reduces labor and human review restores trust in the final product. That combination is central to the whole pitch. Without it, the platform would still be selling raw archives. With it, Snow can claim he is selling curated intelligence extracted from those archives.
Turning Failed Ransoms Into Recurring Revenue
Leak Bazaar offers a baseline split of 70 percent to the data supplier and 30 percent to the platform. That is a meaningful signal about where it believes value sits. The supplier still controls the scarce asset, which is access to unpublished corporate data, but the platform is claiming that its processing, packaging, and marketplace functions justify a substantial intermediary cut. In legitimate markets, this would be described as a platform taking margin for aggregation, transformation, and distribution. That is effectively what Snow is trying to normalize here. He wants suppliers to see Leak Bazaar not as a passive middleman, but as the mechanism that unlocks the full monetization potential of otherwise dead data.
The two sales formats in the ad push that logic even further. The exclusive option offers a one-time sale in which the buyer pays full price, and the data is removed from the market permanently. The multi-buyer option halves the price for each buyer, keeps the material listed, and allows the supplier to continue receiving revenue from repeated sales. That is one of the most important parts of the entire advertisement because it shows that Leak Bazaar is not thinking only in terms of extortion. It is thinking in terms of yield. The model treats stolen data less like a weapon that is used once and more like an asset that can generate recurring returns over time. In effect, Snow is trying to turn a failed ransom event into something closer to a revenue-producing catalog.
That changes the economics in a way that is worth taking seriously. A conventional leak site often works as a blunt escalation mechanism. Leak Bazaar is trying to construct an aftermarket. If the victim refuses to pay, the value of the archive does not disappear. Instead, the archive is disassembled, priced by segment, and sold according to buyer appetite. That is a more durable model than simple public dumping because it preserves scarcity where possible, allows repeat monetization, and creates incentives for both suppliers and buyers to use the platform in a more targeted way.
More than a Storefront
The ad also tries to solve a trust problem. It says that all transactions are conducted through the Exploit guarantor, which is meant to reassure participants that the marketplace has some transactional discipline. It promises qualified support for deals and even offers consultation in negotiations with victims, framing the processed data as leverage that can materially change the tone of ransom discussions. That is revealing because it shows Leak Bazaar trying to embed itself not only in resale, but in the negotiation process itself. It wants to be useful before sale, during sale, and after sale. In other words, it is not just building a storefront. It is trying to become part of the extortion workflow.
Even the intake requirements reveal a lot about how Snow imagines the market. The ad asks for unpublished data, predominantly English-language content, target revenue above $10 million, and volumes starting at 100 GB, ideally one terabyte or more. That is a clear quality filter. Leak Bazaar is signaling that it is not interested in every possible dump. It wants corporate material that is large enough, commercially relevant enough, and linguistically accessible enough to justify heavy processing and targeted resale. That makes the project look less like a public bazaar in the literal sense and more like a curated pipeline for specific classes of corporate theft.
Taken together, the advertisement describes a business that sits between several criminal constituencies at once. Suppliers need a way to salvage value from failed negotiations. Buyers do not want five terabytes of noise when they only care about source code, financials, or personal data. Negotiators benefit from having a cleaner, more persuasive articulation of what was actually stolen. Leak Bazaar is trying to place itself at the center of all three relationships. That is why it feels more significant than a simple leak site launch. The pitch is not just “we have data.” The pitch is “we know how to process stolen data into something more useful than the raw archive ever was.”
That is ultimately what makes the advertisement worth studying. It reveals a view of extortion in which the breach itself is only the beginning of the value chain. Theft creates the raw input, but the real monetization happens afterward through filtering, extraction, segmentation, and repeated sale. Snow may be overselling his infrastructure, and some of the platform’s claims may not survive contact with reality, but the advertisement still matters because it shows how at least one actor is trying to professionalize the space between exfiltration and monetization. Leak Bazaar is not interesting because it promises another place to dump stolen files. It is interesting because it tries to build the processing layer that turns those files into a market.
Know When Your Data Enters the Aftermarket
Platforms like Leak Bazaar are turning failed ransoms into structured revenue streams — parsing, categorizing, and reselling your data long after the breach. Flare monitors 1000+ dark web sources so your team gets alerted the moment your organization’s data surfaces, before it’s packaged and sold.