By Assaf Morag, Cybersecurity Researcher
While hundreds of millions of soccer fans worldwide eagerly await the kickoff of the 2026 FIFA World Cup, threat actors are preparing just as intensely to deploy nefarious fraud schemes against unsuspecting supporters.
We have uncovered a large-scale phishing and consumer fraud infrastructure designed to exploit this global excitement. The operation is already in place, leveraging 75+ lookalike domains to sell fake tickets and merchandise that will never reach their buyers.
About this World Cup Series
As of early April, the lineup of all 48 teams set to compete in the games hosted in the US, Canada, and Mexico are complete. Threat actors have also prepared phishing infrastructure to ensnare unsuspecting fans.
We expose the infrastructure behind the campaign, including its scope, domains, and associated IPs to raise awareness, protect fans, and support FIFA’s efforts to combat World Cup–related cybercrime.
This blog is part of our World Cup 2026 Cybercrime Series: a collection of focused research pieces examining the evolving threat landscape surrounding the tournament. The series explores key areas including phishing infrastructure, fraud and scams, illegal streaming services, illicit betting platforms, insider threats, and other cybercriminal activities targeting the 2026 World Cup.
Key Findings About World Cup Phishing Infrastructure
- There’s a coordinated phishing infrastructure of 14 IP addresses hosting 79 typosquatting and lookalike domains impersonating the official FIFA website: The sites replicated legitimate FIFA URL path structures to create a highly convincing phishing experience.
- All sites are built based on the same templates and show high automation as over half the domains were registered through a single registrar, suggesting a scalable campaign designed to expand as tournament demand intensifies: 45 out of 79 domains were registered to GNAME.COM PTE. LTD., which points to a centrally managed operation rather than independent actors.
The fraudulent sites function as full-ecosystem replicas, not simple phishing pages: HTML and structural elements are copied from the malicious infrastructure, while images and icons are pulled directly from the real FIFA website, blending legitimate and fraudulent content to deceive even attentive users.
Detect Lookalike Domains Before They Reach Your Customers
Flare continuously monitors newly registered domains, typosquatting patterns, and underground activity to detect phishing infrastructure impersonating your brand, enabling early disruption before campaigns scale.
The Phishing Infrastructure Impersonating the FIFA Website
We identified an infrastructure comprising 14 distinct IP addresses hosting 79 typosquatting and lookalike domains impersonating the official FIFA website.
Typosquatting domains are crafted to closely resemble legitimate domains by introducing subtle modifications (such as character substitutions, omissions, or additions or using numbers instead of letter) that can easily deceive users. The official FIFA domain is https://fifa.com (with https://www.fifa.com redirecting to it).
Threat actors have registered domains such as vww-fifa[.]com, which combines character substitution (“www” → “vww”) and structural variation (“fifa.com” → “fifa-com”) to mislead even experienced users.
Lookalike domains, by contrast, do not rely on direct string similarity but instead exploit brand association and user expectations. Domains such as fifa[.]sale can convincingly impersonate official services – such as ticketing or merchandise platforms—despite not matching the original domain structure.
Coordinated Phishing Infrastructure Deployment Using FIFA Lookalike Domains
Below you can observe the registrar used:
| Registrar | Count |
|---|---|
| GNAME.COM PTE. LTD. | 45 |
| GoDaddy.com, LLC | 14 |
| Metaregistrar BV | 10 |
| Alibaba Cloud Computing Ltd (HiChina) | 6 |
| PT Jagoan Hosting Indonesia | 2 |
| GMO Internet Group, Inc. d/b/a Onamae.com | 1 |
| Web Commerce Communications Limited | 1 |
A significant portion of the domains were registered through GNAME.COM PTE. LTD., a registrar known for supporting a wide range of payment methods (including cryptocurrency) which may make it attractive to threat actors seeking flexibility and reduced traceability.
When accessing these domains via a browser, users are redirected to paths such as /en/tournaments/mens/worldcup/candamexicousa2026. While not an exact match, this structure closely mimics the legitimate FIFA website, reinforcing the illusion of authenticity.
As shown in the screenshot below, the combination of domain typosquatting and realistic URL paths creates a highly convincing phishing experience that can mislead even attentive users into believing they are interacting with the official site.
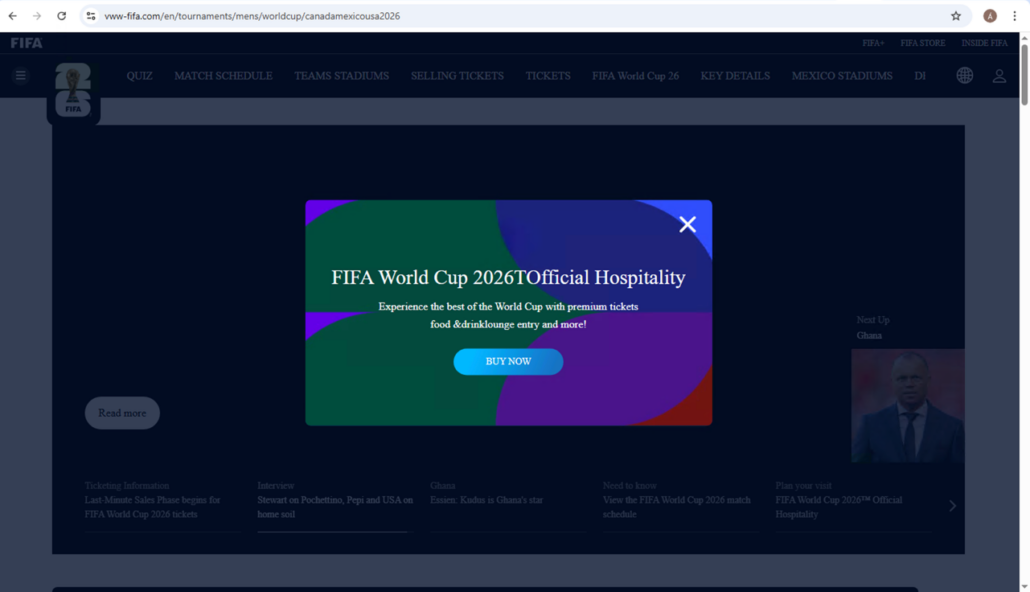
Fraudulent World Cup website
Below you can see an option of “Match Schedule.” The HTML and most of the elements are taken from the malicious website, but some (like pictures, icons etc.) are taken from the official FIFA website.
The “Match Schedule” page of the fraudulent website
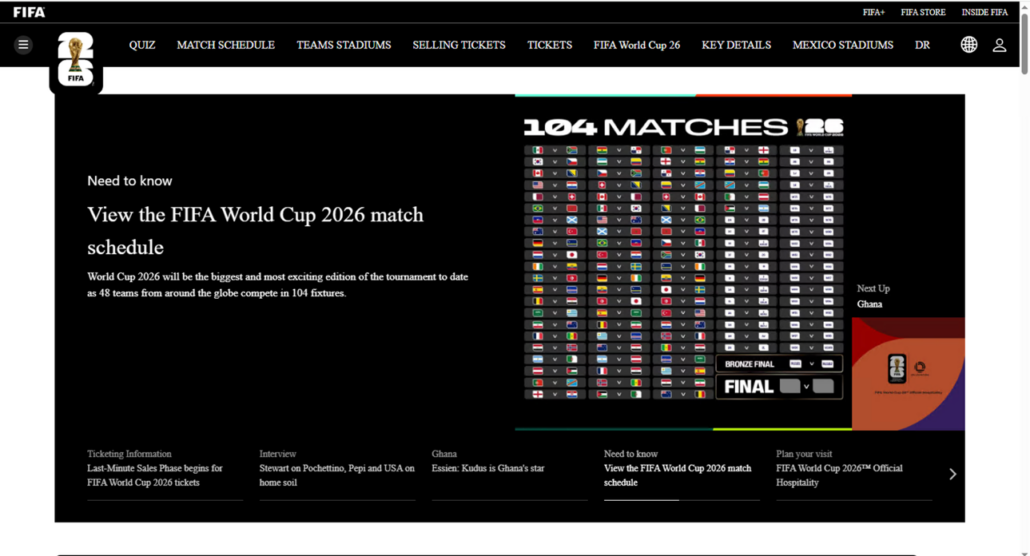
The FIFA store itself looks exactly like the original one.
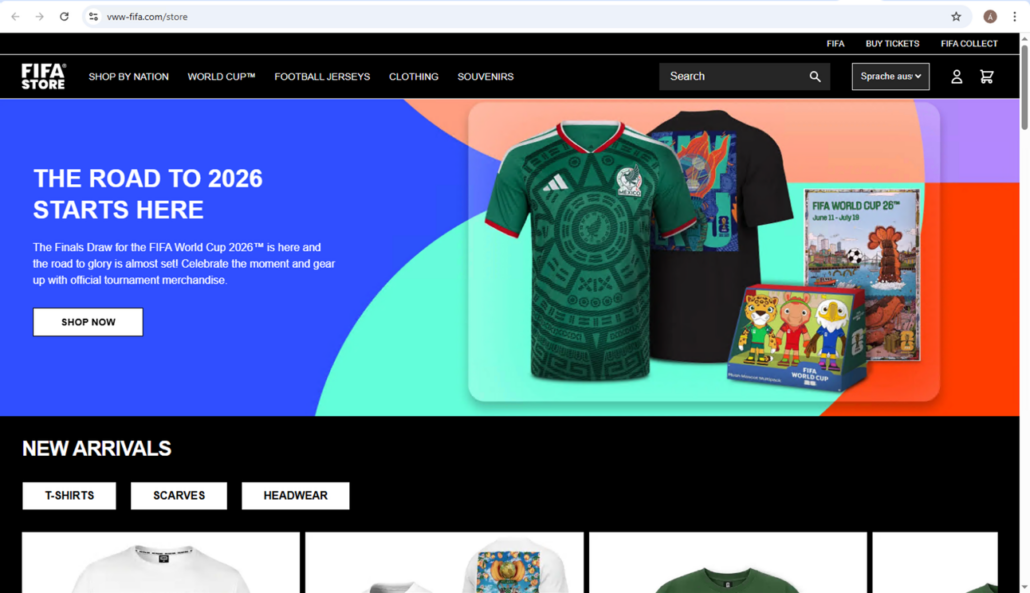
Fraudulent FIFA Store page
When clicking on the “FIFA Collect” page, the new tab opens to the real FIFA website.
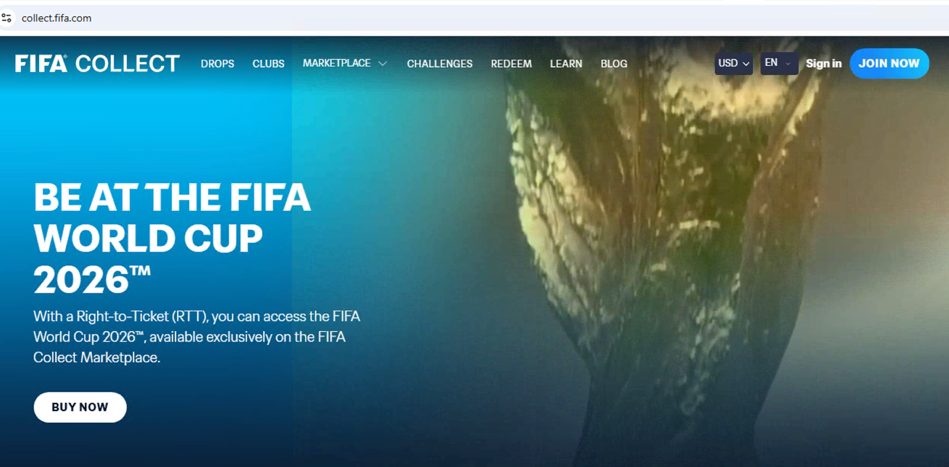
Fraudulent FIFA Collect page
To further look into the fraudulent FIFA Store, we tried to buy the official original game jersey of the next 2026 World Cup winner.
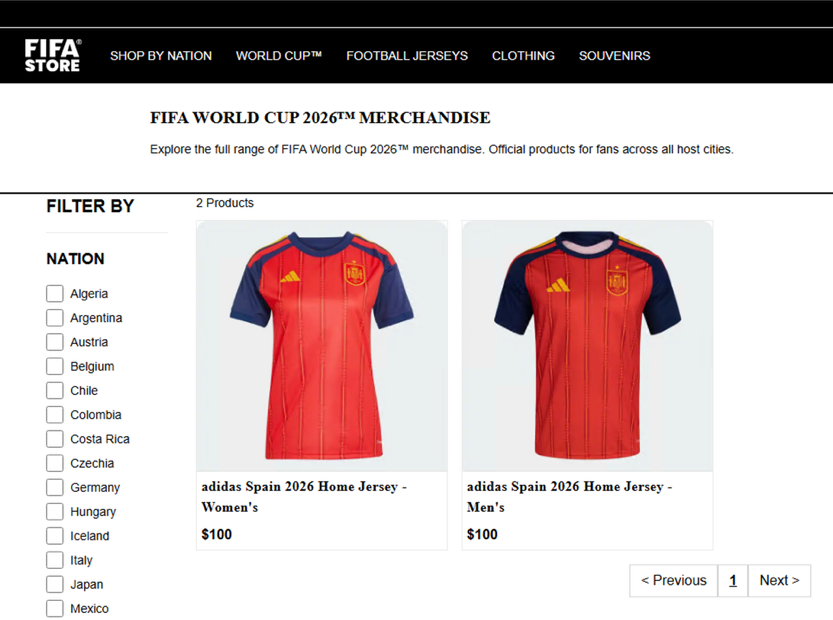
Screenshot of shirts sold on the fraudulent FIFA Store
After we chose a jersey, we were redirected to a fake FIFA ID login page, which resembles the legitimate FIFA ID login page.
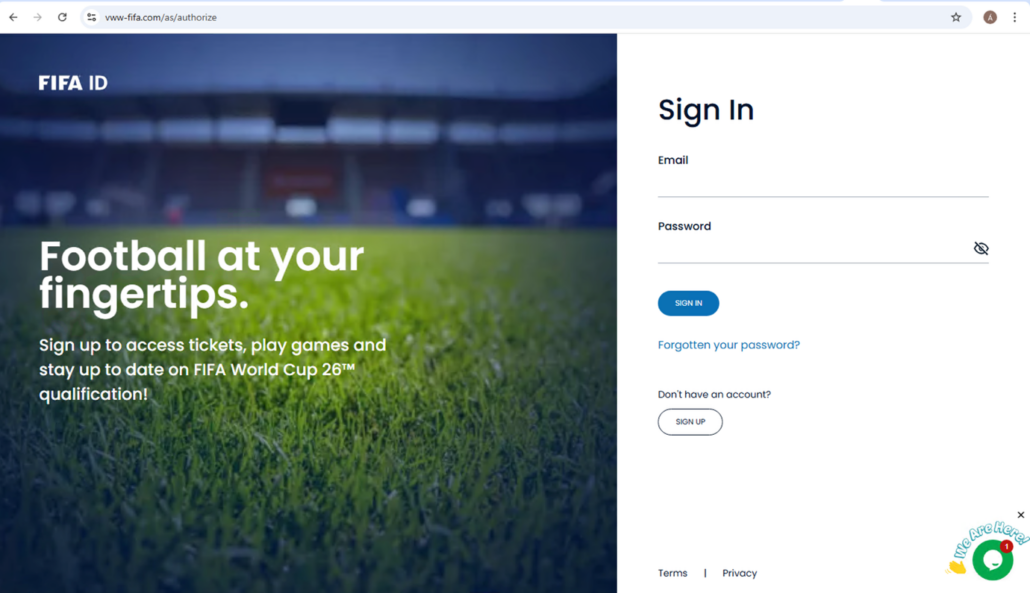
Fake FIFA ID page looks similar to the real version
We were asked to sign in to our FIFA account. So, we entered a fake login, which surprisingly (or not) was immediately accepted.
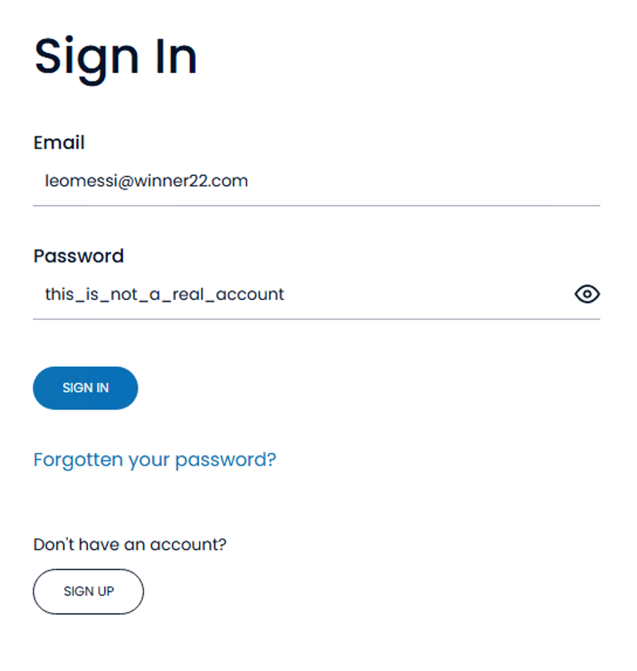
Fake login entered into the FIFA ID page
This provides additional insight into the nature of the site. While it may function as a phishing portal targeting FIFA accounts for potential account takeover, it does not appear to proxy or relay live data from the legitimate platform, unlike more advanced, real-time phishing kits. Instead, the evidence suggests it primarily operates as a standalone financial fraud site, designed to directly collect payments from victims.
That said, harvesting user credentials remains a valuable secondary objective. Compromised FIFA accounts could be monetized by reselling legitimate match tickets, which often range from several hundred to several thousand dollars.
Following the fake login process, selecting merchandise options (such as shirt size), and completing the purchase flow, we proceeded to add a match ticket (for example, Spain vs. Uruguay) to further analyze the transaction behavior.
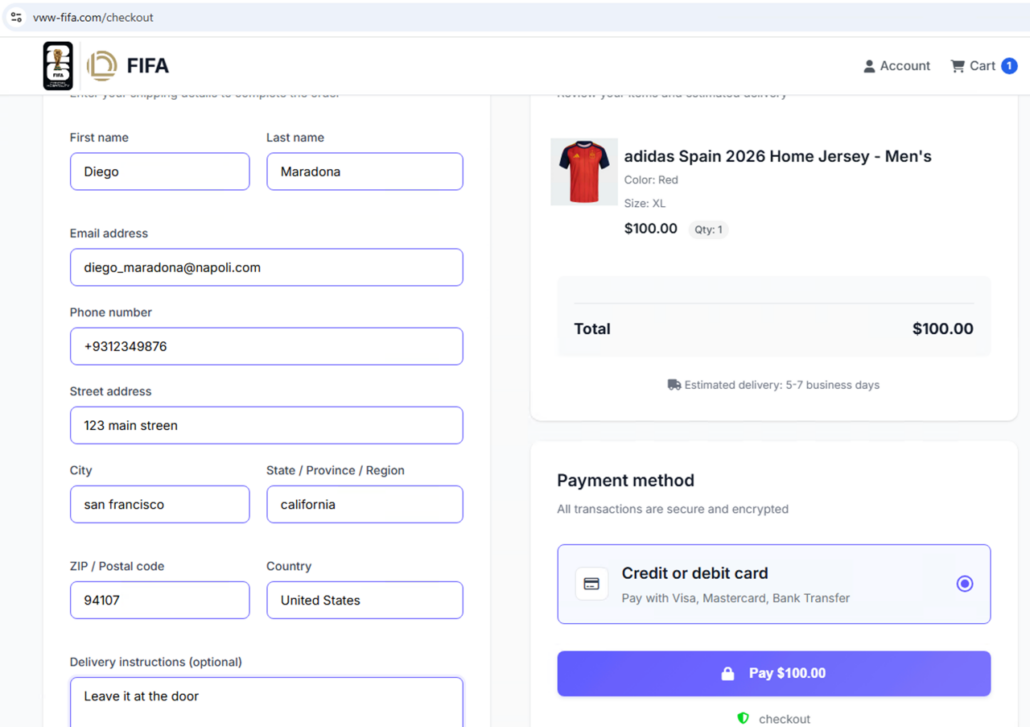
Entering in false information for checking out from the fake FIFA Store
As expected, the ticketing page also resembles the real FIFA website.

False FIFA ticketing page
We selected a ticket for a game and clicked to check out.
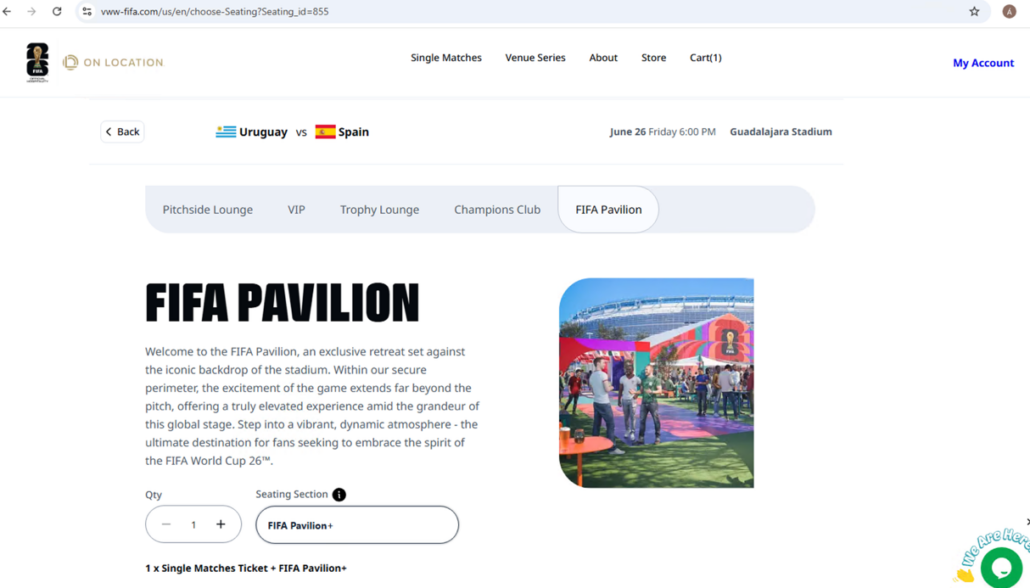
Selecting a ticket
Below you can see our shopping cart.
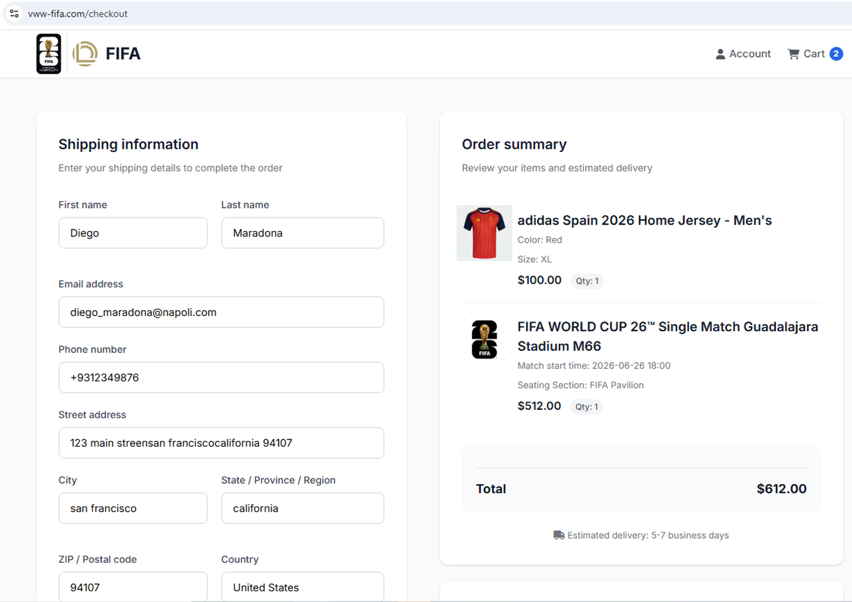
Shopping cart includes a jersey and a game ticket
Before being directed to the actual payment methods, the website offers the option to pay with a credit card.
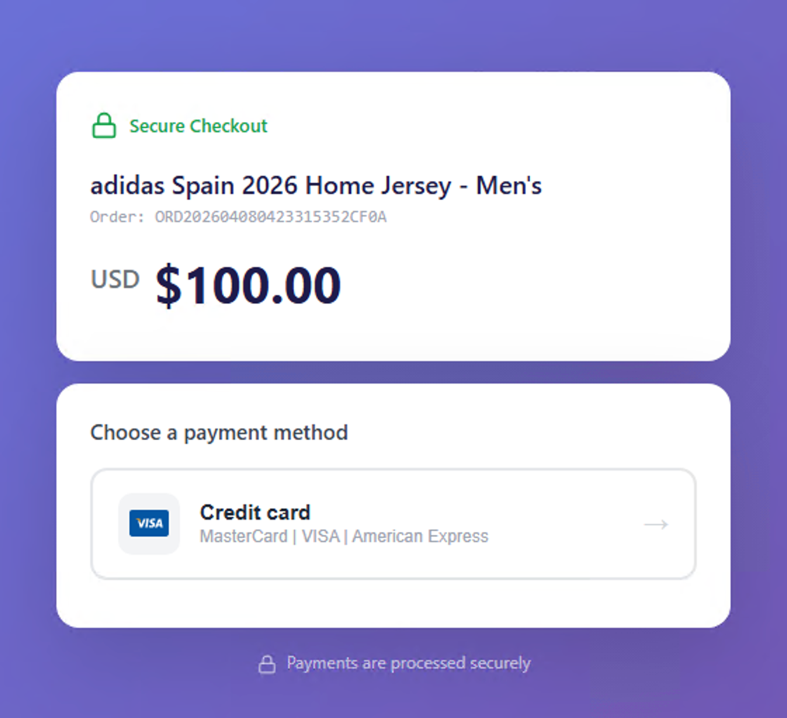
Payment method available includes credit card
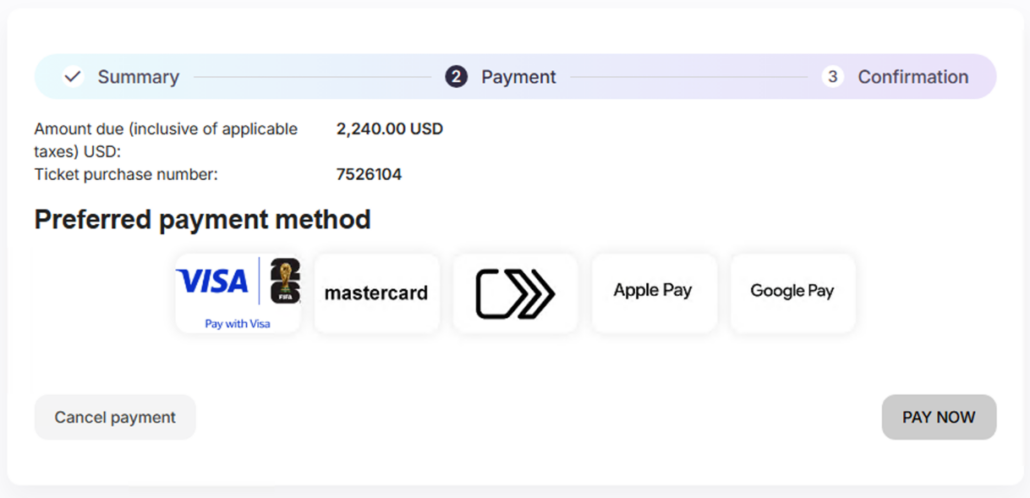
However, the next page shows that the actual payment methods available are only through various payment apps and crypto.
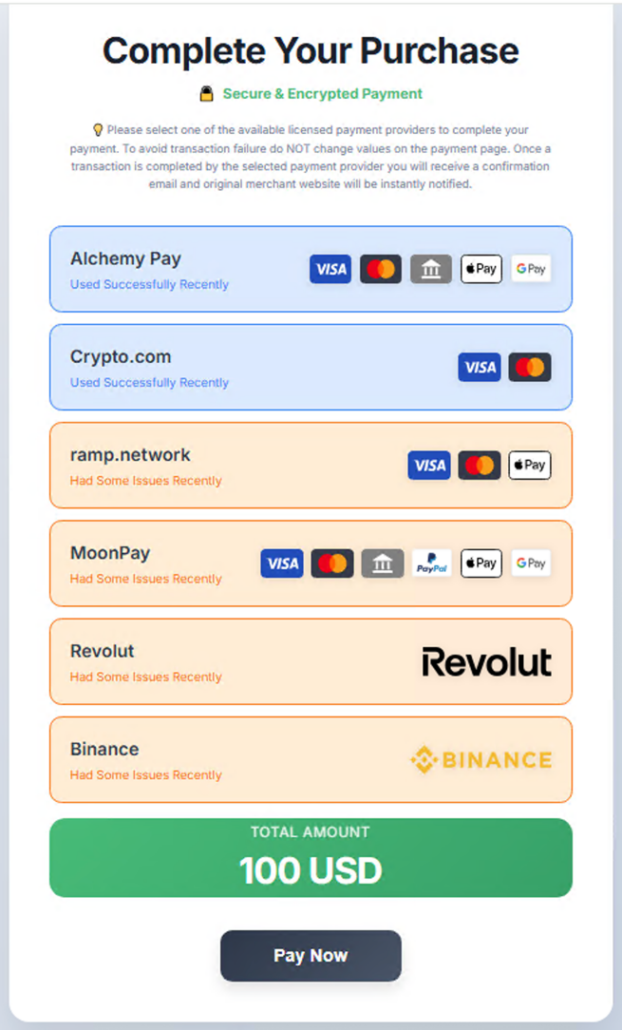
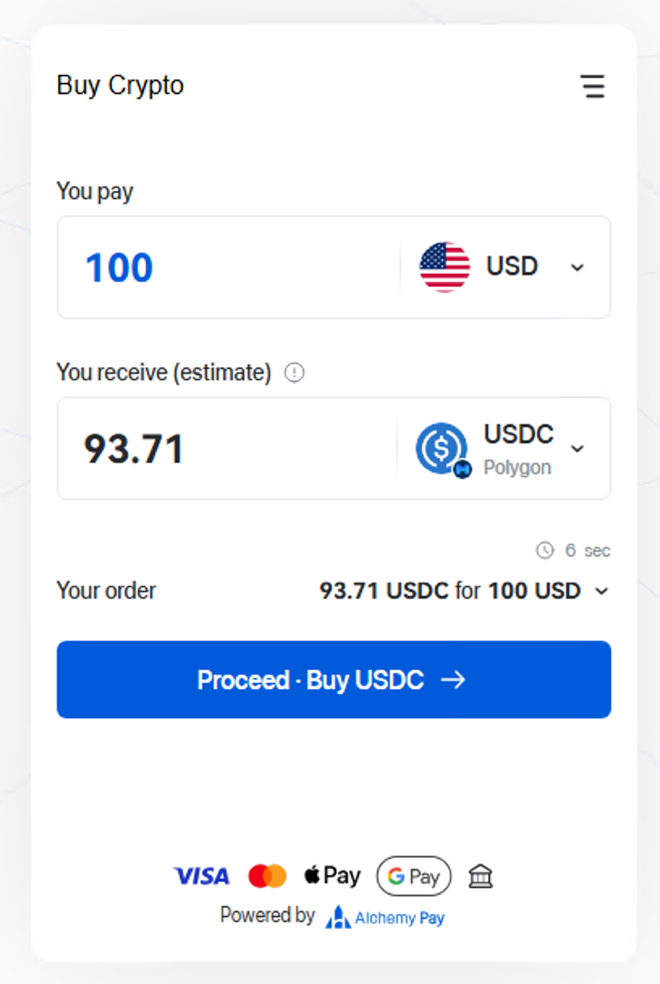
The only payment methods available are payment apps and crypto
We wanted to inquire more about that and tried using the chat option, but it was not functional.
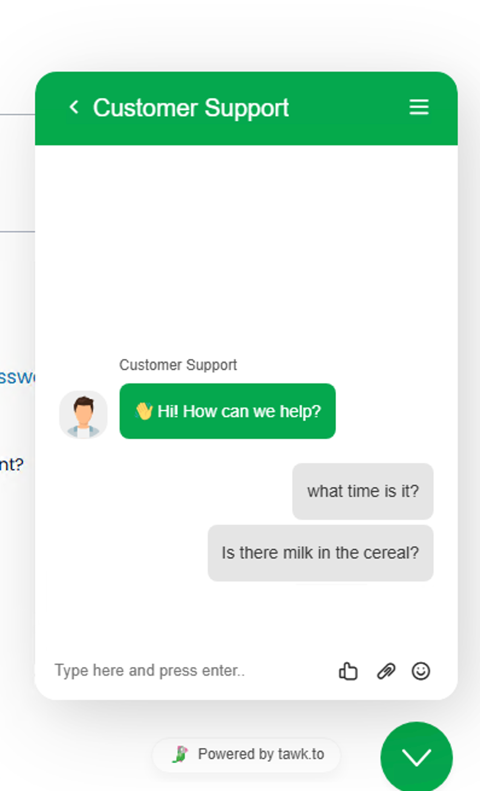
Customer support chat did not actually work
As a comparison, we registered an account with the real FIFA website. The threat actors’ fake websites are pretty similar to the real version.
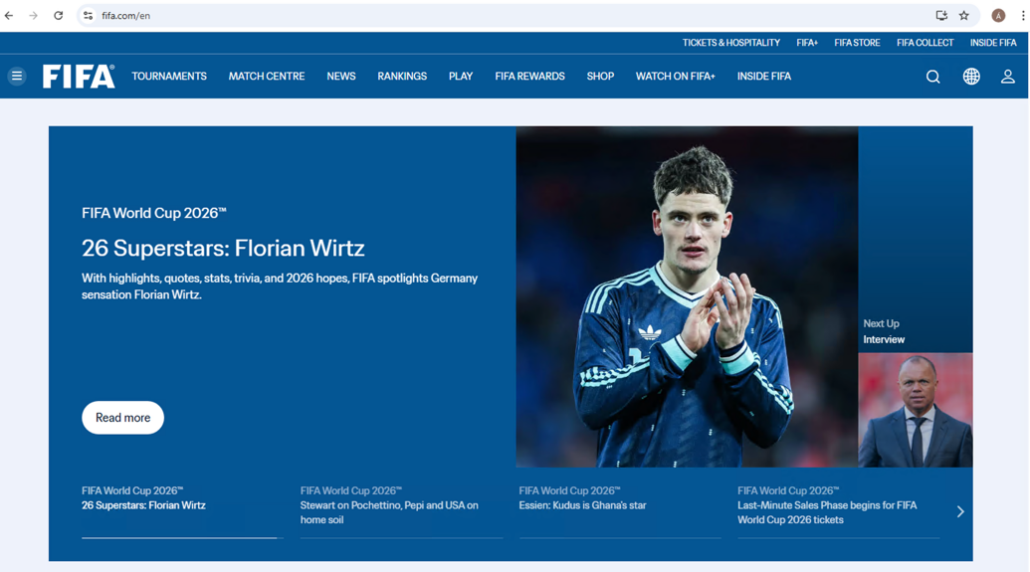
Real FIFA website
The FIFA ID login page was copied pretty closely by threat actors for their fake version.
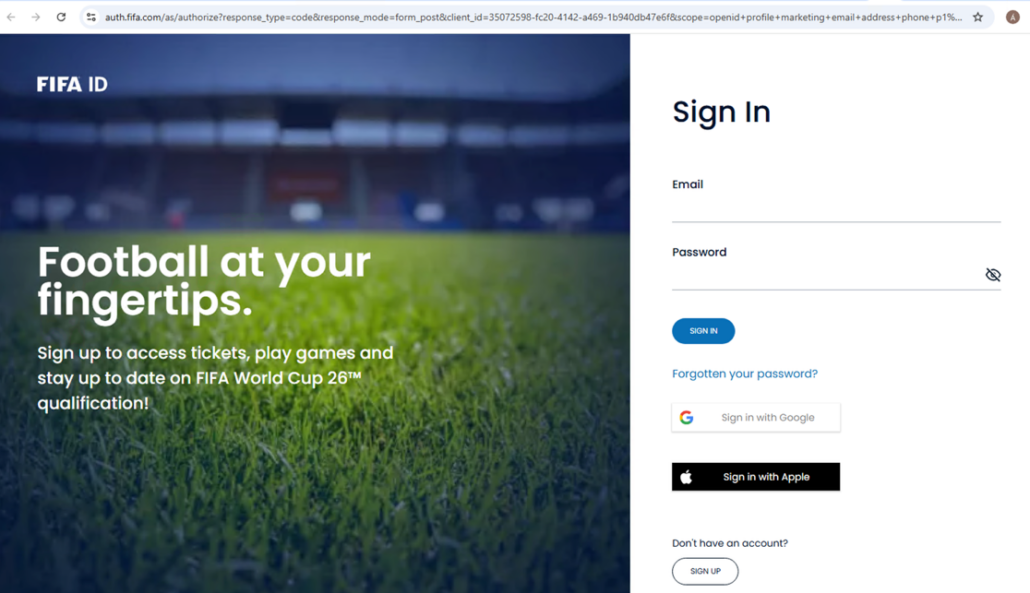
FIFA ID login page
However, here is where the similarities end. The ticket purchasing process is completely different.
The page prompted choosing a specific stand, sector, block and seat, rather than selecting a ticket for a game (which is what the fake website allowed). The Spain vs. Uruguay tickets were sold out, so we selected a ticket for the Canada vs. Bosnia and Herzegovina game.
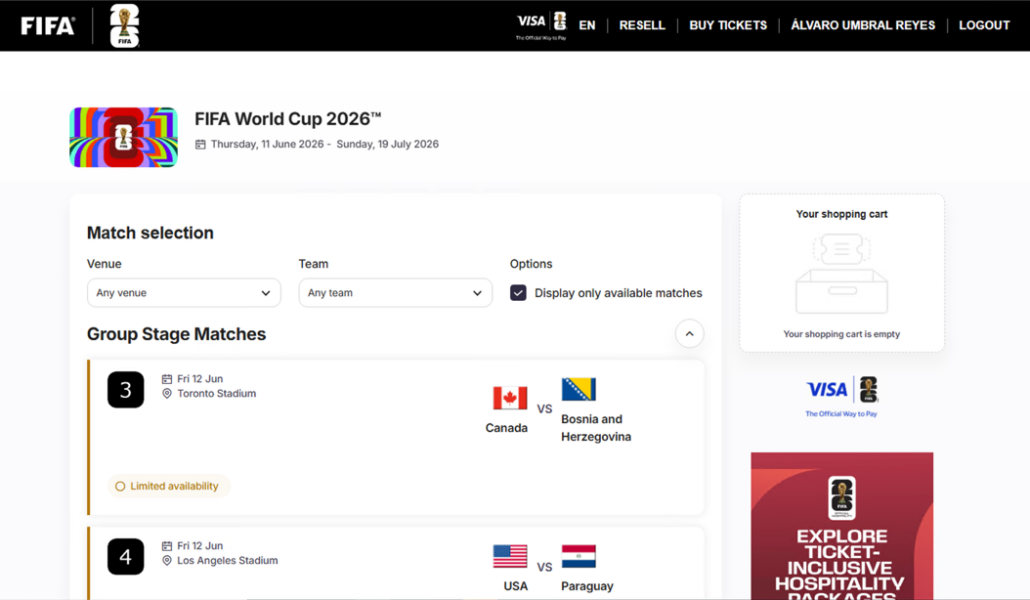
Step to choose a game
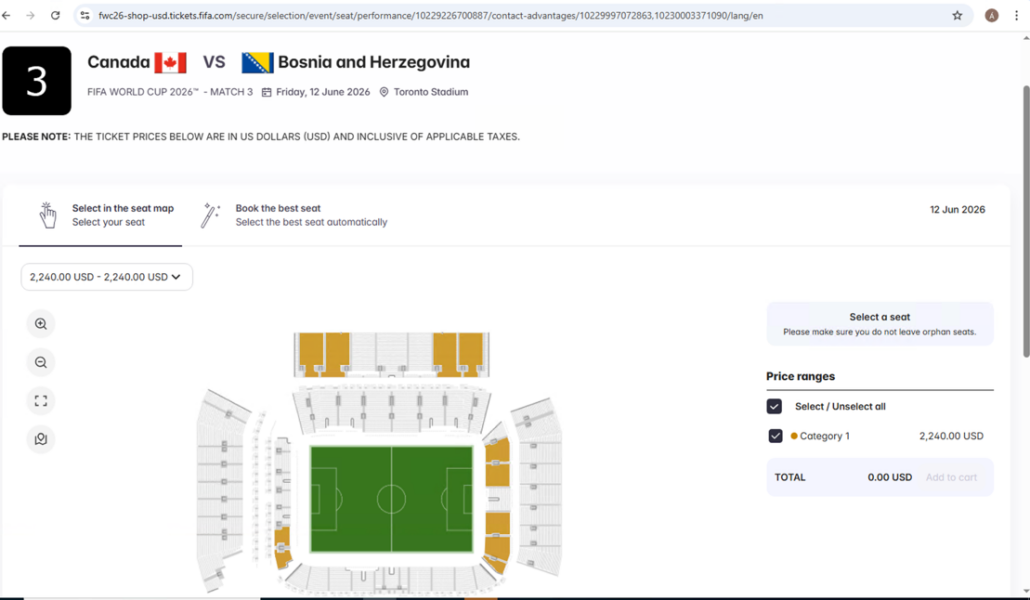
Step to choose a stand
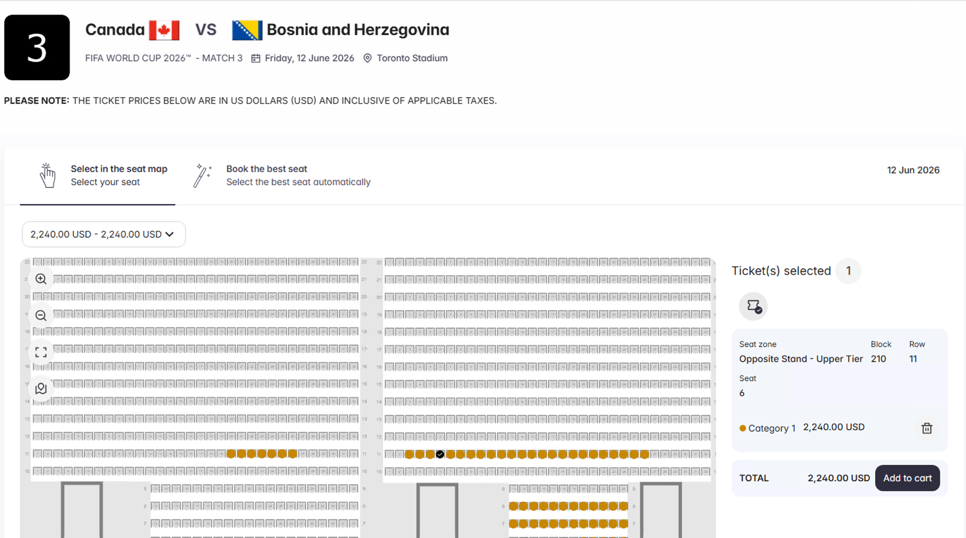
Step to choose a seat
The payment page allows for the option to pay with a credit card, rather than through various applications or crypto.
Payment page
The 2026 World Cup is not just a global sporting event, but it’s also a prime target for cybercriminal operations at scale.
Five Best Practices on How Fans Can Avoid Getting Scammed
Stay safe during the World Cup and similar high-profile events with these key practices:
1. Verify the Domain Carefully
- Only use the official domain: https://fifa.com
- Watch for subtle changes like:
- vww-fifa.com
- fifa-sale.com
- fifa-com.*
- Even small differences can indicate a scam
2. Avoid Clicking on Ads or Social Links
- Fraudulent sites are often promoted via:
- Social media
- Messaging apps
- Sponsored ads
- Always navigate manually to trusted websites
3. Be Suspicious of Payment Methods
- Official platforms use secure, traceable payment methods (e.g., credit cards)
- Red flags include:
- Crypto payments
- Payment apps only
- No refund or buyer protection
4. Validate the Purchase Flow
- Real ticket platforms:
- Require seat selection (section, row, seat)
- Scam sites:
- Offer generic tickets without seat details
- Allow unrealistic availability (e.g., sold-out matches)
5. Never Trust Login Pages Blindly
- If login credentials are accepted instantly (even fake ones) → it’s a scam
- Use password managers, as they won’t autofill on fake domains
Threat Actors Increasingly Build Convincing Fraud Architecture
Attackers no longer rely on simple phishing pages; they build entire ecosystems that mimic legitimate platforms, making detection increasingly difficult for end users.
Awareness, verification, and proactive monitoring are critical for fans, and organizations can proactively detect and disrupt fraud infrastructure to protect end users.
Disrupt Fraud Infrastructure Before It Scales
Flare correlates domains, IPs, registrars, and hosting providers to give your team a campaign-level view of phishing operations, supporting rapid takedowns through actionable intelligence shared with registrars and law enforcement.
Indication of Compromise
| # | Category | Value | Classification |
|---|