North Korean IT workers (NKITW) are infiltrating companies across North America and Western Europe through job applications. Joint research from Flare and IBM X-Force reveals the inner workings of a sprawling operation in which skilled IT professionals use fake identities to land remote jobs, funneling salaries back to the DPRK regime.
This is a close look at the day-to-day operations, internal tools, and organizational structure behind one of the most unusual threats facing organizations today.
Keep reading for the highlights, and check out the full report here.
Equip Security Professionals and HR Teams to Threat-Hunt
As remote work persists and AI makes persona creation easier, organizations need ground-level intelligence to detect and stop this threat.
The Scale of the Problem
Estimates suggest there are between 3,000 and 10,000 North Korean overseas workers across multiple industries, with some reports indicating over 100,000 workers spread across 40 countries. These operations are estimated to generate approximately $500 million annually.
A single DPRK IT worker can individually earn more than $300,000 a year. While some teams of IT workers have been linked to data exfiltration and cryptocurrency theft, the primary motivation is revenue generation. These salaries fund the DPRK regime’s strategic objectives, including weapons programs.
A Structured Operation with Clear Roles
According to Flare Research and IBM X-Force, the NKITW ecosystem operates with a clear, multi-tiered structure:
- Recruiters screen potential IT workers and conduct initial interviews, sometimes recruiting candidates who may not fully understand what they’re signing up for
- Facilitators manage fake identities, apply to jobs (sometimes 120+ per day), and coordinate with western collaborators
- IT workers do the actual technical work using fake personas
- Collaborators/brokers are western individuals who provide their real identities, receive corporate laptops, pass drug tests, and handle paperwork in exchange for a share of the salary
Our research uncovered internal timesheets tracking daily work down to the second, ranking systems for worker productivity, and educational slide decks with tips on landing freelance and full-time jobs.
How NKITW Build Fake Identities
The persona creation process is methodical. Workers use tools like Fake Name Generator to create identities and then build out these identities across LinkedIn, GitHub, Upwork, and other platforms.
For GitHub profiles specifically, the research uncovered searches for topics like “how to create fake commit activity on GitHub” and “how to get fake GitHub badges.” Profiles often contain empty repositories or boilerplate code with generic names, alongside several forked repos to appear more substantial.
AI tools play a significant role. Workers download and edit photos to avoid reverse-image searches, use tools like RoomGPT to create fake background images for video calls, and rely heavily on Google Translate and ChatGPT throughout their daily workflow.
One worker downloaded RoomGPT from GitHub, followed the instructions to run it locally, and then Google searched images of rooms
The Freelance and Full-Time Hustle
NKITWs operate in two modes:
Freelancing: Workers bid on projects across platforms like Upwork, Toptal, Fiverr, and others, across about 80 to 1,000 projects in one month, with only about 10 acceptances. Average payouts range from $200 to $1,000 per job. When workers win a contract they can’t complete, they quietly hire additional help.
Full-time employment: This is more lucrative but requires deeper deception. Western collaborators assist with identity verification, background checks, I-9 paperwork, and receiving corporate hardware. Workers look for remote positions at web agencies, where they can gain access not only to the agency’s internal systems but also to the agency’s clients — multiplying their access to corporate email, Slack, Jira, Shopify, and other platforms.
Google Translate as a Lifeline
One of the most revealing aspects of the research is how central Google Translate is to NKITW operations. Workers use it at nearly every stage: translating job descriptions, crafting applications, interpreting ChatGPT responses, and communicating with collaborators.
Interestingly, a large portion of their translation activity goes from English to Korean. This suggests workers draft messages in English first, then translate back to Korean to validate that the meaning holds. Because Google Translate updates the URL bar with each character typed, browser histories showing long sequences of incremental translation URLs indicate the worker was composing messages directly, a useful forensic indicator.
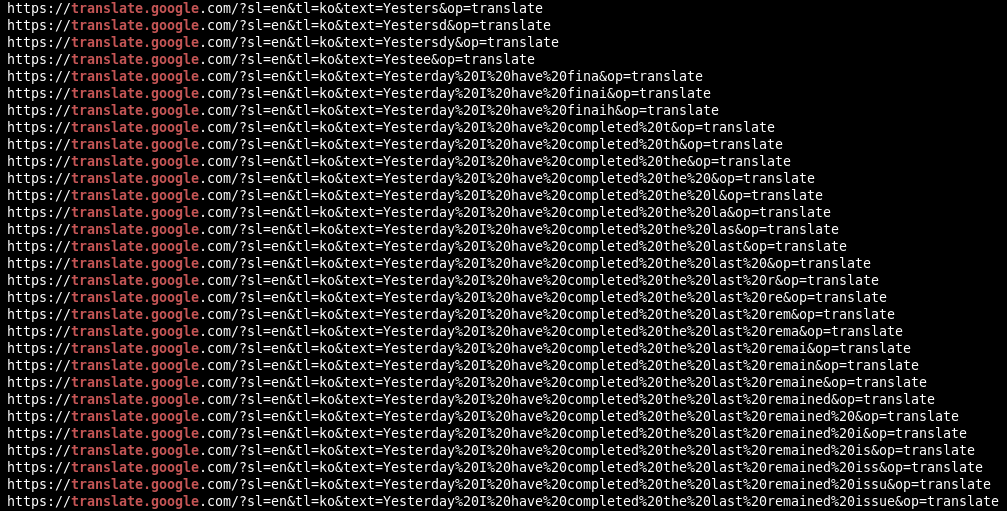
Example of the sequence of URLs visited as a North Korean IT worker types their daily scrum update letter-by-letter into Google Translate in English, and translates to Korean to validate that it makes sense
Internal DPRK Infrastructure
The research uncovered concrete evidence of internal management platforms:
- RB Site (assessed with moderate confidence to be associated with Ryonbong, a sanctioned entity linked to DPRK weapons procurement): a back-office web platform hosted at an internal IP where workers track jobs, manage hardware, and download software updates
- NetKey/OConnect: DPRK-owned VPN and authentication software found installed on worker machines, used to connect to internal North Korean networks
- NetkeyRegister: another internal portal for managing VPN credentials and device registration
These tools, especially in combination, represent strong forensic indicators of NKITW activity.
The Inevitable Termination Cycle
The research paints a clear picture of how these engagements typically end. After weeks or months of employment, questions from teammates about work quality begin to surface. Workers may struggle with technologies listed on their resume, have difficulty communicating, or need excessive hand-holding on tasks like git branch management.
Performance improvement plans follow, then termination. At that point, coordination begins between the DPRK worker and their western collaborator about returning the corporate laptop and collecting the last paycheck. The cycle then restarts with a new identity, new profiles, and new applications.
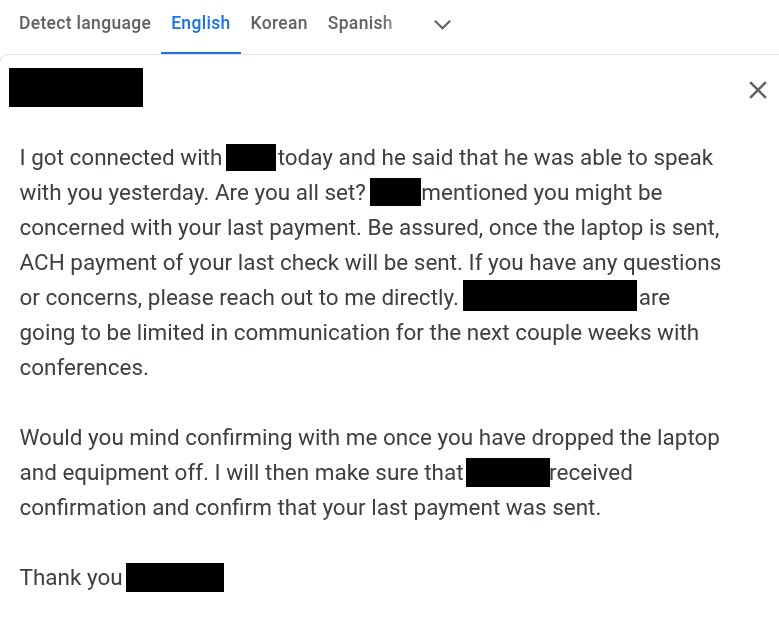
Google translation of a message from a manager about performance concerns
NKITWs understand this is temporary by design. They continuously shift between jobs, identities, and accounts.
What Security Teams and HR Can Do
Defending against this threat requires collaboration between security operations, human resources, hiring managers, and interviewers. Here are practical steps organizations can take:
During Hiring and Onboarding
- Conduct extensive identity verification and background checks, recognizing that western collaborators can help operatives bypass traditional vetting
- Exercise vigilance on video calls, look for signs of fake backgrounds, AI face changers, or AI voice changers
- Where possible, conduct interviews, laptop pickups, or onboarding steps in person
- Take seriously any discrepancies between resumes and what candidates say in interviews, especially regarding languages, skills, and location
After Onboarding
- Watch for noticeable differences between spoken and written communication styles, or between interview behavior and on-the-job behavior
- Monitor for suspicious VPN, proxy, or remote access software on workstations
- Check endpoint logs for DPRK-specific tools like NetKey or OConnect, or access to internal web pages associated with RB Site or NetkeyRegister
- Engage frequently with remote employees through video calls, NKITW operatives may quit roles that require regular face-to-face interaction
Forensic Indicators to Hunt For
- Installed software: NetKey (versions 4.1–5.1), OConnect (versions 5.3–6.0.0), IP Messenger
- File paths containing “rb corp” or “STN Corp”
- Browser history showing access to internal IPs like 192.168.109.2 or 172.20.100.7
- Extensive Google Translate usage patterns, particularly English-to-Korean translations
- Browser history showing visits to .kp domains
The Bigger Picture of NKITW Operations
North Korean IT worker operations are widespread and deeply integrated within the DPRK party-state. Teams are deployed across multiple government bodies, party organizations, and front companies, which makes this a ubiquitous presence rather than a single trackable group.
Because this approach has been so lucrative, NKITW tactics continue to evolve. Building close, personal relationships with candidates and employees from day one remains one of the most effective countermeasures. NKITW operatives thrive in environments of disengagement and will avoid roles where close personal interaction is expected.
The full report from Flare and IBM X-Force contains additional indicators of compromise, including email addresses, visited URLs, and installed software associated with NKITW operations.
Equip Security Professionals and HR Teams to Threat-Hunt
As remote work persists and AI makes persona creation easier, organizations need ground-level intelligence to detect and stop this threat.





