By Adrian Cheek, Senior Cybercrime Researcher
There’s an active campaign using fraudulent domains that specifically target Canadian residents, and may be targeting residents of other countries as well. The hosting provider supporting this activity has been publicly linked in prior research to Iranian nation-state aligned threat groups.
Our analysis found no clear evidence that the provider’s ownership, management, or operational practices have materially changed since these links were first documented in 2023, increasing the assessed risk associated with this infrastructure. This research focuses on understanding and highlighting the infrastructure used by threat actors to facilitate fraudulent activity.
Key Takeaways on the Phishing Campaign
- An active phishing campaign is currently targeting Canadian residents (and possibly present in other countries) using fraudulent domains impersonating trusted institutions, including the Government of British Columbia and Hydro-Québec, with the goal of harvesting personal information and credit card details.
- The phishing sites are designed to bypass basic validation, as demonstrated when deliberately fabricated personal details including an 1901 birth year and randomly generated contact information successfully passed the site’s verification process.
- The hosting infrastructure behind this campaign is linked to RouterHosting LLC / Cloudzy, a provider that was publicly accused in 2023 of supplying services to at least 17 state-sponsored hacking groups from countries including Iran, China, Russia, and North Korea.
- The scale of potentially malicious infrastructure is significant: of 134 Canadian-specific (.ca) domains identified on RouterHosting’s network, 58% contained language assessed as suspicious, referencing Canadian banks, utility providers, or payment-related terms.
- CIRA’s Canadian Presence Requirements appear to be exploited, as registering a .ca domain requires a verifiable connection to Canada, yet the fraudulent domains passed this requirement despite their clearly malicious purpose.
Phishing & Brand Protection
Detect Fraudulent Domains Impersonating Your Brand Before Victims Do
Active phishing campaigns are registering lookalike domains to impersonate trusted institutions — from government portals to utility providers — harvesting personal data and payment credentials at scale. Flare continuously monitors domain registrations, dark web marketplaces, and illicit Telegram channels so your team can identify spoofed infrastructure and credential leaks before they impact your customers.
The Phish: Impersonating Provincial Governments
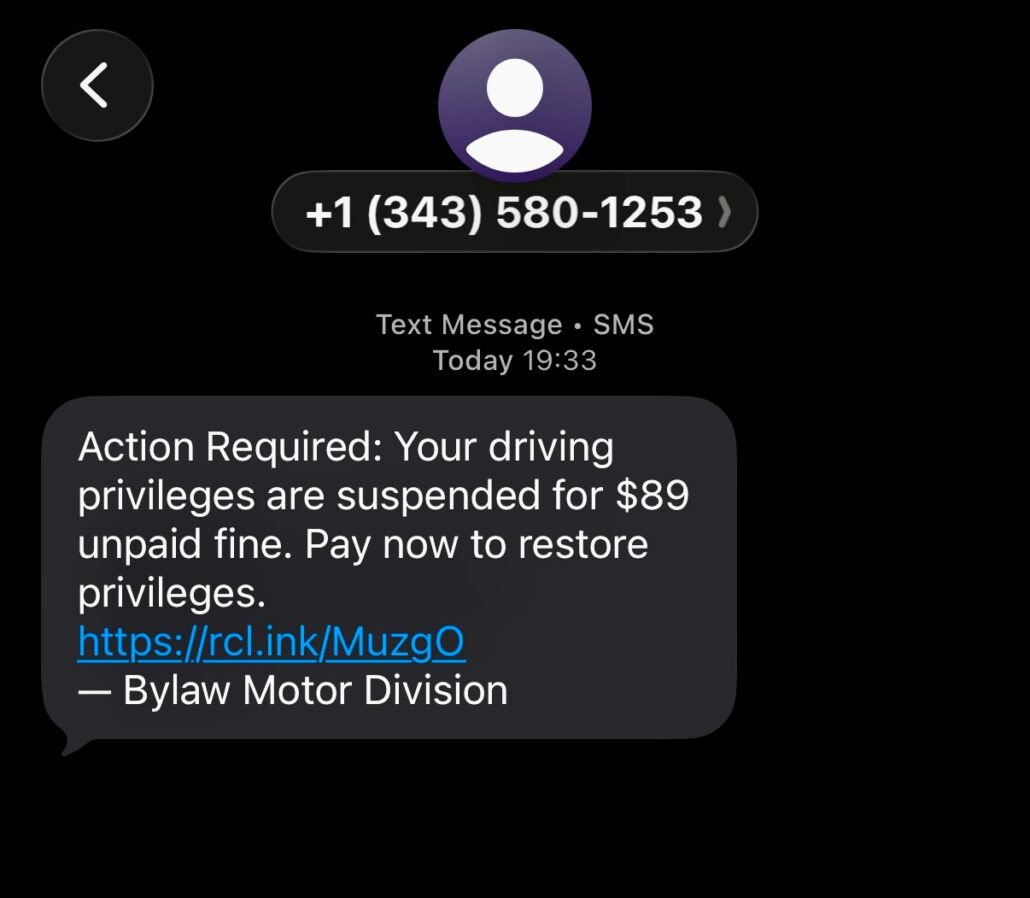
This text message link is no longer active and was sent by a user in British Columbia
Although the link in the message was no longer active, our research was able to recover the destination URL and identify it as a fraudulent webpage impersonating the Government of British Columbia, specifically the non-existent Court of Justice.
The fraudulent webpage shows a parking ticket
We examined where the domains were hosted and whether patterns in their activity could be identified. The analysis began by reviewing domain registration and routing information to better understand how the infrastructure supporting the campaign was organized.
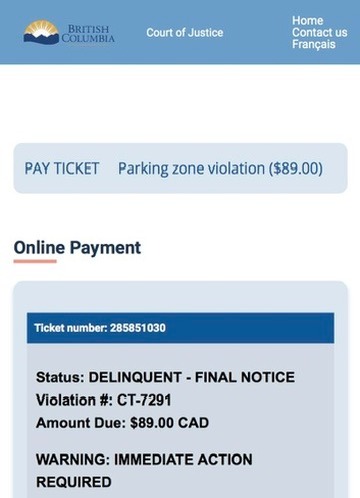
As we investigated the fake BC government domain we uncovered an additional domain, coveragesurcharge-reversal[.]ca, which was active at the time of writing and impersonated a billing accuracy notice purportedly from Hydro-Québec. The notice informed recipients that “recent system audits have identified that certain areas have been overcharged between January and March 2025” and advised that they “may be eligible for a refund,” prompting them to verify whether their area had been affected.
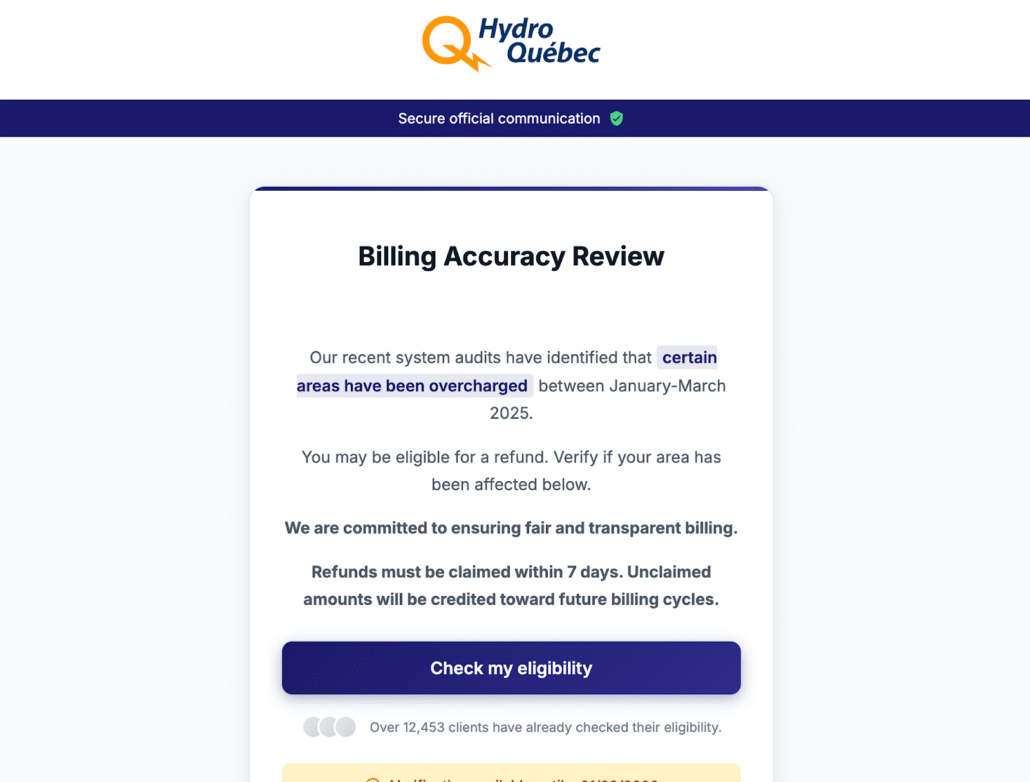
Fraudulent Hydro-Quebec domain hosted on coveragesurcharge-reversal[.]ca
By selecting the blue button, a potential victim is redirected to a new page where they are asked to enter personal details in order to “check eligibility.”
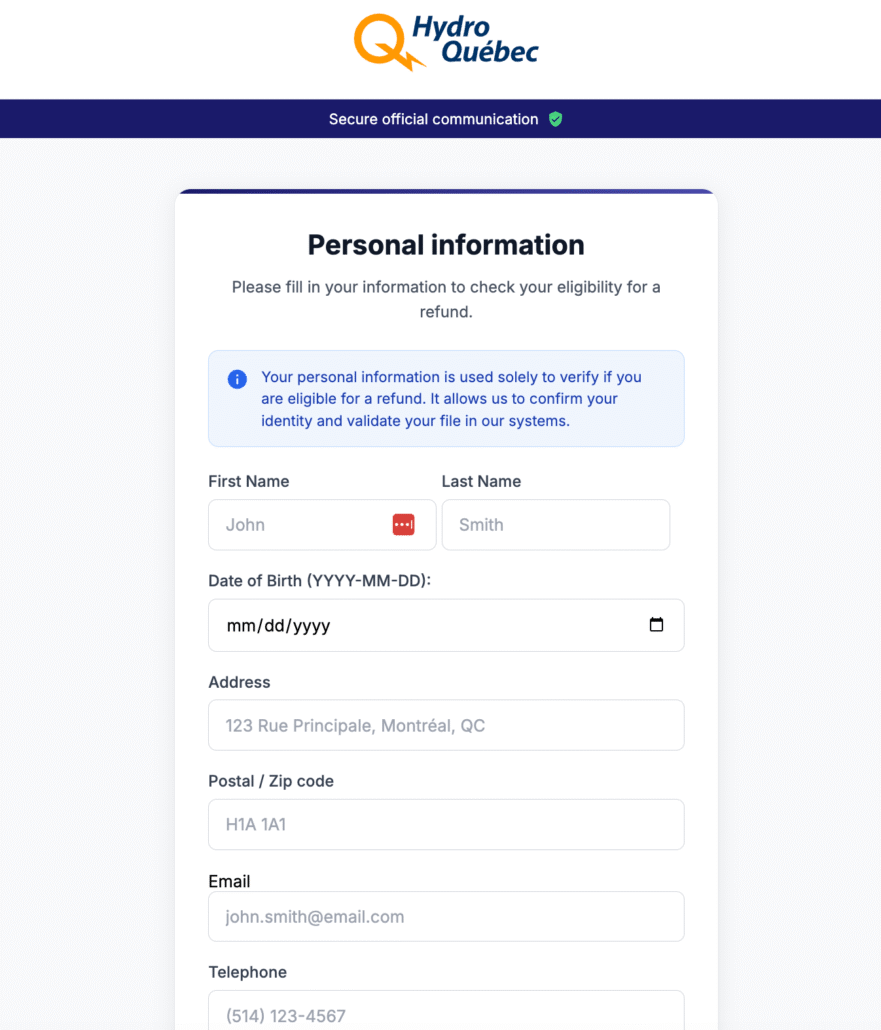
Personal information page on coveragesurcharge-reversal[.]ca
As part of our analysis, we submitted deliberately fabricated information, including addresses and postal codes from two different provinces, a date of birth using the year 1901, and a randomly generated telephone number. Despite these clearly invalid details, the information passed the site’s verification process.
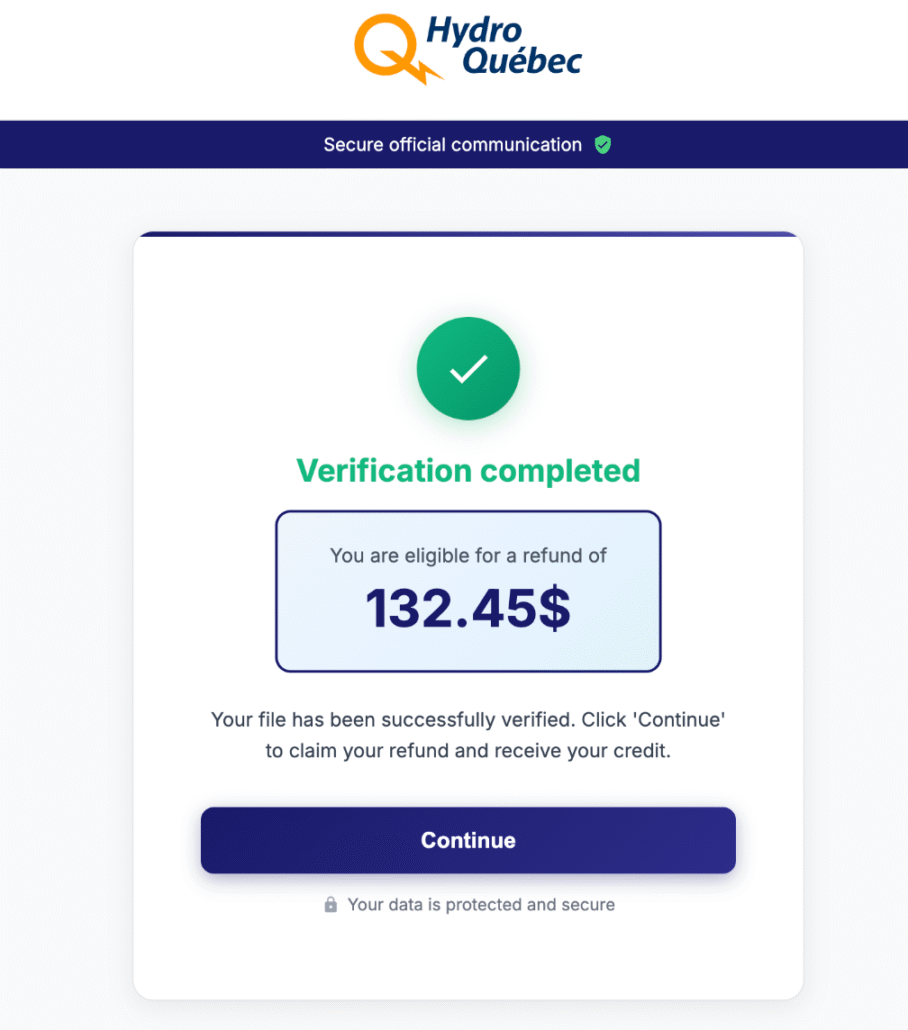
Page shows verification complete and a refund amount
After the form is completed, victims are redirected to a page describing the refund process and prompted to enter their credit card details. When combined with the previously submitted personal information, this data can be used directly for fraud or resold by the threat actors until the compromised card is ultimately blocked.
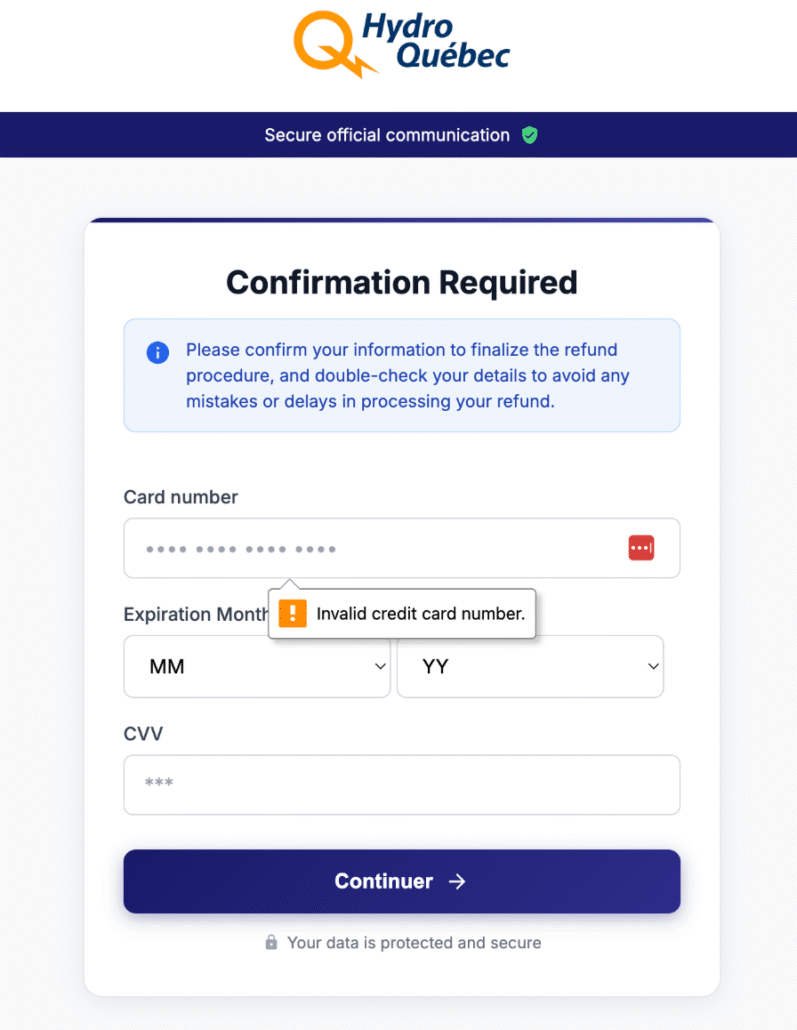
Credit card page on coveragesurcharge-reversal[.]ca
Network Infrastructure
Our network analysis began with the known domain, coveragesurcharge-reversal[.]ca, by examining the IP address used to host the site. This IP address also hosted eligibilityrequest-overchargereversal[.]info and eligibilityform-refund[.]info, which were registered on January 16th and January 19th, respectively. Analysis also showed shared SSL certificate data, which strongly suggests shared ownership, control, or management of the infrastructure for all three domains.
We then applied the same analysis to the URL received via the original text message. In this instance the domain shown was payinfraction-now[.]help on the IP 144.172.88.xxx. Also hosted on this IP address are the domains civicpenalty-resolve[.]ca, municipalinfraction-settle[.]ca, and alectra-eligibilityform-refund[.]ca. All of the domains were registered in January 2026, using different registrars, however in each instance the same ISP, RouterHosting LLC was used.
Using the collected infrastructure indicators, we conducted a query of domains hosted by RouterHosting LLC. Our query returned more than 28,000 domains at the time of analysis. To focus on activity potentially targeting Canadians, the results were filtered to domains using the .ca country-code, which is administered by the Canadian Internet Registration Authority (CIRA). Applying this filter reduced the dataset from over 28,000 domains to 134 at the time of writing. In the process of filtering we noted additional domain names which potentially matched the same naming conventions, but not targeting Canadian citizens, leading to a conclusion that this particular scam may be widespread targeting residents of other countries.
Each domain was reviewed to assess its likely purpose, as domain naming conventions can often provide insights into the intended use even when the domain is not active. Of the 134 .ca domains identified, 78 (58%) contained wording we assessed as suspicious, including terms such as “paiement,” “ticketcollection,” and “pendingticket,” as well as references to Canadian banks or Canadian utility providers. This figure does not account for additional domains registered outside .CA that were linked to the same infrastructure, such as ticketresolution-ca[.]help, which shared an IP address with pendingticket-reso[.]ca.
CIRA’s Canadian Presence Requirements (CPRs) mandate that anyone registering a .CA domain must have a verifiable connection to Canada, such as being a Canadian citizen, permanent resident, or an organization with Canadian ties. CIRA’s Terms of Service also state that conducting fraud, phishing, hosting malware, or engaging in illegal, harassing, or defamatory acts are illegal activities and constitute a breach of their terms.
To make a website accessible through an Internet Service Provider (ISP), the appropriate DNS records must be configured. Some domain registrars offer integrated DNS services, while other providers, such as RouterHosting LLC, must be explicitly added to the DNS configuration to enable access.
Who is RouterHosting LLC?
RouterHosting LLC was founded in 2008 by Hannan Nozari as a provider of virtual private server (VPS) hosting and remote desktop services. In 2022, the company rebranded as Cloudzy, and in 2024 relocated its headquarters to Dubai.
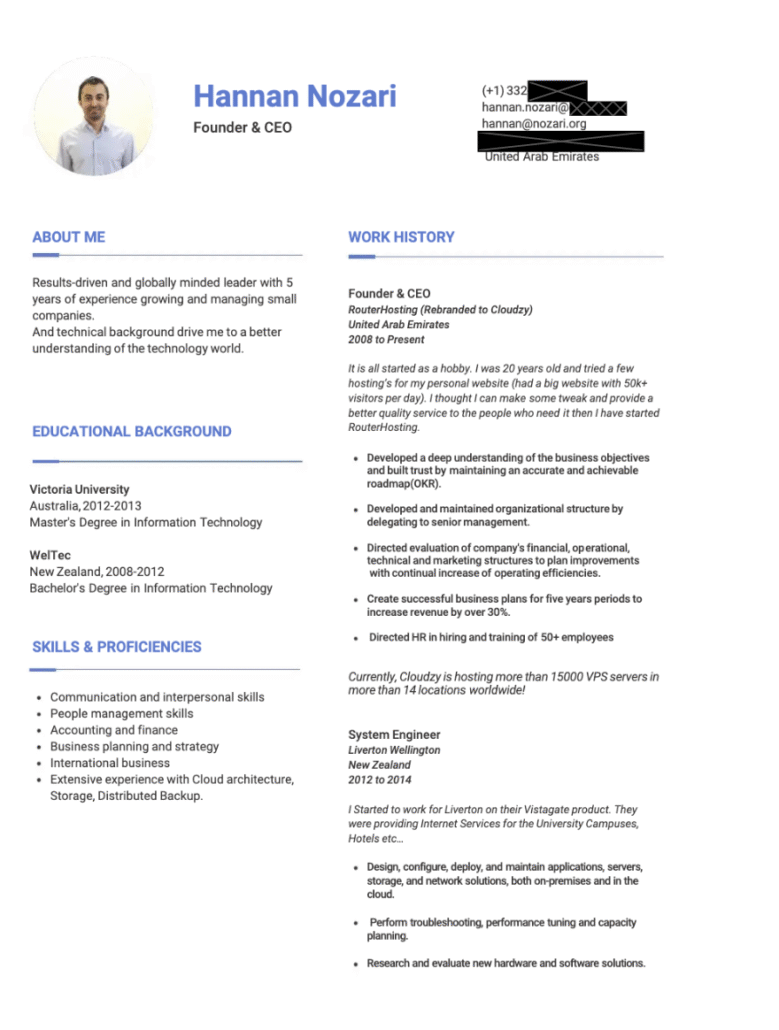
Screenshot of Hannan Nozari’s alleged resume (Source: Scribd)
While these corporate changes are not unusual on their own, reporting in December 2023 raised additional concerns. In an article titled “How cybercriminals are using Wyoming shell companies for global hacks,” Reuters referenced an earlier, August 2023 article which highlighted research conducted by the anti-ransomware firm Halcyon that accused an Iran-linked internet company called Cloudzy of providing services to “a rogues’ gallery” of digital spies and cybercriminals, in part through its U.S. registered entity, RouterHosting LLC, based in Sheridan, Wyoming.
In the research by Halcyon, entitled “Cloudzy with a Chance of Ransomware” it alleged that “a company called Cloudzy had been leasing server space and reselling it to no fewer than 17 different state-sponsored hacking groups from China, Russia, Iran, North Korea, India, Pakistan and Vietnam.” and it estimated “that roughly half of Cloudzy’s business was malicious, including renting services to two ransomware groups.”
The allegations were refuted by Nozari, who was quoted by Reuters stating that he had been “under the mistaken assumption that he needed it to buy internet infrastructure in North America” and “the Wyoming company had been dissolved.” Our research confirmed that RouterHosting LLC was dissolved in 2024.
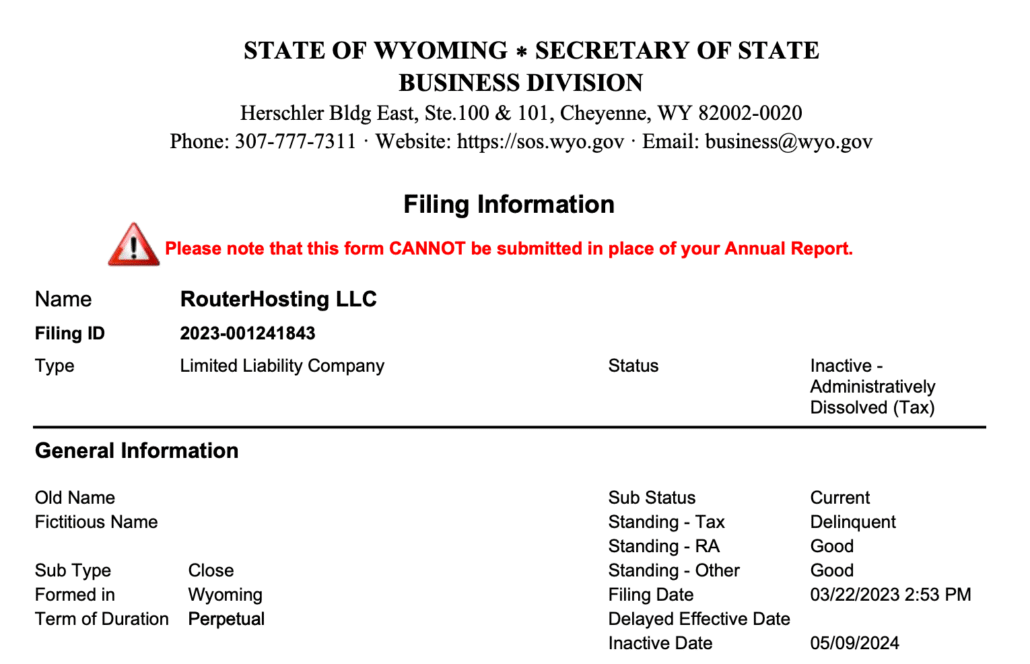
Screenshot of the Wyoming Secretary of State Business Centre filing information for RouterHosting LLC
ARIN (the American Registry for Internet Numbers) manages the distribution and registration of internet number resources, such as IP addresses and Autonomous System Numbers, for the United States, Canada, and parts of the Caribbean and North Atlantic. Under ARIN’s Section 8.2 transfer policy, organizations are required to document any changes in legal status or ownership. Organizations are also required to demonstrate they are a legal entity within the ARIN region, and this status must be verified annually.
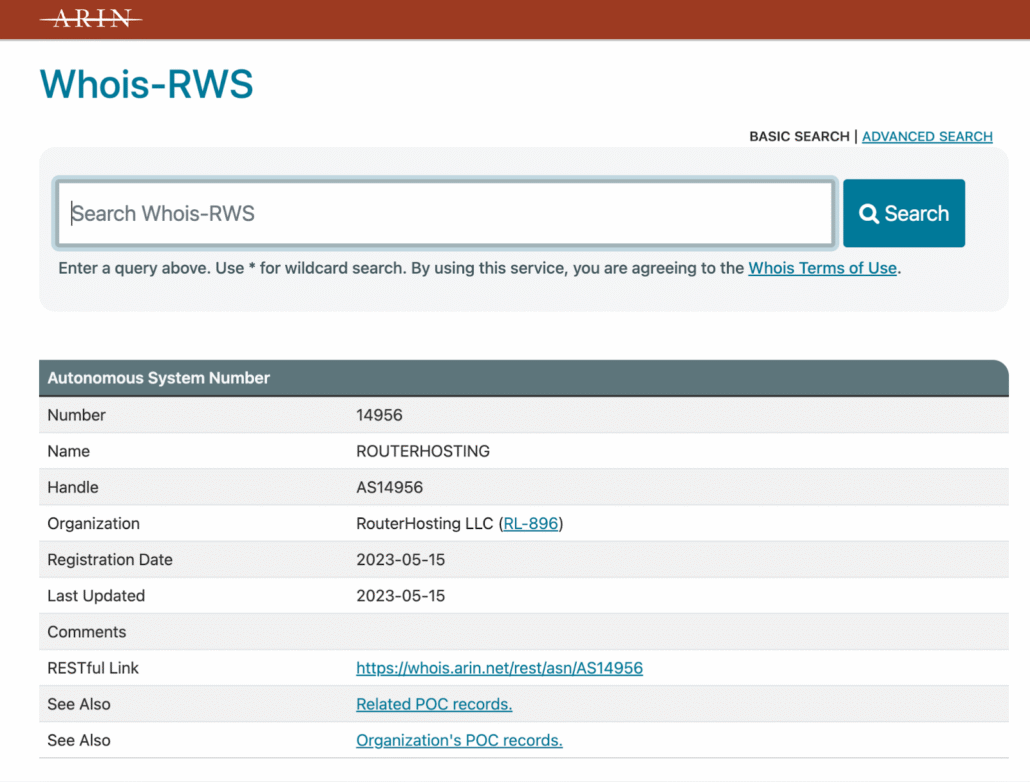
Screenshot of the current RouterHosting LLC record held by ARIN showing ASN assignment
ARIN’s official records show that the record for RouterHosting LLC was last updated in May 2023 and it continues to have an ASN number assigned to it. Additionally, despite being dissolved, the ARIN records continue to show the Wyoming address.

ARIN WHOIS record showing RouterHosting LLC still using a Wyoming address, despite being dissolved
We were unable to identify a verifiable physical presence for Cloudzy within the United States, despite the company’s public claims of U.S. incorporation. The company’s founder has publicly stated that Cloudzy’s headquarters are located in Dubai. Based on available information and public records, RouterHosting LLC appears to be a dissolved U.S. entity and, as such, would not meet ARIN’s eligibility requirements for the assignment of an Autonomous System number.
Cloudzy/RouterHosting’s Ties to State-Sponsored Hacking Groups
RouterHosting LLC appears to be the preferred ISP for a network of malicious scam domains actively targeting Canadian residents. Public records indicate that RouterHosting LLC is a dissolved U.S. entity and now operates as part of Cloudzy, a Dubai-based VPS provider. Despite this, Cloudzy/RouterHosting LLC appears to be operating an ARIN-assigned netblock, which requires a qualifying U.S. legal presence, and there is no evidence that the associated registration records have been updated since 2023, indicating a potential non-compliance with ARIN requirements.
Research published in 2023 by the anti-ransomware firm Halcyon alleged that Cloudzy provided services to at least 17 state-sponsored hacking groups linked to China, Russia, Iran, North Korea, India, Pakistan, and Vietnam, and that the company operated from a base in Tehran. If investigated and substantiated, these allegations could potentially place Cloudzy and organizations or services relying on its services in contravention of U.S. sanctions.
Appendix
Domains registered since December 2025 identified as a result of this research:
| Domain | Registered |
| coveragesurcharge-reversal.ca | 1/20/26 |
| pendingticket-reso.ca | 1/17/26 (Current Spam Text Domain) |
| etia.ca | 1/11/26 |
| civicpenalty-resolve.ca | 1/10/26 |
| municipalinfraction-settle.ca | 1/9/26 |
| alectra-eligibilityform-refund.ca | 1/8/26 |
| gca-error412.ca | 1/8/26 |
| relink-pcoptimum.ca | 12/31/25 |
| ticketmanagement-secu.ca | 12/13/25 |
| ca-accnc-secu.ca | 12/11/25 |





