This article was updated on September 30th, 2025.
While phishing attacks and malicious website links often lead to ransomware attacks, many deliver other types of malware. Over the last few years, threat actors have been increasingly relying on infostealer malware variants to obtain employee credentials.
One of the most common infostealer variants is RedLine, which at one point was the most popular stealer malware. According to Kaspersky’s research, RedLine was used in 51% of infostealer infections from 2020 to 2023. Although RedLine use has declined in recent years, it’s still widely used in attacks. Recent data from IBM showed RedLine as the fifth most used stealer variant, although Lumma is now the most popular.
What is Infostealer Malware?
Infostealer malware, also called stealers and infostealers, are a vital part of the cybercrime ecosystem. The information stolen during a stealer attack is packaged into stealer logs, which are often used later to perpetrate future attacks.
Information stealer malware is a type of Remote Access Trojans (RAT). Attackers typically infect a victim’s device by using a social engineering attack, delivering the stealer via malicious attachments, websites, or ads.
Are Your Credentials in a RedLine Log?
RedLine and other infostealers have compromised millions of devices. Flare monitors stealer logs across dark web marketplaces and Telegram channels—so you can find and remediate exposed credentials before attackers use them.
Once the stealer is downloaded to the victim’s device, it harvests sensitive information, like credentials saved in a browser, and sends that data back to the attacker.
Typical data collection methods include using:
- Form grabbers: intercept and copy data that users send in forms
- Keylogging: recording the keys that people strike on their keyboards
Most infostealer malware variants target:
- Online banking services
- Social media sites
- Email accounts
- FTP accounts
- eCommerce platforms
- Cryptocurrency wallets
Stolen information is compiled into a stealer log, and distributed or sold to other threat actors in cybercrime marketplaces on the dark web (like Russian Market), in threat actor forums, or using a messaging platform like Telegram.

Stealer logs, and the credentials they contain, are then used by those other criminals to launch their own cyberattacks.
What’s the role of stolen credentials in cybercrime?
Credential-based attacks are extremely common. Verizon’s 2025 Data Breach Investigation Report (DBIR) found that 88% of web application attacks in the last year started with stolen credentials. With the cybercrime landscape, stolen credentials typically are synonymous with stealer logs.
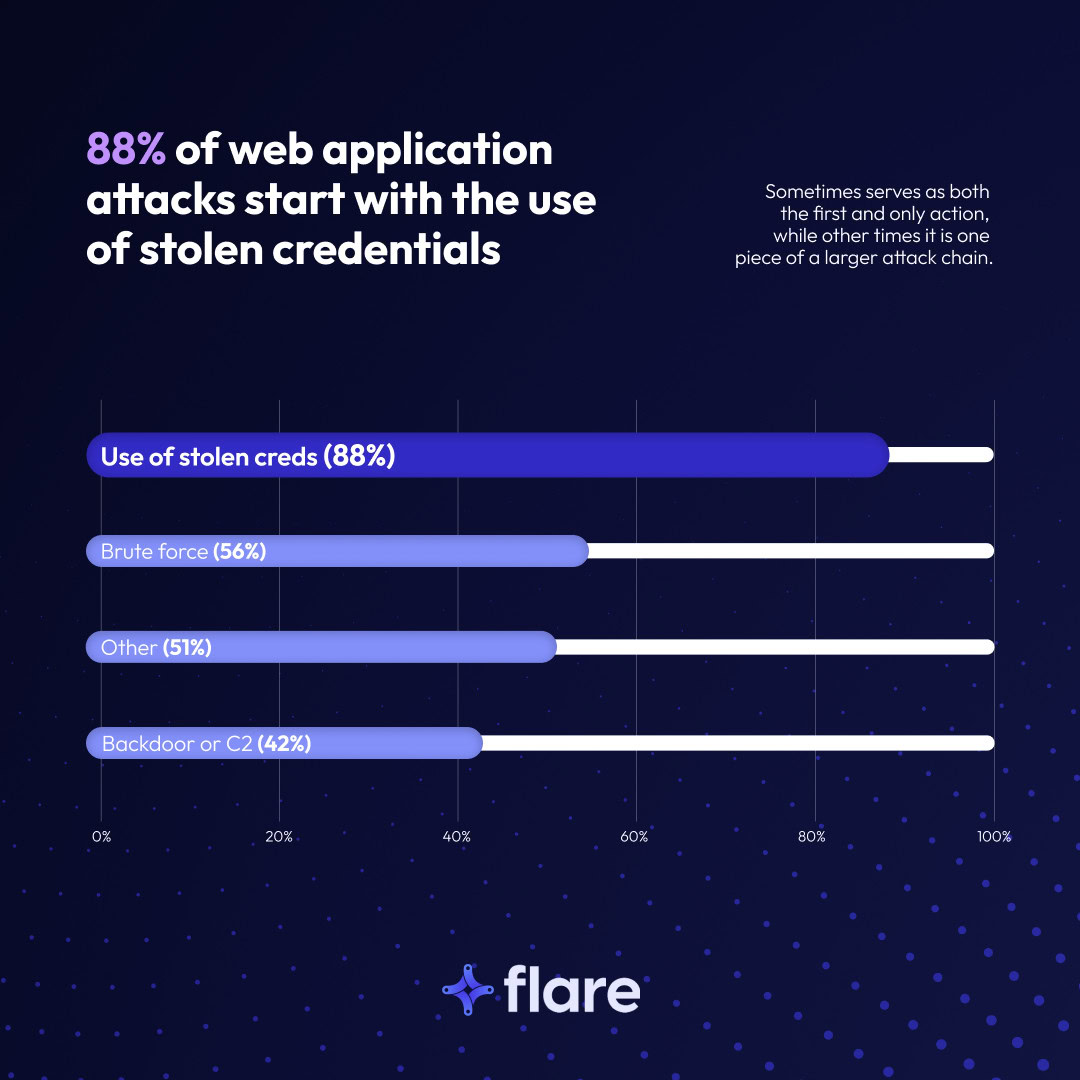
There’s also a strong correlation between ransomware and stealer logs. According to the DBIR, 54% of ransomware victims’ credentials were found in infostealer logs, and 40% of those logs included corporate emails.
While organizations have tried to prevent credential-based attacks by implementing multi-factor authentication (MFA), resourceful threat actors have found ways around MFA, either by using cookies to hijack sessions, or by barraging users with MFA notifications in MFA fatigue attacks.
What is RedLine Stealer?
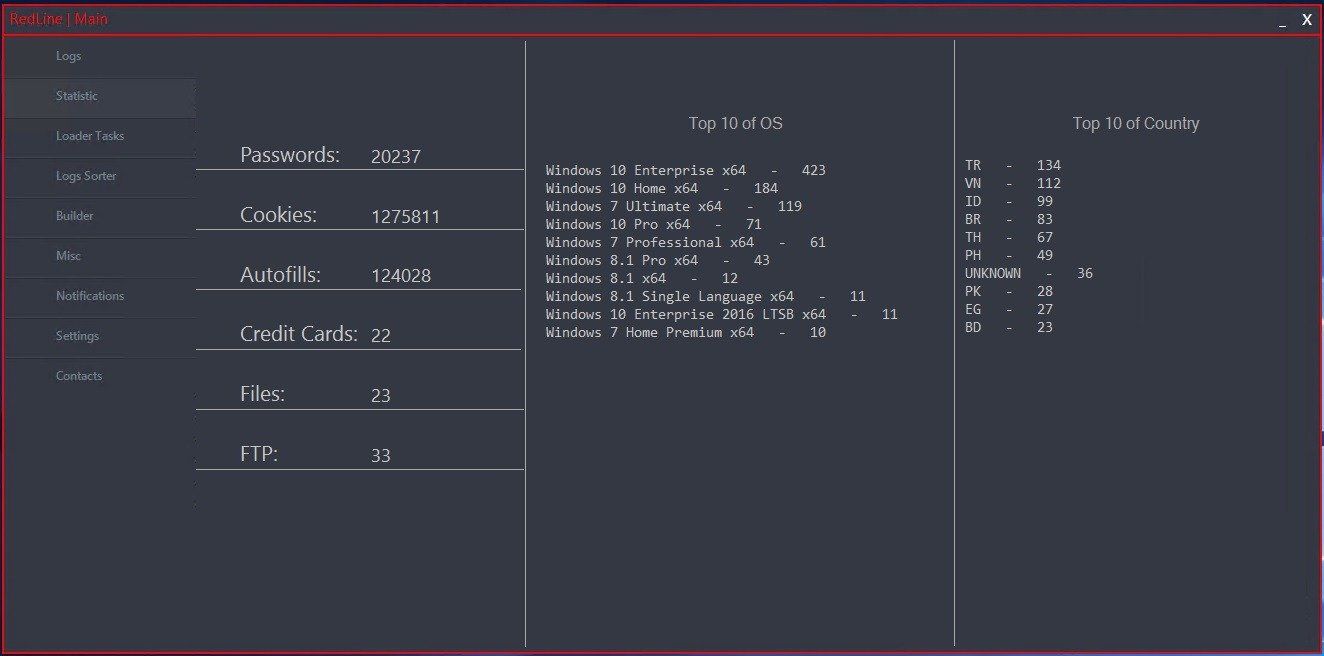
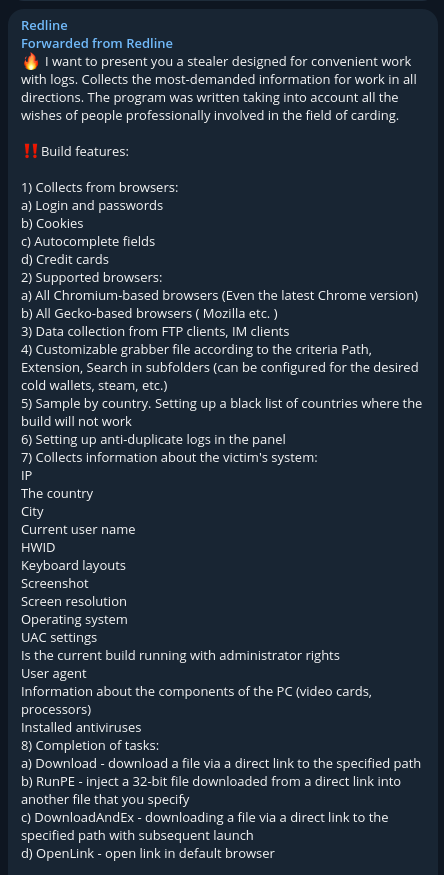
Originally discovered in March 2020, attackers initially delivered the RedLine malware in an email campaign, spoofing a legitimate coronavirus-cure research company email address. The RedLine infostealer variant offers a customizable file-grabber, enabling attackers to collect credentials from web browsers, cryptocurrency wallets, and applications, including:
- Chromium browsers
- Gecko-based browser, like Mozilla Firefox
- FTP clients
- Instant messaging applications
- VPN applications
RedLine collects the following information from users’ browsers:
- Logins and passwords
- Cookies
- Auto-fill form fields
- Credit card data
- Browser history
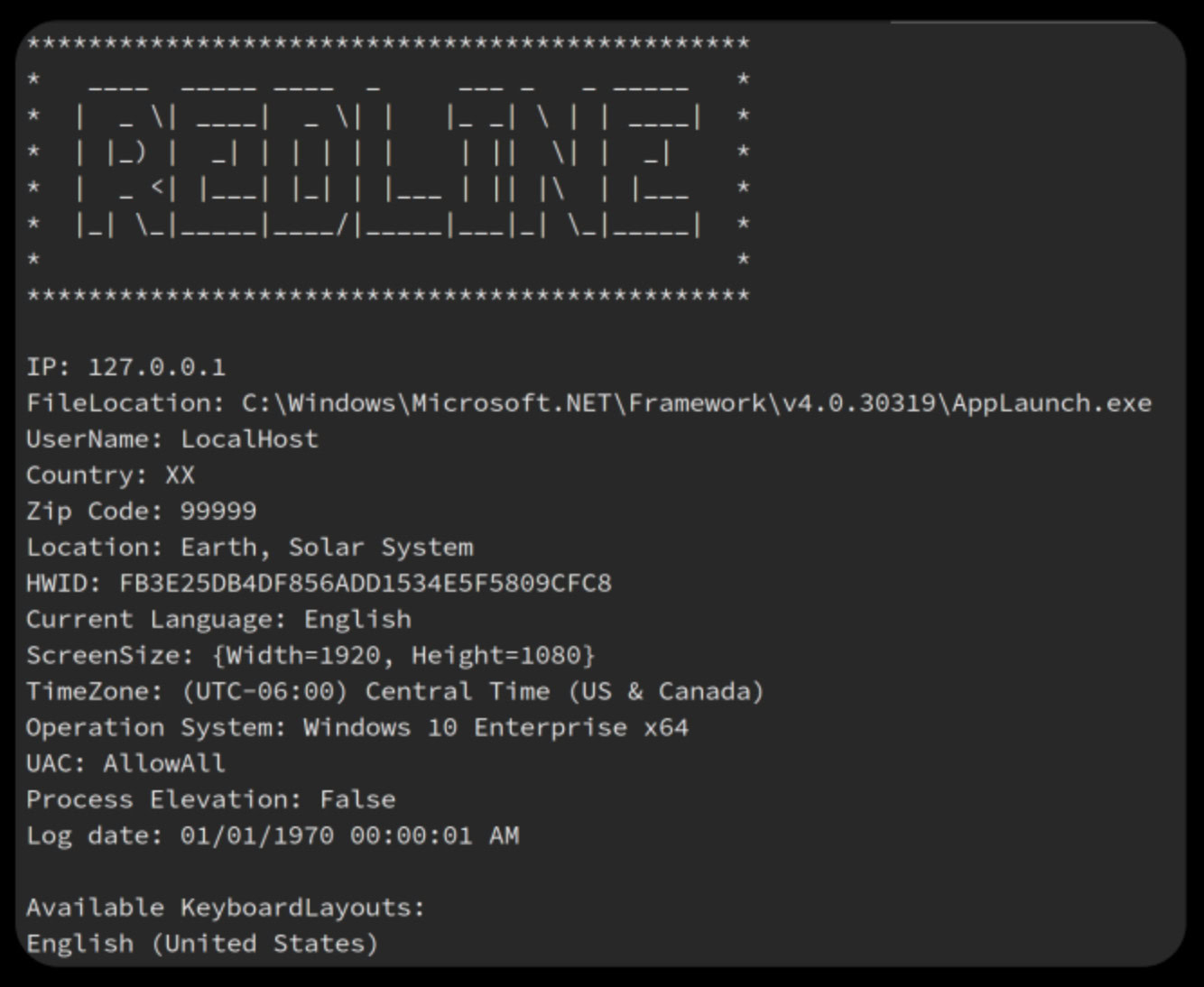
Furthermore, RedLine Stealer also collects information from the compromised device, including:
- IP address
- Country
- City
- Current username
- Hardware Identification (HWID)
- Keyboard layout
- Screenshots
- Screen resolution
- Operating system
- User Account Control (UAC) settings
- User-Agent
- PC hardware information
- Installed anti-virus tools
- Data about privileges running
- Data/files from common folders
Although RedLine Stealer has been around since 2020, malicious actors continue to deploy it. In January 2023, researchers observed malicious actors delivering the malware variant using OneNote files.
As organizations adopt more cloud-based technologies, malicious actors will increasingly seek to steal credentials and evolve their use of the RedLine Stealer malware.
RedLine enjoyed widespread use and popularity until October 28, 2024, when Operation Magnus disrupted RedLine’s infrastructure. Members of the Dutch National Police, the FBI, and other law enforcement agencies seized servers, domains, and Telegram channels associated with both RedLine and META.
However, despite the disruption, RedLine is still in use.
How Threat Actors Purchase and Use RedLine Stealer
RedLine stealer is a Malware-as-a-Service (MaaS), so threat actors can purchase it then sell the stolen data on dark web forums.

RedLine Stealer is a Malware-as-a-Service (MaaS), so threat actors can purchase it then sell the stolen data on dark web forums.
What is Malware-as-a-Service (MaaS)?
Malware-as-a-Service (MaaS) is the process of malicious actors following the Software-as-a-Service (SaaS) subscription business model to make money from their malicious code. The threat actors offer lifetime licenses or monthly subscriptions that include:
- Malware program
- Command and Control Center (C&C) infrastructure
The MaaS vendors do the same thing that SaaS vendors do:
- Offer access to an online platform
- Generate user accounts so customers can manage the attack
- Provide technical assistance when customers need help with the platform
With the subscription, malicious actors can receive, sort, and extract information from compromised devices’ logs.
How Does the MaaS Ecosystem Work?
The MaaS ecosystem consists of online forums acting as marketplaces. Three basic malicious actors need to interact:
- Someone selling malware
- Someone selling stolen data
- Someone who wants to use the stolen data to engage in other crimes, like fraud
Malicious actors advertise their malware on forums with listings that define the malware’s functionality, including:
- Data it collects
- Supported software
- Data collection locations
- Customization capabilities
- Platform’s settings
- Tasks it performs
After purchasing and deploying the malware, the customers then sell that data in dark web forums, like the Russian Market, with listings that typically include:
- Stealer malware family
- Device operating system
- Device country of origin
- Victim internet service provider
- List of service credentials available
- Archived directory content
- Device infection date
Want to learn more about the lifecycle of a stealer malware attack? Take a look at our report, Dissecting the Dark Web Stealer Malware Lifecycle with the MITRE ATT&CK Framework.
RedLine Stealer and Telegram Channels
Malicious actors increasingly use the Telegram messaging app to purchase and deploy their RedLine stealer malware.
Telegram is popular with threat actors for several reasons:
Illicit Telegram Groups Can Provide a Greater Sense of Anonymity
Dark web sources can be intensely monitored by cybersecurity teams and various law enforcement agencies. Telegram, however, is a bit trickier to monitor.
- Telegram’s “disappearing messages” feature allows channels to automatically delete messages after a certain amount of time
- The rapid flow of Telegram messages pushes older messages down the feed, making it difficult to find older messages, even if they still exist.
- Telegram’s strict privacy policies may make threat actors feel more secure
Illicit Telegram Groups Can Be Easier to Use
Compared to the difficulties of connecting to dark web sources, Telegram is much more accessible:
- The service only requires a mobile phone number (which can be hidden)
- Telegram channels do not require a domain to offer services and tools for sale
- If a Telegram channel is disrupted by law enforcement, it’s easy to set up a new one
- As long as the Telegram service remains online, so can threat actors
In addition, Telegram’s growth as a go-to messaging platform makes it a target for attackers. For example, malicious actors disguised one RedLine variant as a Telegram installer to evade detection.
Monitoring Stealer Logs with Flare
The Flare Threat Exposure Management solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors. Our platform automatically scans the clear & dark web and prominent threat actor communities 24/7 to discover unknown events, prioritize risks, and deliver actionable intelligence you can use instantly to improve security.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. See what external threats are exposed for your organization by signing up for our free trial.





