
By Flare Research
SiegedSec, commonly known as the “Gay Furry Hackers,” was a black hat hacktivist group created in April 2022 and directed by “YourAnonWolf.” Their primary purpose was political hacktivism, notably targeting threats to LGBTQ+ rights, right-wing movements, and US states passing anti-gender-affirming care legislation.
SiegedSec’s Origins and Ideology
SiegedSec first appeared on our radar in 2022 after they created their first Telegram channel and Twitter account shortly after. Early chat archives suggest that the group was founded and created by an individual using the alias “YourAnonWolf.” Since its inception, SiegedSec positioned itself as a hacktivist collective rather than a financially motivated operation, setting it apart from its counterparts in the cybercrime ecosystem at the time.
In December 2022, SiegedSec announced its first disbandment. However, this would become a recurring pattern over the course of their lifespan: the group disbanded or went dark multiple times, a tactic widely interpreted as an attempt to reduce media and law enforcement attention.
Their brand and ideology were clear from the start; they were not professional, often making jokes and posting cat gifs in their channels, and their techniques reflected a similar lack of sophistication. They notably used SQL injection as well as cross-site scripting (XSS) for a majority of their attacks. Due to the combination of low technical complexity, public-facing drama, and hacktivism-motivated attacks, a lot of cybersecurity analysts frequently made comparisons between SiegedSec and an earlier group from the 2010s, LulzSec. Both groups shared a flair for spectacle, a disdain for operational security, and a habit of taunting their targets publicly.
Track Threat Actor Groups Before They Target Your Organization
Flare continuously monitors Telegram channels, dark web forums, and breach databases where groups like SiegedSec announce targets, leak stolen data, and coordinate attacks — giving your team early warning to respond.
SiegedSec’s Breach History
In February 2023, SiegedSec announced in their Telegram channel that they had gained access to a global software company. They originally posted 35 megabytes worth of documents to the public as proof of the breach, including office floor plans and other files containing information on 13,000 employees. A few months later, SiegedSec posted leaks for the company as well as Sumerge, an IT services company based in Egypt, to BreachForums.
The group’s largest and most notorious hack occurred in July 2023, when they posted in their Telegram channel that they had breached the NATO Communities of Interest Cooperation Portal. The NATO COI is an unclassified information-sharing website used by NATO partner nations. SiegedSec claimed to have stolen hundreds of files, with the initial leak being around 845 megabytes in size.
This attack against the NATO COI was framed as politically motivated and retaliatory: “Do you like leaks? Us too! Do you like NATO? We don’t! And so, we present… a leak of hundreds of documents retrieved from NATO’s COI portal, intended only for NATO countries and partners”.
Not only do they share characteristics with other politically motivated squads like Anonymous, but they also have tendencies similar to groups like LulzSec. While flaunting their NATO hack, one member posted to the Telegram channel, “It’s fun to leak documents.” They have a mixture of organized, politically motivated hacktivism while also “doing it for the lulz,” and their name even resembles the LulzSec squad.
In July 2024, SiegedSec announced their “final hack.” They were able to breach The Heritage Foundation. The Heritage Foundation is an American conservative think tank founded in 1973 and considered among the most influential public policy organizations. The Heritage Foundation was responsible for leading “Project 2025,” which threatened the rights of abortion healthcare and LGBTQ+ communities. As a result, SiegedSec decided to make The Heritage Foundation their final target. They got into the database and stole user data, logs, and “200GB+ of useless files.” They then proceeded to leak the entire dataset of passwords, emails, and full names on Mega.
Whilst SiegedSec commonly referred to themselves as hacktivists and politically motivated, going through their archives on Flare, we noticed a pattern of less advanced attacks that had no clear political motivation. One example was in February 2025, just a few months after the Heritage Foundation hack was announced, the group posted to their Telegram channel that they had hacked the security camera system of Saint Elizabeth University.
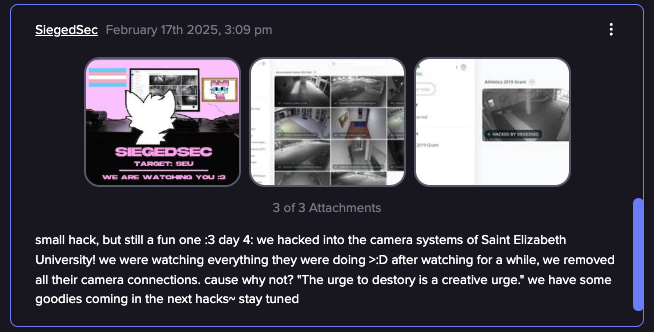
SiegedSec posted about hacking into camera systems (Flare link to post, sign up for the free trial to access if you aren’t already a customer)
This pattern echoes LulzSec’s legacy of hacking simply for the entertainment of it. Many of these smaller intrusions appeared opportunistic rather than planned, with group members seemingly acting on impulse when they spotted a vulnerability rather than selecting targets for their activist significance.
SiegedSec’s Tactics, Techniques, and Procedures
SiegedSec frequently demonstrated a consistent pattern of low technical sophistication in their attacks. The group primarily relied on widely known exploits, most notably SQL injection, misconfigured databases, and leaked credentials. These techniques show that this group wasn’t as advanced as some of the media portrayed them to be.
Operational security was minimal. They frequently claimed responsibility for attacks in real time on Telegram or Twitter/X, posting screenshots or small data samples as proof of breaching a certain target. While this approach clearly increased their media coverage and heightened their visibility, it also increased their exposure to law enforcement.
The group showed little evidence of lateral movement in any of their attacks, no custom-made malware, or long-term access to their victims. Instead, a majority of their jobs were of “smash and grab” in nature. Quickly getting into the systems from one of their techniques, dumping the data, then immediately posting on one of their social media accounts, disclosing the breach. This style aligned with their style of hacktivism, prioritizing publicity over operational depth.
The Inevitable End
SiegedSec’s rapid rise in notoriety made its downfall predictable. Hacking NATO put them on the radar of law enforcement agencies worldwide. In July 2024, just a few days after the hack against The Heritage Foundation, the group took to Telegram to formally announce its disbandment.
SiegedSec’s formal disbandment message
“
Hello everynyan!
The time has come for SiegedSec to disband :(
Yes, this is a sudden announcement. We planned to disband later today or tomorrow, but given the circumstances, I believe we should do so now. For our own mental health, the stress of mass publicity, and to avoid the eye of the FBI.
”
A few months after their formal dissolution, a few members came out and shared that “vio,” the leader of the group, was raided and arrested by the FBI. Although there has not been any evidence of this arrest happening, many independent journalists with experience covering the group’s antics reiterated the claim that a raid occurred.
SiegedSec’s brief but chaotic run serves as a textbook example of hacktivism’s double-edged nature in a modern setting. While their technical prowess may not have been memorable, the impact that they had on the companies they breached demonstrated that in the age of social media, publicity matters more than sophistication.
The group’s legacy is complicated. On one hand, they were successful in bringing attention to the political causes they deemed important, and exposed the lack of security and vulnerabilities in massive organizations. On the other hand, their operational security, attention-seeking behavior, and recklessness led to their eventual downfall and overexposure to law enforcement.
SiegedSec and Modern Hacktivism
In many ways, SiegedSec represented a new era of hacktivism, technically proficient enough to cause the damage and chaos they were able to cause for the short time that they were around. Their story serves as a cautionary tale about the consequences of poor operational security and a reminder to the world that hacktivist collectives rarely endure for long. Whether they will be remembered as a group of digital activists or just another group of script kiddies who got in way over their heads remains to be seen.
Track Threat Actor Groups Before They Target Your Organization
Flare continuously monitors Telegram channels, dark web forums, and breach databases where groups like SiegedSec announce targets, leak stolen data, and coordinate attacks — giving your team early warning to respond.





