By Tammy Harper, Senior Threat Intelligence Researcher
A sophisticated new ransomware-as-a-service (RaaS) operation named Vect has emerged on the Russian-speaking cybercrime forum Rehub. The developers claim a codebase written entirely from scratch in C++, with dedicated support for Windows, VMware ESXi, and Linux environments. With an aggressive affiliate program offering up to 88% commission and free access for CIS-based operators, Vect represents a significant new entrant in the enterprise ransomware ecosystem.
Information Gathered from the Vect Affiliate Panel
Intelligence gathered from the Vect affiliate panel reveals an already polished operation targeting enterprise hypervisors. The group’s “Partner Program” aggressively recruits CIS (Commonwealth of Independent States) actors with free entry while charging non-CIS affiliates $250 for access. The commission structure tops out at 88% for affiliates who generate over $75 million in ransom payments, indicating the developers are planning for large-scale “big game hunting” operations against enterprise targets.
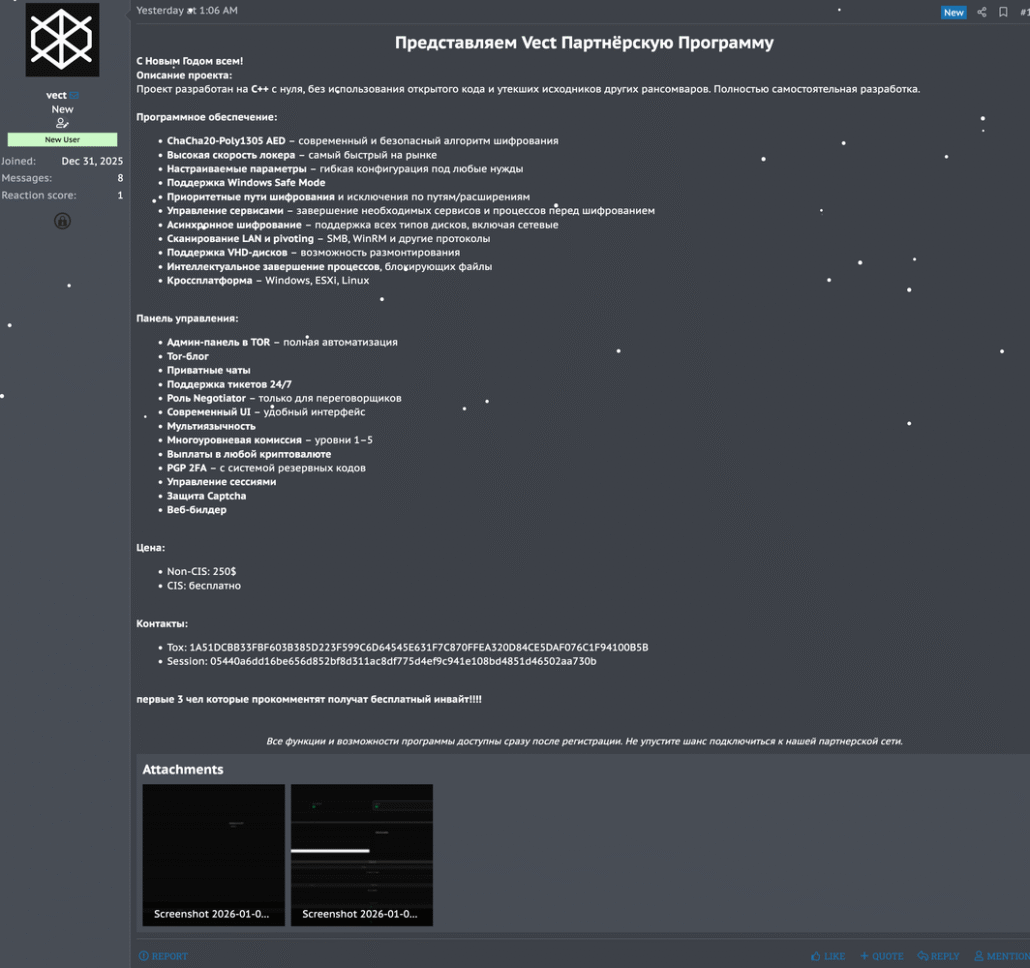
Vect ransomware advertisement on the Rehub cybercrime forum detailing features and affiliate program
Technical Analysis: ChaCha20 Encryption and the Speed vs. Security Tradeoff
Vect’s primary marketing claim centers on speed, boasting a “high speed encryption” engine built on the ChaCha20-Poly1305 algorithm. In forum discussions, the developer (username “vect”) claims encryption speeds of 1,750 MB/s on Samsung 980 PRO NVMe drives. However, when challenged by skeptical malware authors, the developer admitted this speed is achieved through intermittent (partial) encryption rather than full file encryption.
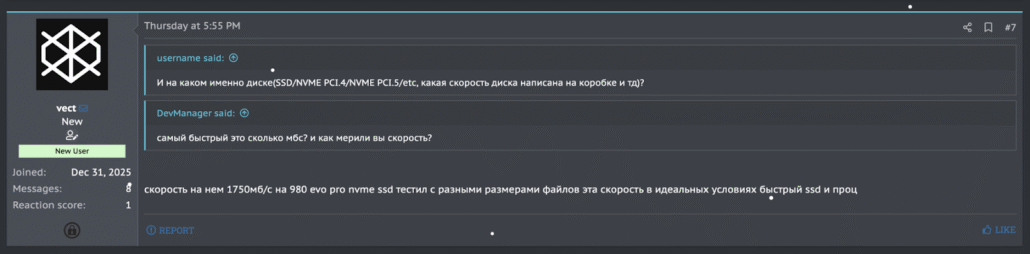
Vect developer claims 1,750 MB/s encryption speed on NVMe drives
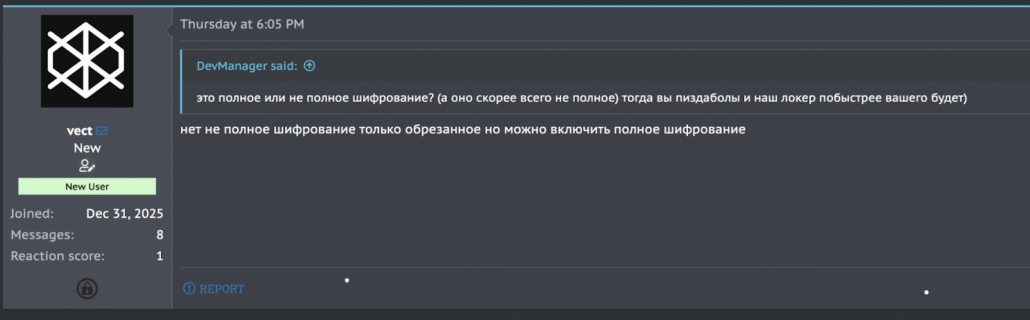
Vect developer admits the ransomware uses partial encryption by default
Understanding Intermittent Encryption
By default, Vect does not encrypt entire files. Instead, it “crops” or skips data blocks to maximize encryption speed. While this approach destroys files just as effectively from the victim’s perspective, it represents a known shortcut to bypass performance bottlenecks rather than a cryptographic breakthrough.
Intermittent encryption has become increasingly common among ransomware groups targeting enterprise environments where speed is critical. Encrypting only portions of large files (such as virtual machine disk images) allows attackers to render systems unusable much faster than full encryption would permit, reducing the window for detection and response.
Enterprise Deployment: Cross-Platform Builder and GPO Integration
The Vect builder interface confirms the ransomware is designed for mass deployment in hybrid enterprise environments. The panel provides dedicated compilation tabs for Windows, ESXi, and Linux targets, enabling affiliates to generate payloads for diverse infrastructure from a single interface.
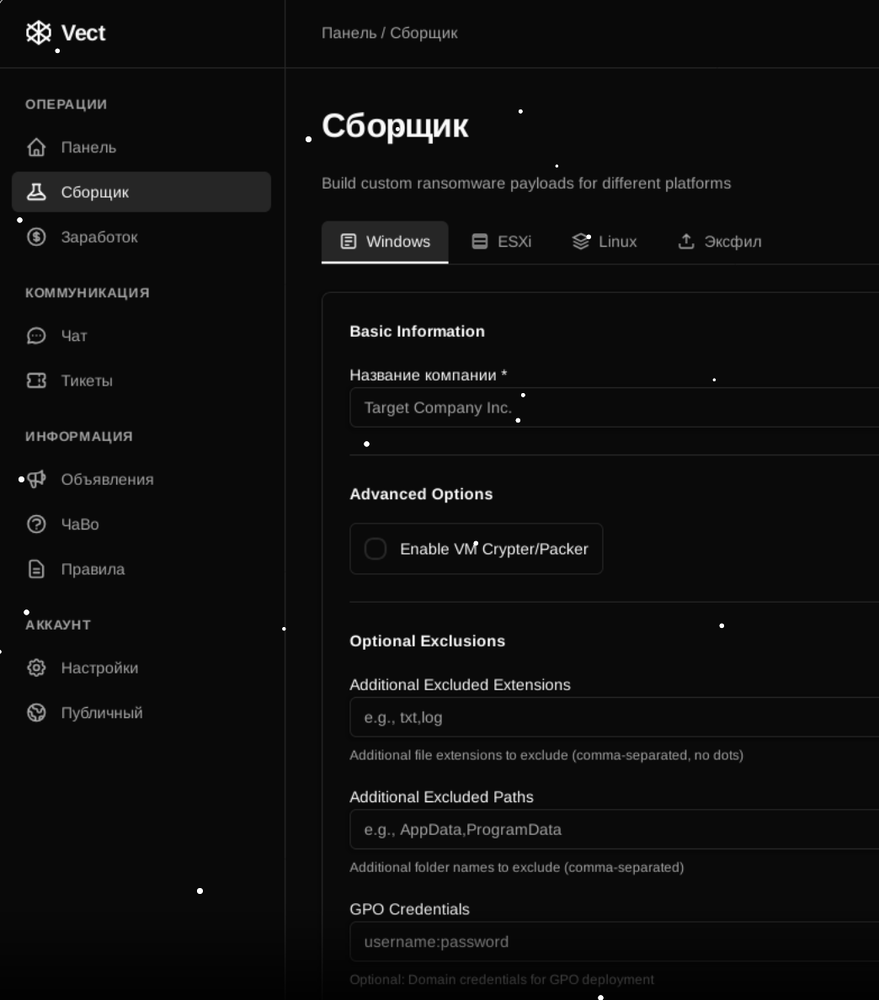
Vect builder interface with cross-platform support and GPO credential integration
Key deployment features include:
Cross-Platform Compilation: Dedicated tabs for Windows, ESXi, and Linux allow affiliates to target heterogeneous enterprise environments from a unified panel.
GPO Credential Integration: A “GPO Credentials” field allows affiliates to input Domain Admin credentials directly into the payload builder, enabling automatic distribution via Group Policy Objects without external scripts. This significantly streamlines mass deployment across Windows domains.
Built-in Evasion: A “VM Crypter/Packer” toggle standardizes anti-analysis techniques, protecting binaries from immediate signature detection by security tools.
File Exclusions: Configurable exclusion lists for file extensions and paths allow affiliates to avoid encrypting system-critical files that would prevent ransom note display or payment.
The Affiliate Program Economics
Vect utilizes a tiered commission structure designed to incentivize high-volume attacks and “big game hunting” operations against large enterprises. Analysis of the earnings dashboard reveals a five-level hierarchy based on cumulative ransom payments:
| Level | Revenue Threshold | Affiliate Share | Panel Share |
| 1 | $0+ | 80% | 20% |
| 2 | $5,000,000+ | 82% | 18% |
| 3 | $15,000,000+ | 84% | 16% |
| 4 | $35,000,000 | 86% | 14% |
| 5 | $75,000,000+ | 88% | 12% |
Vect’s tiered affiliate commission structure scales from 80% to 88%
The 80% starting rate is highly competitive compared to standard RaaS offerings, which typically begin at 70-75%. The $75 million threshold for the top tier indicates the developers are planning for long-term operations and expecting massive ransom payments from enterprise targets.
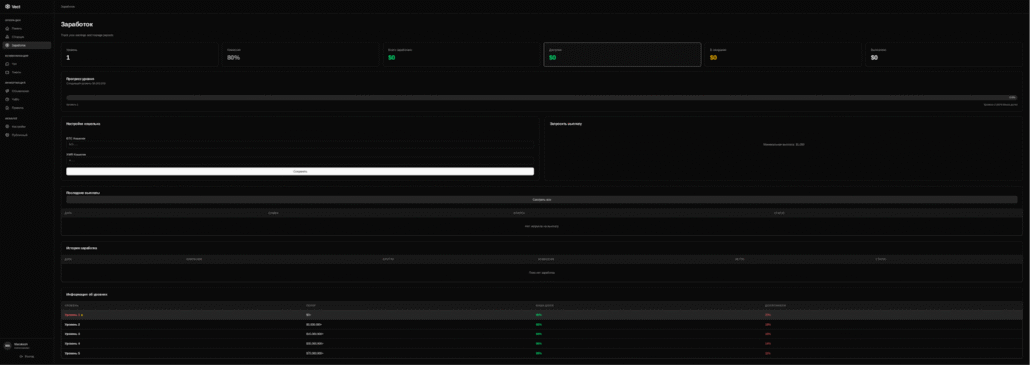
Vect earnings dashboard with cryptocurrency wallet configuration and level tracking
The panel supports withdrawals in Bitcoin (BTC) and Monero (XMR) with a minimum payout threshold of $1,000, ensuring the operation only deals with serious affiliates generating meaningful ransom payments.
Operational Strategy: The Negotiator Role and CIS Recruitment
Vect demonstrates a sophisticated understanding of the cybercrime supply chain by stratifying operational roles. The panel includes a specific “Negotiator Role” that separates technical intrusion specialists from the psychological extortion process. This division of labor allows technically skilled affiliates to focus on initial access and deployment while dedicated negotiators handle victim communications and payment extraction.
CIS-Focused Recruitment Strategy
The group employs a targeted pricing strategy to build a trusted core of Russian-speaking operators:
CIS Operators: Free entry to the affiliate program
Non-CIS Operators: $250 entry fee
Forum screenshots show immediate interest from Russian-speaking users, with potential affiliates explicitly stating “I am CIS… can I have an invite?” This confirms the effectiveness of the nationalist recruitment policy commonly employed by Eastern European ransomware operations to maintain operational security and build trust within the affiliate network.
The Vect Data Leak Site
Security researcher RaaZ identified a Vect data leak site (DLS) hosted at 158.94.210[.]11:8000. At the time of this analysis, the site is no longer accessible, suggesting the group may be transitioning infrastructure or operating in stealth mode before launching attacks.
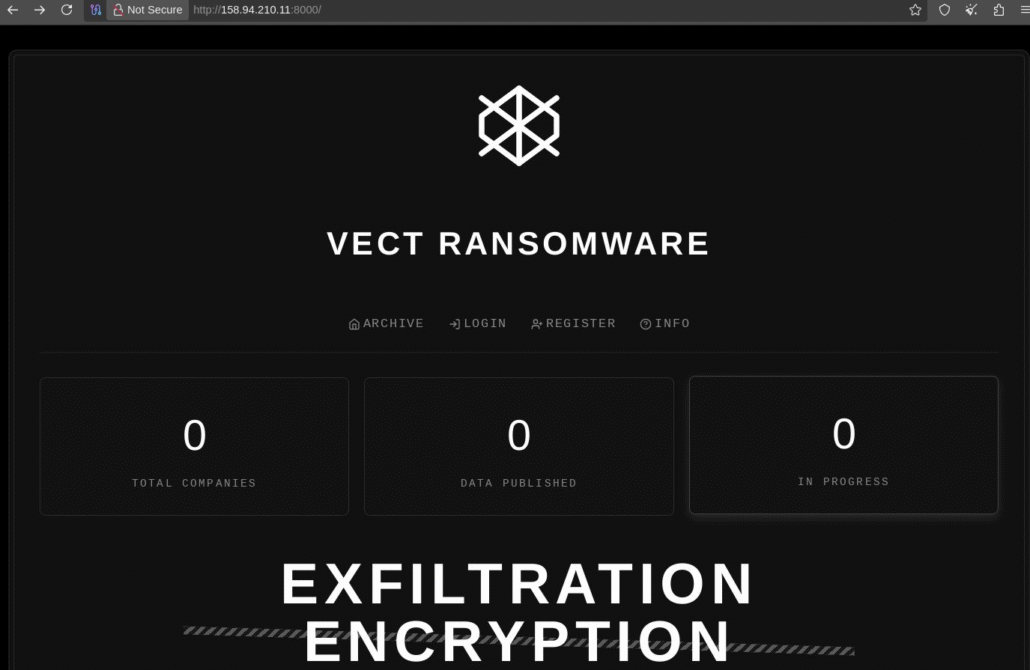
Vect data leak site showing no published victims at time of discovery
The DLS interface shows zero victims at the time of discovery, with counters for “Total Companies,” “Data Published,” and “In Progress” all showing zero. This suggests Vect is a newly launched operation that has not yet conducted public extortion campaigns, though private negotiations may be underway.
Threat Intelligence Implications
Vect’s emergence highlights several trends in the ransomware-as-a-service ecosystem that security teams should monitor:
ESXi and Hypervisor Targeting: The dedicated ESXi compilation option confirms that enterprise hypervisors remain high-value targets. Organizations running VMware environments should prioritize patching and access controls for management interfaces.
GPO-Based Deployment: The integrated GPO credential functionality lowers the technical barrier for mass deployment across Windows domains. Detection of unusual Group Policy modifications should trigger immediate investigation.
Intermittent Encryption Adoption: More ransomware groups are adopting partial encryption to maximize speed. Security tools should not rely solely on encryption behavior patterns for detection.
Role Specialization: The formal Negotiator role indicates continued professionalization of ransomware operations. Organizations should prepare for sophisticated social engineering during ransom negotiations.
Competitive Economics: The 80% starting commission and escalating tiers may attract experienced affiliates from other RaaS programs, potentially accelerating Vect’s operational tempo.
Indicators of Compromise (IOCs)
Organizations should monitor for the following indicators associated with Vect:
Data Leak Site IP: 158.94.210[.]11:8000 (no longer active)
TOX ID: 1A51DCBB33FBF603B385D223F599C6D64545E631F7C870FFEA320D84CE5DAF076C1F94100B5B
Session ID: 05440a6dd16be656d852bf8d311ac8df775d4ef9c941e108bd4851d46502aa730b
Encryption Algorithm: ChaCha20-Poly1305 (intermittent encryption by default)
Target Platforms: Windows, VMware ESXi, Linux
Recommendations for Security Teams
Organizations should implement the following controls to defend against Vect and similar enterprise-focused ransomware:
1. ESXi Hardening: Restrict management interface access, enable lockdown mode, and ensure ESXi hosts are patched against known vulnerabilities.
2. GPO Monitoring: Monitor for unauthorized Group Policy modifications and unusual GPO deployments, particularly those distributing executables.
3. Domain Admin Protection: Implement privileged access workstations (PAWs) and time-limited administrative credentials to reduce the impact of credential theft.
4. Network Segmentation: Isolate hypervisor management networks and implement strict access controls between network segments.
5. Backup Verification: Ensure offline backups exist for critical systems, particularly ESXi datastores and domain controllers.
What Security Teams Can Keep in Mind About Vect
Vect represents a professionally developed ransomware-as-a-service operation with clear focus on enterprise environments. The combination of cross-platform support, GPO integration for mass deployment, competitive affiliate economics, and role specialization indicates a mature understanding of both technical attack chains and cybercriminal business models.
While the operation appears to be in early stages with no confirmed victims, the polished infrastructure and aggressive CIS recruitment suggest Vect affiliates may begin active campaigns soon. Organizations with VMware ESXi environments and Windows Active Directory domains should prioritize the defensive recommendations above and add Vect indicators to their threat intelligence monitoring.
The $75 million top-tier threshold in the affiliate program signals the developers’ ambitions for large-scale “big game hunting” operations against enterprise targets. Security teams should prepare for potential attacks by reviewing incident response plans and ensuring backup and recovery procedures are tested and functional.
Monitor for External Threats with Flare
The Flare Threat Exposure Management solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors. Our platform automatically scans the clear & dark web and prominent threat actor communities 24/7 to discover unknown events, prioritize risks, and deliver actionable intelligence you can use instantly to improve security.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. See what external threats are exposed for your organization by signing up for our free trial.