By Flare Research
“You’re from a country that is under sanctions. If you’re still interested in the role, I need to confirm whether you’re comfortable working under someone else’s identity.”
– North Korean IT worker recruiting from other countries for their employment fraud strategy
Recent research into the NKITW operation uncovered evidence that the North Korean regime is likely hiring, with intention, individuals from Syria, Saudi Arabia, and Iran as part of its IT worker infiltration program, creating new urgency to improve employment verification.
With high confidence, Flare Research finds that North Koreans are deliberately targeting US defense contractors, cryptocurrency exchanges, and financial institutions. While the primary motivations appear to be financial, the deliberate targeting evidenced from their documents indicates that there may be other objectives at play as well.
The world wouldn’t be interesting without a little bit of irony. And there’s something genuinely poetic about discovering that North Korea, a country literally dubbed “the hermit kingdom,” has been quietly outsourcing one its most iconic exports: paid infiltrators whose mission is to gain employment at firms within the United States, Canada, and Western Europe.
After the release of a joint publication in early March with IBM X-Force, “Inside the North Korean Infiltrator Threat,” Flare Research drilled down further into the inner workings and nuances involved in the NKITW scheme. This report aims to provide additional detail into the process of how the DPRK receives siphoned money and intellectual property by infiltrating Western organizations, specifically by recruiting individuals from sanctioned countries by the United States, the European Union, and the United Nations. Please note that all information contained in this report was legally obtained and has been turned over to US Federal Law Enforcement, who did not ask us to withhold any information from publication.
Key Findings
- There is evidence from systems believed to be operated by NKITWs, detailing the recruitment of individuals from Iran, Syria, Lebanon, and Saudi Arabia.
- At least two Iranians received formal offer letters from US employers.
- Multiple major US defense contractors, cryptocurrency exchanges, and financial institutions appeared to be directly targeted by North Korean IT workers.
- There is evidence of more than 10 instances of Iranians being directly recruited by the North Korean regime.
- Documents confirming NKITW successfully reached fingerprinting and final stages within the hiring process of major telecommunications and defense companies.
Equip Security Professionals and HR Teams to Stop Fraud
Flare provides ongoing monitoring for North Korean IT worker indicators of compromise, including email IOCs for HR teams screening candidates and URL and installed software IOCs for security teams validating current employees.
The North Korean IT Worker Threat
North Korea has a revenue problem. Under international sanctions, the country is denied access to traditional means of global capital exchange and seeks to fund its regime through non-traditional methods. One such scheme is operated through the global remote work market where identification of individuals is difficult to enforce. The result is a state-sponsored program that deploys thousands of technically skilled workers overseas and online, operating under false identities to secure jobs at Western companies and funnel the income back to the regime.
The US Departments of Justice, Treasury, and State independently issued advisories on the threat, and multiple indictments have been unsealed. Companies ranging from early-stage startups to Fortune 500 firms have unknowingly hired DPRK nationals, with workers ranging from very competent to inefficient.
The operational model is straightforward in concept if not in execution. Workers assume fabricated personas, complete with polished LinkedIn profiles, GitHub histories, and references. They rely on networks of facilitators inside the United States to receive work laptops, manage payroll, and handle logistics that would otherwise require a physical presence. When a biometric check or background verification threatens to surface the deception, the job gets quietly abandoned, and the cycle starts again somewhere else. The operational model is detailed in more depth in the recent research with IBM X-Force.
Through thinly veiled shell companies, facilitators are recruited by offering an enticing proposition of interfacing with clients for two to three hours a week, earning at least $5k per month, while the development work is handled by someone else: a revenue share model.

A North Korean-operated GitHub profile, recruiting software engineers in the US and Europe. While this particular account was hiring for US and European developers, it is not the only geography the workers recruit from
Inside the Operation: Weekly Reports, Code Names, and Hiring Plans
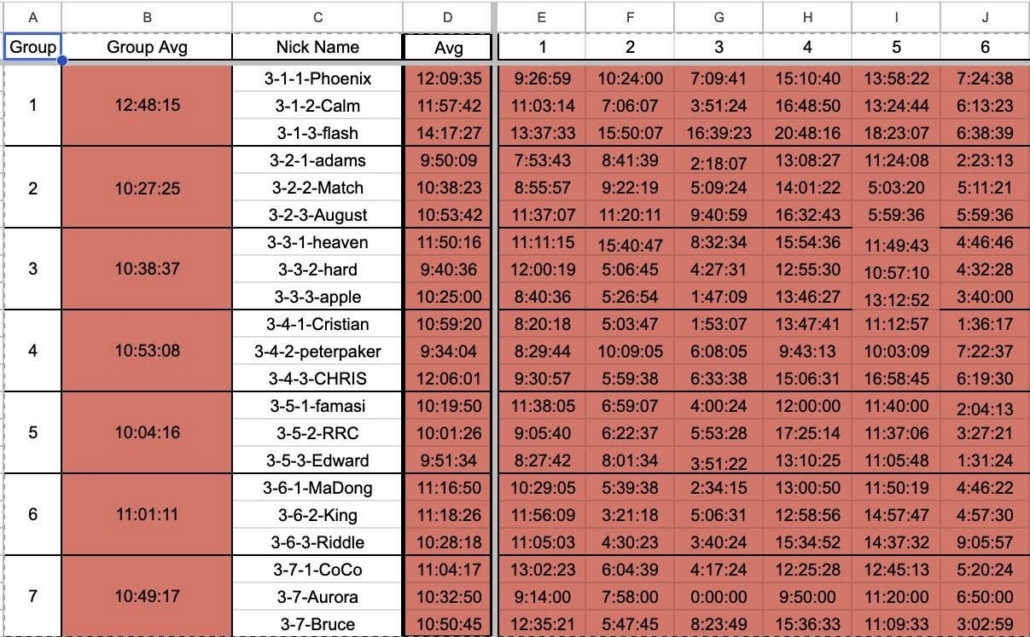
An internal timesheet displaying the code names and working times of groups of North Koreans with rankings
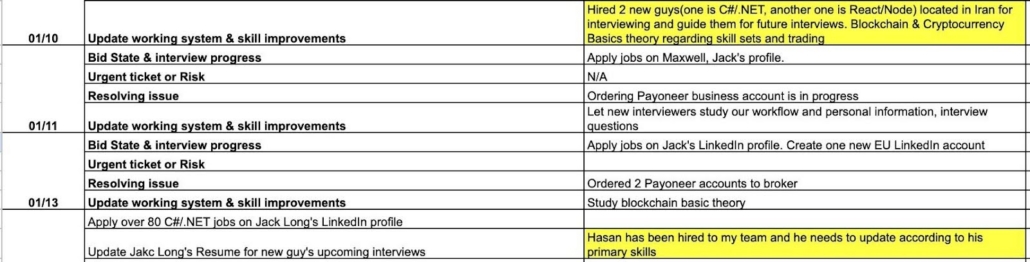
Numerous internal documents uncovered trace back to the North Korean regime. These documents point to a coordinated and orchestrated campaign to recruit Iranians, and others, in illicit operations which target cryptocurrency firms, defense contractors, and other US critical infrastructure.
One challenge seen repeatedly from IT workers, is maintaining employment for an extended period of time. This image reflects an uncovered document in which the NKITW are tracking the number of applications per individual and group, using code-names to ascertain efficiency in getting hired.
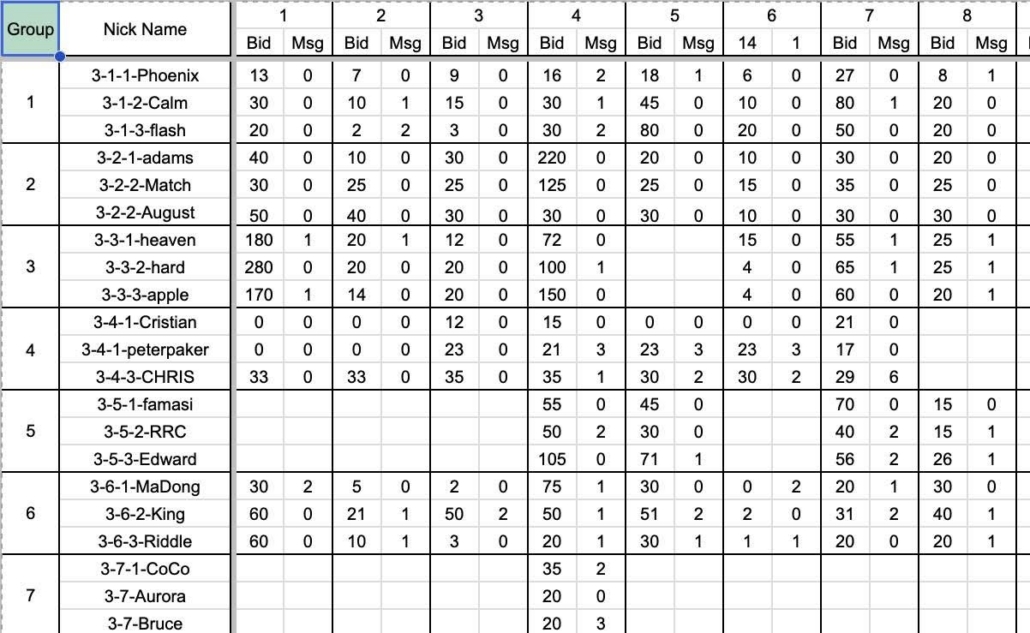
Tracking sheet of applications per individual and group
This allows the North Koreans to focus on obtaining the jobs while outsourcing the actual interviews and work to individuals in other countries. The documents obtained show that North Koreans are applying for thousands of roles per day at organizations ranging from defense contractors to community credit unions.
Targeted Entities
The internal weekly reports show explicit targeting. One facilitator’s task sheet lists a job at one of the largest US defense contractors with the status “will be the final step next week.” Another entry from a different facilitator reports that a position at a major US telecommunications company “will be terminated this week because of finger print test,” indicating the operative made it deep into the onboarding process before a biometric check, which will certainly catch the deception. A third facilitator received a formal offer from a US enterprise software company at $125,000 per year, and successfully completed onboarding, background checks, and laptop delivery.
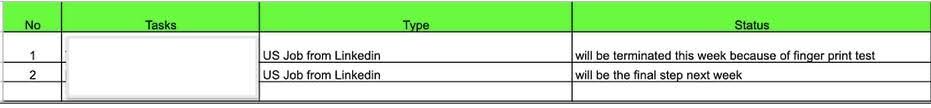
A screenshot of a North Korean spreadsheet showing they sourced a job from a major US defense contractor that will “be in the final step next week”
The cryptocurrency and blockchain sector appear also as a deliberate focus. Multiple facilitators track blockchain-specific Upwork bids and freelance projects separately from their general job applications, while simultaneously studying “Blockchain & Cryptocurrency Basics theory regarding skill sets and trading” as noted in some uncovered documents. Financial institutions are similarly in the crosshairs, with one facilitator’s weekly report documenting active onboarding with a US community credit union, including configuring I-9 employment verification forms and attending standup meetings with the company’s development team.
Multiple facilitators distinguish between their own role (managing profiles, applying for jobs) and hiring separate people to conduct phone screens and technical interviews. These “callers” or “interviewers” are recruited from various countries including, Iran, Ireland, India, and elsewhere, then guided and mentored. When a caller fails an interview, the facilitator reviews the recording and provides feedback, essentially running an interview coaching operation.
Hiring from Tehran: The DPRK’s Iranian Recruitment Pipeline
The weekly reports don’t just reveal how North Korean IT workers operate. They also reveal a large and coordinated network.
Across multiple facilitator reports, recovered independently a consistent pattern emerges: DPRK facilitators appear to be actively and deliberately recruiting software developers in Iran to serve as “interviewers” and “callers.” These are the workers who actually get on the phone with American hiring managers, pass technical screenings, and impersonate the real or fake Western personas that the North Korean operation curates.
Operator Sea: C#/.NET Developer
This isn’t incidental. At least three separate facilitators, operating what appear to be independent cells, were simultaneously recruiting Iranian developers during the same period, as stated in their internal tracking documents.
An internal spreadsheet showing the operator “Sea” explicitly stating they hired Iranians
Within a few weeks, new hires are integrated into the operation. A North Korean IT worker under the code name Sea writes:
“Guide new C# guy for upcoming interviews – Hasan in Iran”
Hasan is assigned to the “Jack Long” persona, a fabricated American C#/.NET developer whose LinkedIn profile Sea maintains. Sea updates Jack Long’s resume to match Hasan’s actual skillset, then starts applying for over 100 C#/.NET jobs per day under that name. When companies call back, Hasan takes the interview.
By February 7, Sea hires another Iranian developer:
“Hire new C# interview – Hamid in Iran”
February 8:
“Prepare profile and guide new guy for future interviews – Hamid in Iran”
And by February 10, the individual hiring decisions have become an explicit operational priority: “Recruiting for new interviewers – Targeting Iran guys”
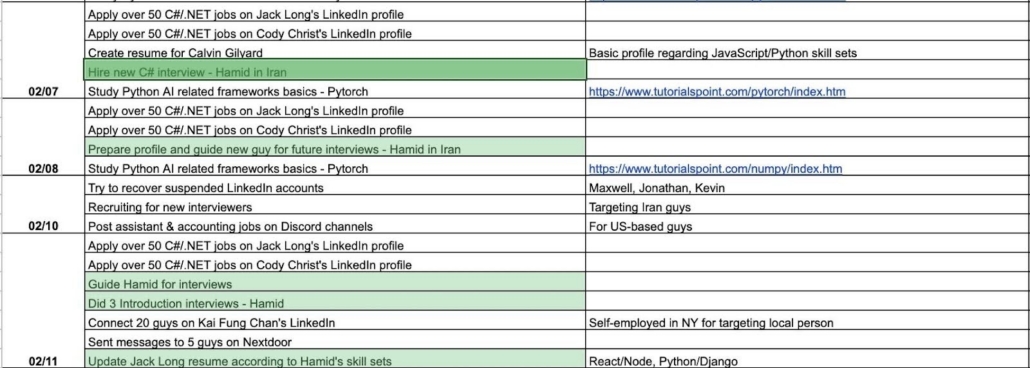
A screenshot of an internal North Korean regime spreadsheet shows the operator Sea explicitly stating they hired Iranians
“Operator Eugene:” Sea’s Accomplice
Sea isn’t operating in isolation. Documents show that a second facilitator codenamed “Eugene,” independently reports on January 10:
“Hiring new guys in Iran, Syria and SA.”
And again on January 11:
“Hiring new guys in Iran, Syria and SA. Found one US guy for keeping laptop.”
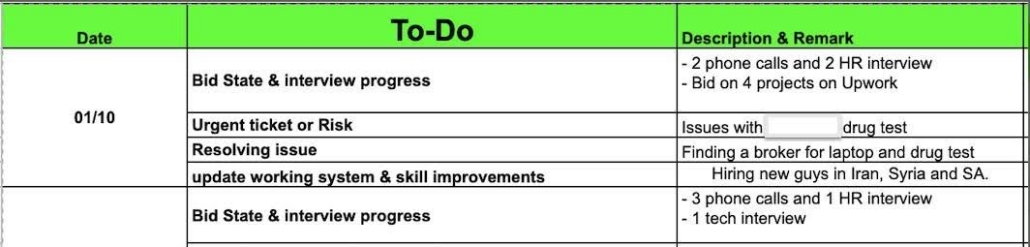
Screenshot mentioning hiring new workers in Iran, Syria, and SA
The DPRK appears to be systematically recruiting from countries where skilled developers exist but face limited direct access to Western job markets.
“Operator Fineboy:” The LinkedIn Funnel
A third facilitator, “Fineboy,” takes a higher-volume approach. Rather than hiring specific individuals, Fineboy runs a LinkedIn recruitment funnel targeting Iranian engineers at scale.
On January 16:
“Connected with 10 Iranian Data engineers using 2 LinkedIn profiles” On January 18:
“Chatted with 5 Iranian data engineers using a profile, no progress”
On January 22:
“Connected with 20+ Iran Data, .NET engineers using 3 LinkedIn profiles”
On January 25:
“Connected with 50+ Iranian devs, chatting with 3 devs”
Across the data set and weekly facilitator reports, Flare has identified at least 14 named Iranian recruits at various pipeline stages, including Hasan, Hamid, Mahdi, Peyman, Mehrdad, Naderi, Amir, Ali, Ali Assar, and Ahmadreza Zenouzi, among others. An additional seven Iranian developers were scouted by name on LinkedIn in a single session, and Fineboy’s outreach alone contacted over 50 Iranian developers in a single week, suggesting the total pool of Iranians engaged across all facilitators is substantially larger than what is visible in individual reports.
At least four separate DPRK cells were involved in Iranian recruitment simultaneously: Sea, Eugene, and Fineboy from the weekly reports, and individuals operating under code names Michael/Lander from a different operation.
The Iranians’ Role
To be clear about what role these recruits play: they are not applying for jobs or managing fake identities, the DPRK facilitators handle that. What the Iranian recruits do is show up on calls.
When a company schedules a phone screen with “Jack Long,” it’s Hasan who answers.
When there’s a technical interview, the Iranian developer is the one solving the coding problem. When a hiring manager wants to discuss experience with C# or React, the Iranian recruit is the voice on the other end of the line.
The facilitators explicitly track this division of labor. Sea’s reports distinguish between “Apply
over 100 C#/.NET jobs on Jack Long’s LinkedIn profile” (the facilitator’s job) and “Guide Hamid for interviews” or “Did 3 Introduction interviews – Hamid” (the recruit’s job). The facilitator gets the interviews; the recruit performs in them.
This is also why English fluency is treated as a critical hiring criterion throughout the reports. Multiple facilitators note rejecting candidates specifically because their English wasn’t good enough. One entry from a different facilitator reads: “reviewed the candidate’s video and declined their candidacy because of their English communication skills.” The Iranian recruits need to be convincing enough on a video call to pass as the Western persona they’re impersonating.
From the Other Side: How the DPRK Pitches Iranians
The weekly reports show this operation from the management side: facilitators logging tasks, tracking hires, and filing status updates. However, evidence from the other end of the conversation, the recruitment pitch itself, was recovered from a separate, confirmed DPRK-controlled machine.
The machine is tied to the internal North Korean site at 192.168.109.2, a known DPRK back-office platform documented in Flare and IBM X-Force’s joint research. It contains 169 Chrome profiles with all translations directed to Korean. The operator uses the alias “Michael,” runs a front company called and works alongside a co-facilitator called “Lander.”
Within browser data, we recovered the full recruitment lifecycle: LinkedIn scouting of Iranian developers, translated recruitment pitches, onboarding instructions, offer letters, and the responses from recruits themselves.
The Pitch
The pitch is standardized. After initial contact on LinkedIn, the operator delivers the key line:
“You’re from a country that is under sanctions. If you’re still interested in the role, I need to confirm whether you’re comfortable working under someone else’s identity.”
For those who express interest, the operator layers on incentives. They tell recruits that Iranians who’ve joined the program have transformed their lives: “Many Persians I’ve worked with have improved and started higher level of their lives, buying new homes and cars.” He promises crypto payment to circumvent Iran’s banking embargo and dangles the possibility of US migration: “we’ll definitely invite you to US once things go well.” In one message, connections to universities in Florida and Minnesota for visa sponsorship was offered.
To entice recruits further, one operator even claimed to have personally migrated to the US in 2016 – He didn’t – this operator was working from a machine on a North Korean internal network. The same identity fraud he asks his recruits to commit against American employers, he commits against his recruits.
The Scouting
Scouting appears to be deliberate. In a single LinkedIn session from May 2024, the operator researched at least seven Iranian developers by name, alongside Syrian and Lebanese candidates. Google search history from the same user shows the strategic logic explicitly:
“what are better english speaker between iran and lebanon” “syria is in sanctions?” “syrian job sites” “discord channels for syrian dev.”
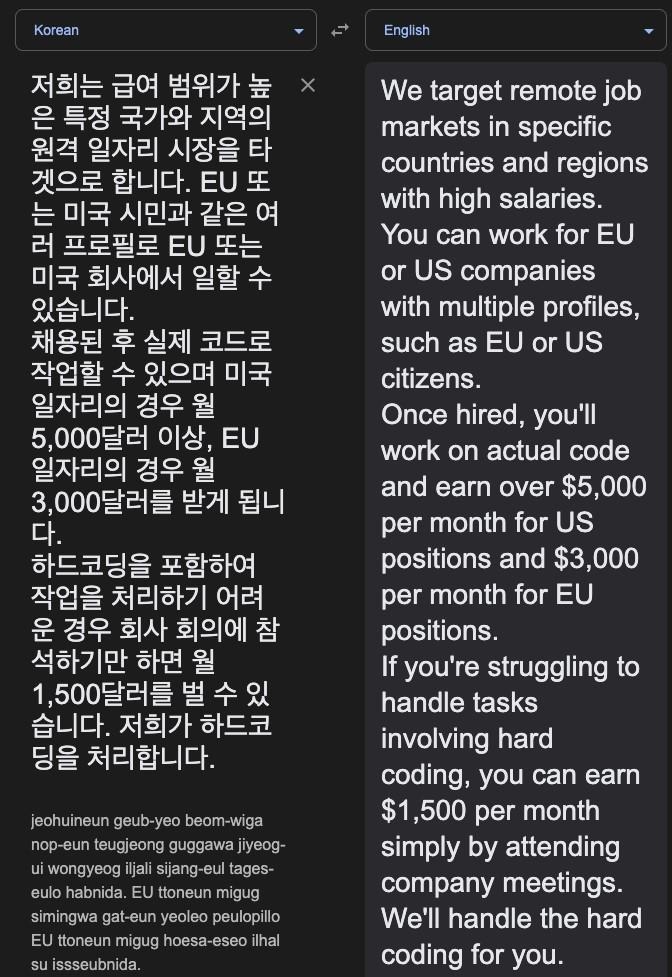
Google translate screenshot of a recruiting message
The Compensation
A formal offer letter recovered from the machine lays out the compensation. Addressed to [REDACTED] with a start date of August 26, 2024, it offers $500 per month as a part-time “Interview Associate” during the initial phase, rising to $2,700 per month after placement. The letter includes a one-month probation period, 15 days of annual leave, and an exclusivity clause. It reads like a legitimate employment contract for what is functionally a fraud recruitment document. But $2,700 is the starting tier. A Korean-language recruitment pitch reveals the full menu: $5,000 or more per month for US placements, $3,000 for EU. And for those who can’t handle the technical work: “you can simply attend the company meeting and you can earn $1,500/month. We will handle hard coding.”
The Recruits’ Responses
One developer told the operator directly: “I am totally agree with you that due to sanctions it would be a bit difficult. But I believe I have no problem to work under someone else identity.”
This recruit was onboarded to work US Eastern hours, starting at 4:30pm Iran time, paid in cryptocurrency.
Another recruit, Amir, accepted but questioned the pay, noting that $2,700 per month was below European entry-level salaries. Michael’s private reaction, visible in his own notes: “dare complaining salary huh” and a flat emoji.
Iranian military service is a recurring disruption across the pipeline. Multiple recruits cite it as a blocking factor, in which the North Korean recruiter has adapted, now screening for it upfront:
“Do you have any upcoming commitments, like military service in Iran, that could interrupt our contract?”
How Security Teams Can Respond
The evidence we have uncovered reveals an operation that is broader, more systematic, and more internationally networked than previous public reporting has suggested. The DPRK is not simply deploying its own nationals under false identities. It is building a multinational recruitment pipeline, drawing skilled developers from Iran, Syria, Lebanon, and Saudi Arabia into an infrastructure designed to infiltrate US defense contractors, cryptocurrency exchanges, financial institutions, and enterprises of every size. The recruits are real software engineers, paid in cryptocurrency, coached through interviews, and slotted into fabricated Western personas.
For organizations, the implication is clear: the person on the other end of a technical interview may not be who their resume says they are, and they may not be operating from where they claim. Strengthening employment verification is no longer optional. It is a direct countermeasure against a state-sponsored program that is actively scaling.
Equip Security Professionals and HR Teams to Stop Fraud
Flare provides ongoing monitoring for North Korean IT worker indicators of compromise, including email IOCs for HR teams screening candidates and URL and installed software IOCs for security teams validating current employees.