By Christopher Budd, Cybersecurity Evangelist
The February 2026 Microsoft Patch Tuesday is significantly smaller than January’s.
It can also be thought of as “security feature bypass month,” as security feature bypass vulnerabilities comprise the most significant issues in this release.
In the monthly total CVE tracking chart below, you can see that February is actually the lightest month in terms of total CVE since December 2024 in our tracking.
Total CVEs By Month
(Source: Microsoft Security Response Center)
In my December 2025 Patch Tuesday posting, I noted that December 2025 tied with February 2025 at 56 CVEs as the lightest month of 2025. February 2026 comes in at 55, just one fewer.
This makes February 2026 the lightest Patch Tuesday release since the noteworthy December 2023 one that featured only 33 CVEs.
But don’t let the lighter number of vulnerabilities fool you into thinking this release isn’t noteworthy.
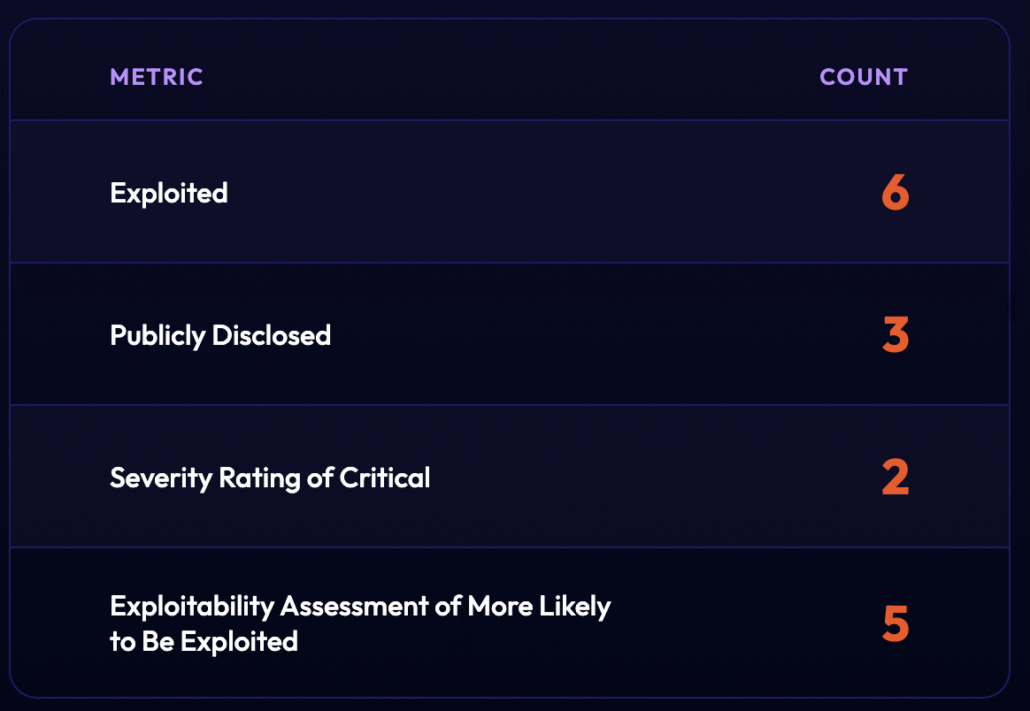
As the chart shows below, six vulnerabilities were listed by Microsoft as Exploitation Detected at release time:
- CVE-2026-21510 – Windows Shell Security Feature Bypass Vulnerability
- CVE-2026-21513 – MSHTML Framework Security Feature Bypass Vulnerability
- CVE-2026-21514 – Microsoft Word Security Feature Bypass Vulnerability
- CVE-2026-21519 – Desktop Window Manager Elevation of Privilege Vulnerability
- CVE-2026-21525 – Windows Remote Access Connection Manager Denial of Service Vulnerability
- CVE-2026-21533 – Windows Remote Desktop Services Elevation of Privilege Vulnerability
Exploited and Publicly Disclosed CVEs
(Source: Microsoft Security Response Center)
Almost immediately after Patch Tuesday, CISA added all six exploited vulnerabilities to the Known Exploited Vulnerabilities (KEV) catalog.
Three of these vulnerabilities are also listed as Publicly Disclosed:
- CVE-2026-21510 (Windows Shell Security Feature Bypass)
- CVE-2026-21513 (MSHTML Framework Security Feature Bypass)
- CVE-2026-21514 (Microsoft Word Security Feature Bypass)
Notably, all three are security feature bypass vulnerabilities, reinforcing this month’s theme and echoing the January out-of-band release.
The vulnerabilities listed as Exploitation Detected but Not Publicly Disclosed are:
- CVE-2026-21519 (Desktop Window Manager Elevation of Privilege Vulnerability)
- CVE-2026-21525 (Windows Remote Access Connection Manager Denial of Service Vulnerability)
- CVE-2026-21533 (Windows Remote Desktop Services Elevation of Privilege Vulnerability)
Since the January 2026 Patch Tuesday release, Microsoft also released CVE-2026-21509 (Microsoft Office Security Feature Bypass Vulnerability) out-of-band due to known active exploitation at the time. As I discussed in our January posting, this vulnerability appeared to be used in what I would call “limited and targeted attacks” when I was in the MSRC. That analysis appears to be accurate with no evidence of widespread attacks or much dark web interest in the exploits for that as of this writing, I discuss this further below.
This month only has two vulnerabilities rated Critical, interestingly neither is exploited. Of further interest, one of the exploited vulnerabilities is rated as Moderate, which is unusual. The remaining five exploited vulnerabilities are rated as Important.
Important rated vulnerabilities make up nearly all of this month’s release: only three vulnerabilities, already mentioned, are not rated as Important.
Five of the vulnerabilities are rated as Exploitation More Likely and these are all rated as Important.
Below, I examine the February 2026 Patch Tuesday to highlight information of greatest importance for threat hunters and defenders focused on vulnerability management and attack prevention.
I examine the vulnerabilities that I have defined as “notable” using the criteria below in “Methodology.”
Vulnerability Intelligence
Track Exploited CVEs Before Threat Actors Weaponize Them
Flare continuously monitors dark web forums, Telegram channels, and cybercrime communities for early signals of CVE weaponization, giving your team actionable intelligence on which vulnerabilities threat actors are actively discussing, trading, and exploiting.
✔ Real-time dark web exploit chatter monitoring
✔ 50,000+ cybercrime Telegram channels tracked
Methodology
I have developed these criteria based on my experience building and leading Patch Tuesday for Microsoft and other companies in the industry. The criteria identify vulnerabilities more likely to be used in attacks against unpatched systems and thus of greatest interest and concern for defenders.
I prioritize in decreasing order based on information Microsoft provided at the time of release, February 10, 2026:
- Those known by Microsoft to be exploited
- Those known by Microsoft to be publicly disclosed
- Those with a “Severity Rating” of “Critical”
- Those with an “Exploitability Assessment” of “More Likely”
For each vulnerability meeting these criteria, I provide some information on the technology and the threat environment around that vulnerability as of this writing.
Vulnerabilities that are not “notable” are not covered. This is to help defenders focus on the most impactful threats in this month’s release. However, remember that as the threat environment evolves, things that on paper appear as not “notable” at time of release can later be under attack. Best practices recommend deploying all updates, ultimately. When and how you do so is a matter for your analysis and assessment.
Microsoft labels these as “Exploitation Detected.” For readability, I refer to them as “exploited” except when quoting Microsoft terminology.
The information in this posting is intended to help you understand and better prioritize vulnerabilities for remediation in your environment.
In Appendix A, you will find the complete listing of this month’s Microsoft bulletins with hyperlinks to information about the individual vulnerabilities on the MSRC website.
All information is based on the MSRC’s publicly available database, open source intelligence research, and the Flare platform. I include links for validation, reference and your further research.
Top Level Findings
Numbers of CVEs: Total, Max Severity Critical/Important and Notable
Threat Environment and Exploit Information
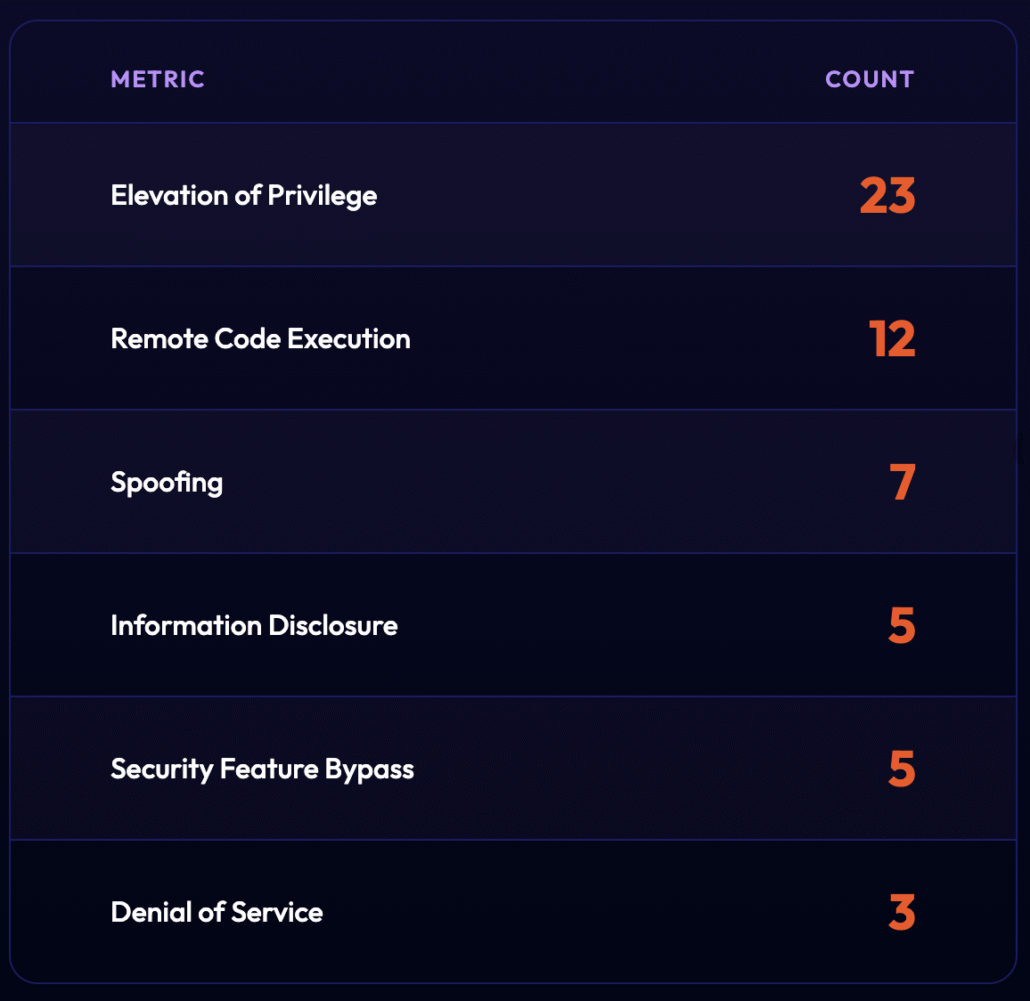
Vulnerability Impacts
Notable CVEs
Exploitation Detected – Publicly Disclosed
These three vulnerabilities are all security feature bypass vulnerabilities rated as Important, Exploitation Detected, and Publicly Disclosed.
CVE-2026-21513 – MSHTML Framework Security Feature Bypass Vulnerability
This particular security feature bypass exists in the notorious MSHTML component, the HTML renderer in Windows.
The Microsoft writeup notes that this vulnerability can allow “the attacker to bypass security features and potentially achieve code execution.” This is not simply the suppression of a security feature dialog but has the potential for code execution as well. In light of that, it’s unclear why this isn’t listed as code execution vulnerability, but that is a very important nuance in understanding the vulnerability and the risks it presents.
The attack vector is a classic vector for MSHTML vulnerabilities. The attacker crafts a malicious HTML file or shortcut (.lnk) file which is then delivered through a link, email attachment, or download. This is a classic vector for phishing attacks.
Beyond the vulnerability’s presence in a well-known and frequently exploited component, the threat environment around this particular vulnerability is notable because of additional information that has come to light since the release.
On February 20, 2026, Akamai released research showing that they had been able to locate an instance of attacks against this vulnerability in a sample uploaded to VirusTotal on January 30, 2026, before the patch was released. That sample indicated malicious .lnk files being used in the attack. Akamai’s information confirms Microsoft’s claim at release that this vulnerability was being exploited at the time of release.
Akamai attributes the activity to APT28 and links to the CERT-UA advisory from January discussing CVE-2026-21509, the January out-of-band release. Akamai doesn’t draw any further connections between these two vulnerabilities, but it is notable that both of these are tied to APT28 in the January timeframe. It’s a reasonable supposition that both vulnerabilities are being used together in their attacks.
However, I noted in January that CVE-2026-21509 appeared to be “limited and targeted” and we will discuss it again later. The limited and targeted label appears to apply to this vulnerability as well, at least at the time of this writing.
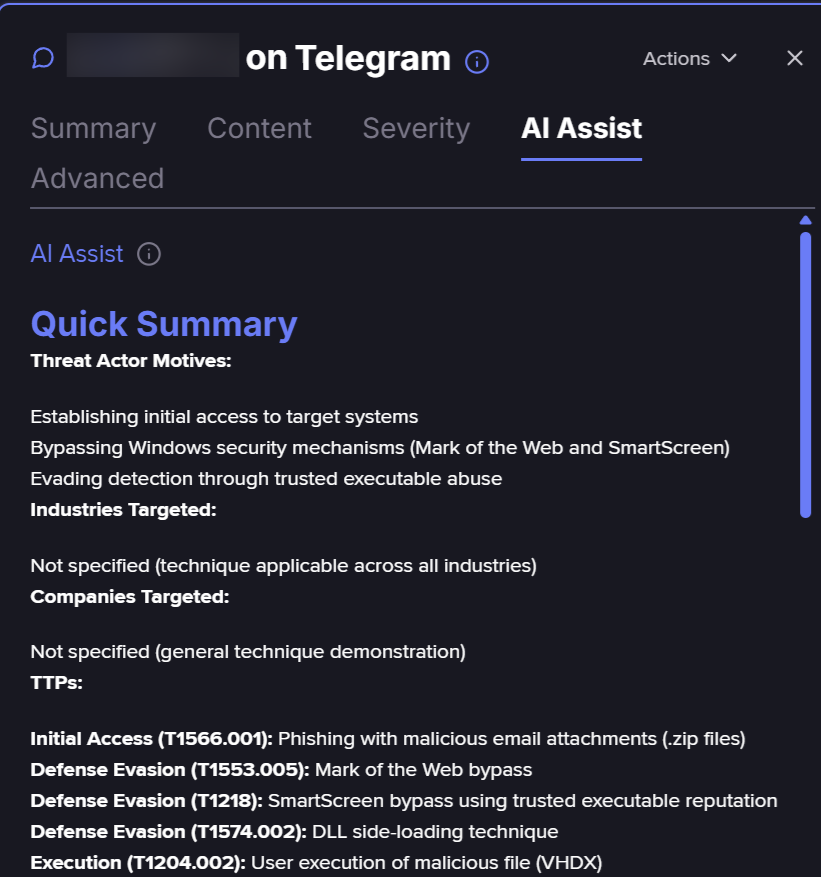
Through Flare, we can see not only that no exploit for this vulnerability is circulating, but also that individuals are actively asking whether anyone has found one, as shown below.
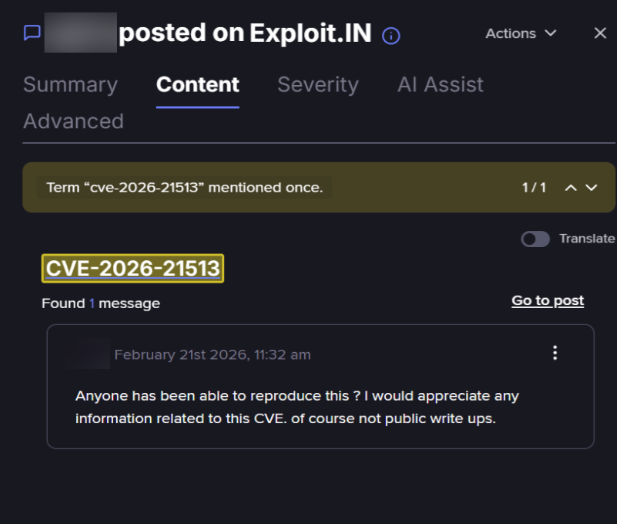
Flare search on CVE-2026-21513 (Flare link, sign up for the free trial to access if you aren’t already a customer)
Flare’s conversation tracking confirms that this request received no responses, further supporting the “limited and targeted” characterization for now.
As with CVE-2026-21509, even though this is limited and targeted, the threat actors known to be using this vulnerability and its active usage means that it’s something that many organizations will want to treat with the highest priority.
CVE-2026-21510 – Windows Shell Security Feature Bypass Vulnerability
In their writeup, Microsoft notes that this vulnerability can enable you to “bypass Windows SmartScreen and Windows Shell security prompts by exploiting improper handling in Windows Shell components, allowing attacker‑controlled content to execute without user warning or consent.”
SmartScreen is a feature in Microsoft Defender that “protects against phishing or malware websites and applications, and the downloading of potentially malicious files.”
As a security feature bypass, this vulnerability can enable an attacker to suppress and bypass the warnings that SmartScreen and the Windows shell would normally raise.
The specific vector for this vulnerability, as Microsoft notes, is to entice a user to “open a malicious link or shortcut file.” Once that happens, the malicious code that is behind the link or shortcut would execute without the expected security warnings being raised to warn and protect the user. This is a classic malicious link or shortcut vector that can be attractive to attackers for phishing campaigns.
While Microsoft calls this out as being exploited, there hasn’t been much discussion on this specific vulnerability since the release, either on the clear or dark web. A search on Flare shows some basic reposting on this on channels at time of release and a couple of mentions since. However, a search in Flare for SmartScreen bypasses does show that threat actors are actively looking for SmartScreen and Mark of the Web (MoW) bypasses as shown below.
Flare search on SmartScreen Bypasses (Flare link, sign up for the free trial to access if you aren’t already a customer)
So while Microsoft shows Exploitation Detected and Publicly Disclosed for this vulnerability, there’s not a lot of activity around it broadly. But there is threat actor interest in SmartScreen bypasses generally. This is a vulnerability that could easily get folded into threat actor research and used more broadly in the coming days and weeks as threat actors look at it and possibly more information comes out.
CVE-2026-21514 – Microsoft Word Security Feature Bypass Vulnerability
While the other two security feature bypass vulnerabilities affect Microsoft Windows, this one affects Microsoft Word, making it a vulnerability that is attacked by using malformed Word documents that suppress the usual security warnings when opening Word documents.
This makes this an attractive vulnerability for the kinds of spear phishing attacks that we’ve seen Office vulnerabilities used for in the past.
On February 18, 2026, CVEReports provided a very good, detailed deep-dive of the mechanics of the vulnerability. Their analysis calls out this vulnerability as an example of the “technical debt” that older code and technologies represent. In this particular case the vulnerability occurs, they report, in Object Linking and Embedding (OLE) a technology Microsoft first introduced in 1990.
Even though this is listed as Exploitation Detected and Publicly Disclosed there is no public indication of exploits for this vulnerability at this time. This would appear to be another that falls into the “limited and targeted” category at this time.
Exploitation Detected – Not Publicly Disclosed
CVE-2026-21533 – Windows Remote Desktop Services Elevation of Privilege Vulnerability
The Sophos Active Adversary Report from April 2024 calls out that RDP abuse was behind 90% of the attacks their IR teams handled.
In light of that, any vulnerability affecting RDP should be cause for concern, especially one that is listed as exploited at time of release. And one that can be used to elevate privileges once on the system using RDP is cause for greater concern.
This vulnerability was reported to Microsoft by CrowdStrike, which has provided some information on the attacks that they’ve seen in their blog. The most important points are that they’ve seen that “threat actors had used this binary in the wild to target U.S. and Canada-based entities since at least December 24, 2025.”
They go on to say they believe that the release of the patch “will almost certainly encourage threat actors possessing CVE-2026-21533 exploit binaries, as well as any exploit brokers possessing the underlying exploit, to use or monetize the exploits in the near term.” That’s a reasonable assessment.
However, beyond CrowdStrike’s reporting, there is little additional public reporting or observable threat actor discussion around this vulnerability, including within Flare telemetry.
This is one where the prudent assessment will likely be to weigh the risks around the vulnerability and what’s been reported over what’s being seen or not seen.
CVE-2026-21519 – Desktop Window Manager Elevation of Privilege Vulnerability
This is another vulnerability affecting the Desktop Window Manager in Windows. This component was front and center in last month’s release with CVE-2026-20805 – Desktop Window Manager Information Disclosure Vulnerability being listed as Exploitation Detected at time of release.
This vulnerability is nearly identical in terms of being known to be exploited at the time of release and affecting this particular component.
Desktop Window Manager has been a problem area for several months now. A review of MSRC data shows that this component has been patched 17 times from January 2025 through the February 2026 release and exploited at time of release three times.
| Month | CVE | Exploited | Exploitability |
|---|---|---|---|
| January 2025 | CVE-2025-21304 | No | Less Likely |
| April 2025 | CVE-2025-24062 | No | Less Likely |
| April 2025 | CVE-2025-24060 | No | Less Likely |
| April 2025 | CVE-2025-24058 | No | Less Likely |
| April 2025 | CVE-2025-24073 | No | Less Likely |
| April 2025 | CVE-2025-24074 | No | Less Likely |
| May 2025 | CVE-2025-30400 | Yes | Exploited |
| June 2025 | CVE-2025-33052 | No | Unlikely |
| September 2025 | CVE-2025-53801 | No | Less Likely |
| October 2025 | CVE-2025-58722 | No | More Likely |
| October 2025 | CVE-2025-59255 | No | Unlikely |
| October 2025 | CVE-2025-59254 | No | Unlikely |
| December 2025 | CVE-2025-64680 | No | Less Likely |
| December 2025 | CVE-2025-64679 | No | Less Likely |
| January 2026 | CVE-2026-20805 | Yes | Exploited |
| January 2026 | CVE-2026-20842 | No | Less Likely |
| February 2026 | CVE-2026-21519 | Yes | Exploited |
While last month, we reported on multiple instances of discussion around CVE-2026-20805, this month’s patch is not garnering as much interest. There’s little active discussion on this vulnerability on the open web or the dark web.
However, given the sheer number of vulnerabilities plus two months in a row this component has been exploited at time of release, keeping patches current for this component is the right call. Being aware of additional vulnerabilities affecting this component in coming months is another right call.
CVE-2026-21525 – Windows Remote Access Connection Manager Denial of Service Vulnerability
This is a denial of service vulnerability affecting the Remote Access Connection manager, a Windows feature that literally dates back to the days of dial-up internet connections but is still used today for some VPN connectivity.
A successful attack would have to be carried out locally and would result in denying the ability to use Remote Access Connection Manager which would impact the ability to use VPNs that rely on it.
Microsoft reports Exploitation Detected at time of release. This vulnerability was reported by 0patch vulnerability research team at ACROS Security and they provide basic information on their site, but only as an addendum to another vulnerability report.
Beyond Microsoft’s Exploitation Detected designation and 0patch’s brief note, there are no public details, meaning we can’t currently assess the exploit chain, reliability, or targeting.
A look on the clear and dark web also turns up no information on this vulnerability.
If you use a VPN that relies on Windows Remote Access Connection Manager, this is something you’ll want to address. Otherwise, you can factor these points into your threat and risk assessment and prioritize accordingly.
January 2026 Out-of-Band
CVE-2026-21509 – Microsoft Office Security Feature Bypass Vulnerability
In our January post I noted that CVE-2026-21509 was released out-of-band, an indicator by Microsoft that something is under active attack and represents a threat.
You can see more information on this vulnerability in that writeup. Here, I want to take a moment and give an update on the current threat environment around this vulnerability since that writeup.
In short, there’s been little change from the “targeted and limited” attacks threat environment around this vulnerability.
The most important comes from a report from ZScaler that goes into detail on an observed campaign utilizing this vulnerability. And a report from Logpoint goes into detail on the mechanics of the vulnerability and how it arises due to a tactic to bypass the Killbit, a security feature by Microsoft to protect against vulnerable ActiveX controls.
While those provide more information on the vulnerability and the attacks that have been observed, though, there’s little change in the threat environment around this vulnerability otherwise.
In the Flare search below, we can see that the chatter around this vulnerability has essentially ceased (and never went very high).
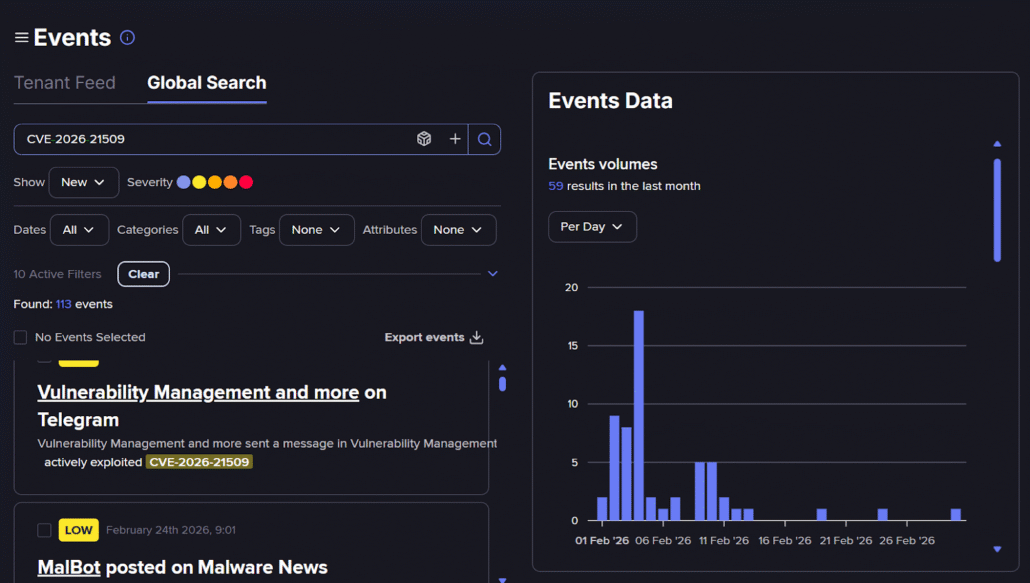
Flare search on CVE-2026-21509 (Flare link, sign up for the free trial to access if you aren’t already a customer)
As noted above, Akamai has noted APT28 activity around CVE-2026-21513 – MSHTML Framework Security Feature Bypass Vulnerability and they are believed to be behind attacks against this vulnerability. But the level of activity around this vulnerability since it was released has, so far, confirmed the assessment I made last month that this is not a widespread threat. It remains a real and active one, especially for organizations that reckon APT28 as an active threat and that should reflect in your assessment of this vulnerability.
Criticals
CVE-2026-21522 – Microsoft ACI Confidential Containers Elevation of Privilege Vulnerability
CVE-2026-23655 – Microsoft ACI Confidential Containers Information Disclosure Vulnerability
This month’s critical vulnerabilities are notable for almost being critical in name only. Both of them affect the same component, Microsoft ACI Confidential Containers. Both are rated as Exploitation Less Likely. And neither are code execution vulnerabilities: one is an elevation of privilege (EoP) and the other information disclosure.
The technology being patched is Microsoft Azure Confidential Instances (ACI) which provides more secure container workloads. These ACIs run in a hardware-backed Trusted Execution Environment (TEE) to provide capabilities like data integrity, data confidentiality, and code integrity.
The vulnerabilities in question can enable an attacker to compromise that core capability of ACI.
The EoP vulnerability can enable an attacker to elevate privileges within the container to run code “within the affected ACI container’s context, allowing them to run code with the same privileges as the compromised container.”
The information disclosure vulnerability is a result of cleartext storage of sensitive information in Azure Compute Gallery and so can lead to the disclosure of secret tokens and keys.
A search in Flare shows practically no traffic or discussion of either vulnerability, and there has been no indication of disclosure or exploits for either of these, which matches Microsoft’s prediction that Exploitation is Less Likely.
That said, these are rated as Critical for a reason, and if you’re using ACI containers, the nature of these vulnerabilities strikes at some of the key reasons you’re using them. So while the exploit environment may not be threatening, these are important issues to address for auditing and cybersecurity hygiene.
Exploitability More Likely
CVE-2026-21253-Mailslot File System Elevation of Privilege Vulnerability
This is an elevation of privilege vulnerability that can give attackers SYSTEM level control. The specific vector for it is a malicious local executable file even though the component in question is an interprocess communications (IPC) component. Mailslots date back to the earliest days of Microsoft Windows networking and provide for one-way message broadcasting across a network.
As of writing this, there is no indication of attacks, exploit code or much interest in this vulnerability in the dark web.
CVE-2026-21241-Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
CVE-2026-21238-Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
These are two elevation of privilege vulnerabilities affecting Winsock, a networking component within Microsoft Windows.
Both can be used to achieve SYSTEM level privileges on a system and require local access and the ability to run code on the vulnerable system to achieve that.
Microsoft calls out CVE-2026-21241 in particular as having a level of complexity that would seem to make it harder to exploit. This makes it unclear why it’s listed as More Likely to be Exploited. The specific complication is that Microsoft notes the attacker “would need to have knowledge of a specific operation that triggers a memory allocation failure, specifically a use after free.” This would appear to make this particular vulnerability useful only for very specific targeting. And that is consistent with EoP vulnerabilities like these: they tend to be used as part of an attack chain.
Neither of these show much activity around exploits or discussion on the open web or the dark web.
CVE-2026-21231-Windows Kernel Elevation of Privilege Vulnerability
This is a race condition elevation of privilege vulnerability in the Windows Kernel. Windows Kernel has three vulnerabilities this month, only one of which is notable.
But Windows Kernel elevation of privilege vulnerabilities have been addressed 21 times since December 2024.
Fortunately only once has it been exploited at time of release in November 2025. But the frequency with which this has been patched in the past 12 months in particular (every month except for June and July) marks this as another problematic area.
CVE-2026-21511-Microsoft Outlook Spoofing Vulnerability
This month has been light on notable Office vulnerabilities, this and CVE-2026-21514 – Microsoft Word Security Feature Bypass Vulnerability being the only ones. There are four other vulnerabilities affecting Office, two information disclosure, an elevation of privilege, and another spoofing vulnerability. But those fall below the “notable” bar because they’re Unlikely or Less Likely to be Exploited.
This vulnerability is a fairly standard Outlook client spoofing vulnerability. Microsoft hasn’t provided much detail on it beyond an attacker being able to “perform spoofing over a network.”
CVE Trends Analyses
Starting this month, I’m including charts to show trends around each release for the past fifteen months, starting with December 2024 as a starting point.
In the chart below, you can see the notable vulnerabilities as a percentage of the vulnerabilities addressed each month.
Notable CVEs are in purple in the chart with the non-notable CVEs stacked on top in orange to give the total number of CVEs for that month. Across is a green line to mark the percentage of each month’s CVEs that were notable as a percentage.
Total CVEs by Month: Notable and Non-Notable
2024
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2026
2026
(Source: Microsoft Security Response Center)
This chart shows that even though this is a lighter release in terms of sheer volume, it is more densely notable than those numbers would lead you to believe. This reinforces the points we made at the beginning about the nature of this month’s release. 24% of the CVEs for this month were notable.
It’s also worth noting that there’s no correlation between the volume of CVEs and the percentage of those that are notable. The October 2025 release was one of the largest ever but had one of the lower percentages of notable CVEs with only 14% of the CVEs being notable. By contrast, the March 2025 release, which was as light as the February 2026 release but had the highest density of notable CVEs in the past fifteen months at 38%.
Looking at trends around the notable CVEs by their type (exploited, publicly disclosed, critical, more likely to be exploited) shows us the breakdown of what makes the notable CVEs specifically notable.
Notable CVEs by Type
2024
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2026
2026
(Source: Microsoft Security Response Center)
This chart shows that this month is unusual in particular for the low number of criticals (only two this month) relative to other months. We can also see how this month is heavier in exploited vulnerabilities, is relatively lighter in terms of those more likely to be exploited and lacks any that are only publicly disclosed. All of those factors make this month’s notable CVEs unusual compared to most months.
Below, I’ve charted the number of CVEs by impact, helping us better understand the trends around the types of vulnerabilities being addressed each month.
CVEs by Impact
2024
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2025
2026
2026
(Source: Microsoft Security Response Center)
One standout pattern in this chart is that elevation of privilege (EoP) vulnerabilities have been the predominant vulnerabilities by impact for ten of the past 15 months with code execution accounting as the top vulnerability by impact for the remaining five of the fifteen months. A subtle shift started in April when EoP vulnerabilities first surpassed code execution vulnerabilities. That shift became decisive in July 2025 and continues through this month’s release.
Forecasting for the March 2026 Release
With 14 months of release trend data, historical patterns suggest the March 2026 release is likely to be:
- Heavier in total CVE volume: This month has been unusually light in terms of volume and we can see a regular pattern where a light month is followed by a heavier month.
- Lighter in exploited CVEs at release time: This is based on the fact that six exploited at time of release has only happened once before in the past fifteen months and every month after a peak like this has shown a drop.
- Slightly heavier in publicly disclosed vulnerabilities: This is because zero publicly disclosed but not exploited vulnerabilities that we see this month is an outlier. Usually we see at least a couple of these each month.
- Slightly lighter in overall percentage of notable CVEs: We see a pattern where heavier months have a lower percentage of notable CVEs. If the volume forecast above is realized, it stands to reason that the overall percentage of notable CVEs will drop slightly next month.
- Elevation of privilege likely remains the dominant vulnerability type: As noted above, elevation of privilege has been the dominant vulnerability type since July 2025.
- Additional Desktop Window Manager vulnerabilities, possibly exploited at time of release: As noted earlier, this component has been under active attack at time of release across two Patch Tuesday releases recently, been exploited at time of release three times across two Patch Tuesday releases, and patched 17 times since January 2025. It’s reasonable to expect some more activity around this component next month.
If these patterns hold, March may bring a higher operational workload with more CVEs to review and process but without a proportional increase in high-urgency exploited or publicly disclosed issues. Defenders can consider preparing for increased volume, but not necessarily elevated crisis response levels.
Multiple Vulnerability Clusters
Often it is helpful to see when similar vulnerabilities being addressed occur around specific products, technologies or features. The below table shows this month’s occurrences of multiple vulnerability clusters.
Appendix A: February 2026 Microsoft CVEs
Below is the complete list of CVEs released this month. This data is taken from the Microsoft Security Response Center (MSRC) Security Update Guide and contains all CVEs that were released on February 10, 2026. It does not contain any third-party or Chromium (Microsoft Edge) vulnerabilities.
The data below has been grouped and sorted as follows:
- All where Exploited = Yes
- All where Publicly Disclosed = Yes
- All where Severity = Critical
- All where Exploitation = More Likely, sorted by decreasing severity, sorted alphabetically by impact
- All where Exploitation = Less Likely, sorted by decreasing severity, sorted alphabetically by impact
- All where Exploitation = Unlikely, sorted by decreasing severity, sorted alphabetically by impact
- Any remaining items
This list shows each CVE only once and groups by the prioritization discussed above.
For example, a CVE that has Exploited = Yes and Publicly Disclosed will be listed only once, under “Exploited = Yes” since that is a higher priority for most defenders’ risk assessments.
Note this month there are three new CVEs where Exploited = Yes and Publicly Disclosed = Yes, three new CVEs where Exploited = Yes and Publicly Disclosed = No and the January out-of-band where Exploited = Yes and Publicly Disclosed = No.
Know When Threat Actors Are Hunting for Exploits
Flare monitors dark web forums, Telegram channels, and underground marketplaces in real time — so your team can see not only whether an exploit for a vulnerability is circulating, but also when threat actors are actively seeking one. Prioritize patching based on real threat actor intent, not just CVSS scores.





