By Tammy Harper, Senior Threat Intelligence Researcher
A new cryptomining malware known as KATREUS Miner has surfaced on the RAMP cybercrime forum, marketed as a “silent” Monero (XMR) miner with advanced stealth and persistence capabilities. Written from scratch in pure C and Assembly with a custom CRT, the builder produces payloads as small as 48.5 KB while maintaining full feature richness. The developer, operating under the handle “IsEmptyOrNull,” is selling only five licenses at $4,999 each, positioning KATREUS as a premium cryptojacking tool for experienced botnet operators.
What is KATREUS Miner?
KATREUS is a cryptojacking malware designed to silently mine Monero cryptocurrency on infected Windows systems. Unlike browser-based cryptojacking attacks that mine through JavaScript, KATREUS operates as a traditional botnet miner that persists on victim machines and mines continuously in the background.
The malware supports Windows 8.1 through Windows 11 and Windows Server 2012 R2 through 2025, covering the full spectrum of enterprise and consumer Windows environments. Its compact 48.5 KB payload size makes it easier to distribute and harder to detect compared to larger mining frameworks.
The developer is offering limited availability with only five licenses for sale, though they also mention willingness to collaborate on campaigns for a percentage split. This revenue-sharing model is common in the cryptojacking ecosystem, allowing operators without upfront capital to participate while the developer takes a cut of mining proceeds.
Understanding Monero Mining Economics
To evaluate the developer’s revenue claims, it helps to understand how Monero mining works. The Monero network operates like a continuous lottery running every two minutes. Every computer that mines is essentially buying “lottery tickets” in the form of hash guesses. The more guesses a miner can make per second (measured as hashrate), the higher the chance of winning a block reward.
Monero uses the RandomX algorithm, which is specifically designed to be CPU-friendly and resist ASIC mining. This makes it ideal for cryptojacking operations since infected consumer and enterprise computers can contribute meaningful hashrates using their standard processors.
The Developer’s Revenue Claims
In forum discussions, the developer “IsEmptyOrNull” makes specific claims about potential earnings from KATREUS deployments:
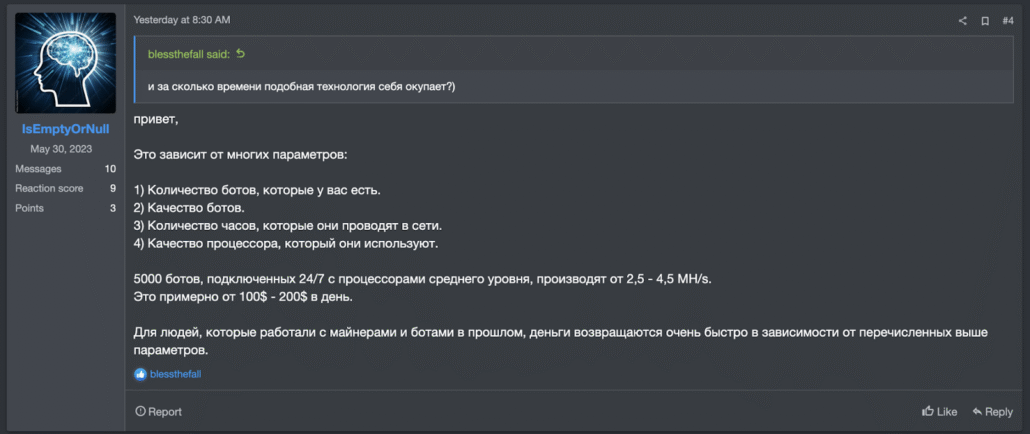
KATREUS developer claims 5,000 bots can generate $100-$200 per day mining Monero
According to the developer, 5,000 bots connected 24/7 with mid-range processors should produce between 2.5 and 4.5 MH/s (megahashes per second) of combined hashrate, translating to approximately $100 to $200 per day in mining revenue.
Verifying the Math: Do the Numbers Add Up?
To verify these claims, we can calculate expected returns using current Monero network parameters. The analysis uses the following assumptions based on November 2025 snapshots:
Network Parameters: Monero block time of approximately 120 seconds (720 blocks per day), tail emission block reward of approximately 0.6 XMR, and network hashrate ranging from 4.18 GH/s to 5.369 GH/s.
Price Snapshot: $347.31 per XMR (as used by mining calculators in November 2025).
Daily Revenue Scenarios
The daily XMR issuance across the entire network equals 720 blocks multiplied by 0.6 XMR, totaling 432 XMR per day. A miner’s expected daily earnings equal their share of total network hashrate multiplied by total daily issuance:
- Scenario A (Low Miner / Low Network): 2.5 MH/s miner against 4.18 GH/s network = ~$89.74/day
- Scenario B (High Miner / Low Network): 4.5 MH/s miner against 4.18 GH/s network = ~$161.52/day
- Scenario C (Low Miner / High Network): 2.5 MH/s miner against 5.369 GH/s network = ~$69.86/day
- Scenario D (High Miner / High Network): 4.5 MH/s miner against 5.369 GH/s network = ~$125.75/day
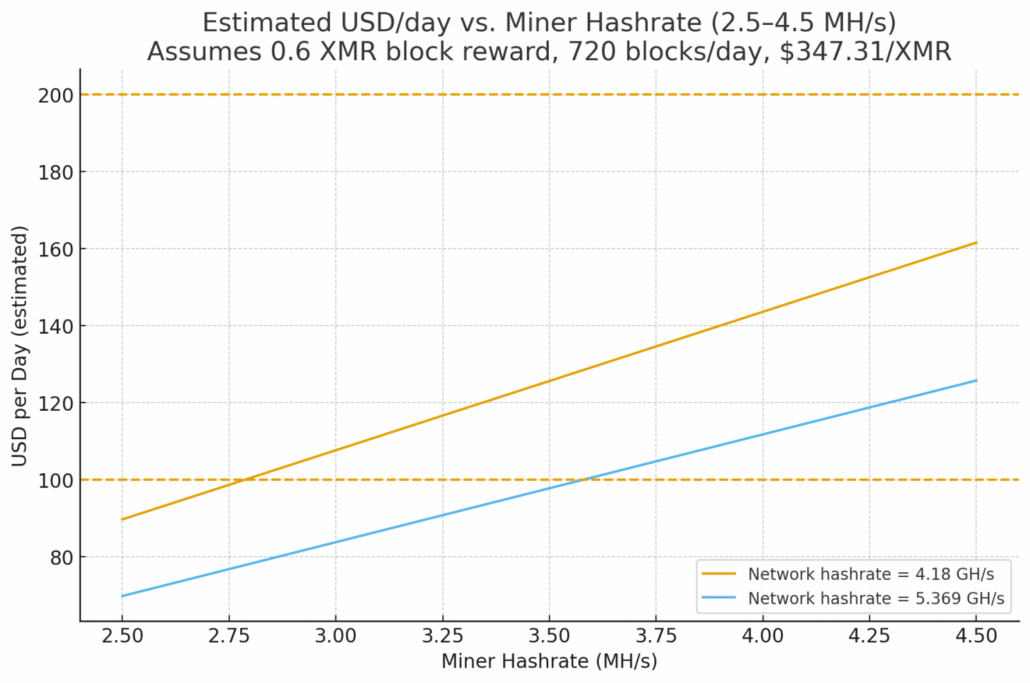
Estimated daily revenue ranges from ~$70 to ~$162 depending on hashrate and network conditions
The calculated range of $70 to $162 per day broadly validates the developer’s claimed $100 to $200 range, though actual results will vary with XMR price volatility and network hashrate fluctuations.
The Per-Bot Economics: Cents Per Machine
While $100-$200 per day sounds attractive, distributing this across 5,000 infected machines reveals the slim margins of cryptojacking operations:
- Scenario A: $89.74/day ÷ 5,000 bots = $0.0179 per bot per day (approximately 1.8 cents)
- Scenario B: $161.52/day ÷ 5,000 bots = $0.0323 per bot per day (approximately 3.2 cents)
- Scenario C: $69.86/day ÷ 5,000 bots = $0.0140 per bot per day (approximately 1.4 cents)
- Scenario D: $125.75/day ÷ 5,000 bots = $0.0252 per bot per day (approximately 2.5 cents)
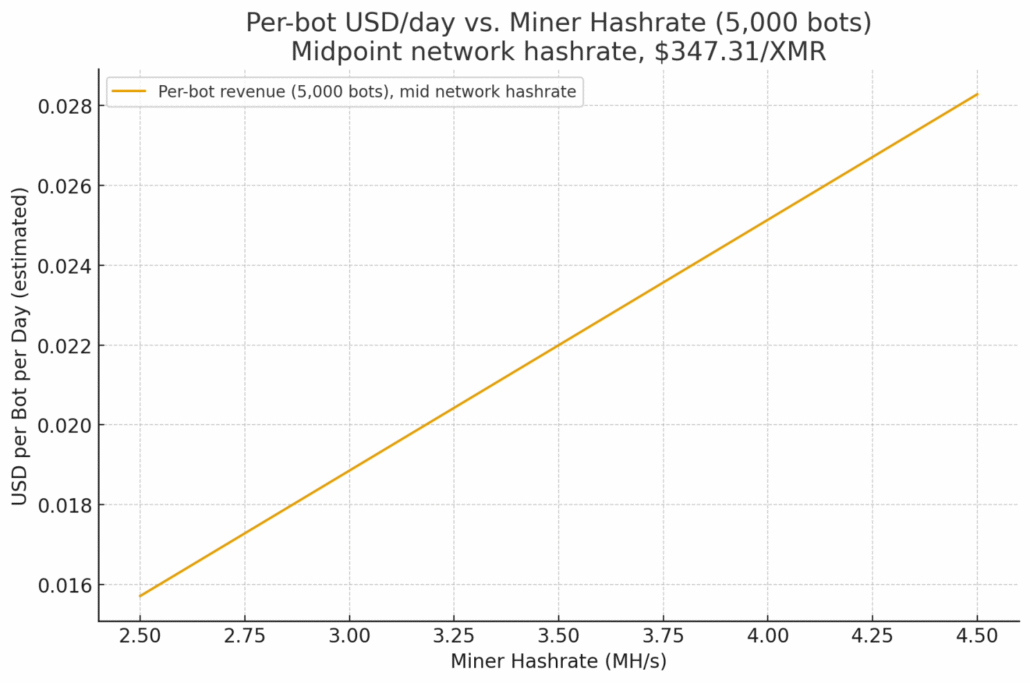
Each infected machine generates only 1.4 to 3.2 cents per day in mining revenue
This illustrates why cryptojacking operations require massive scale. Each infected host yields only a few cents per day, making profitability entirely dependent on botnet size and consistent uptime. The developer’s pitch that “money returns quickly” only applies to operators who already control thousands of compromised machines.
Stealth and Persistence Features
KATREUS includes several features designed to maintain long-term presence on infected systems while avoiding detection:
Anti-Kill and Watchdog Mechanisms
Anti-Kill: If the miner process is terminated, it automatically relaunches after a configurable delay set by the operator during build time.
Watchdog: When users open Task Manager or similar process monitoring tools (Daphne, Process Explorer, System Informer), the miner enters sleep mode and stops consuming CPU resources. This prevents victims from noticing unusual CPU usage during casual system inspection.
Persistence and Process Injection
Persistence: The miner installs automatically and survives system reboots, ensuring continuous mining operations without requiring reinfection.
Process Injection: KATREUS runs as a legitimate Windows process chosen by the operator, making it harder to identify as malicious through process listings.
Anti-Analysis and Evasion Techniques
The developer claims KATREUS bypasses all major security solutions at the time of writing and includes additional evasion features:
Anti-Debug: Detection of debugging environments to prevent analysis
CIS Country Check: Victims in Commonwealth of Independent States countries are excluded from mining, a common practice among Russian-speaking malware developers to avoid domestic law enforcement attention
FLOSS and CAPA Bypass: Techniques to evade automated malware analysis tools
Mutex Checks: Prevention of multiple instances running simultaneously
Cryptojacking Detection: Warning Signs
Organizations should monitor for the following indicators that may suggest cryptojacking activity:
CPU Usage Anomalies: Unexplained high CPU utilization, particularly during off-hours or when systems should be idle. Note that sophisticated miners like KATREUS suspend activity when monitoring tools are opened, so automated monitoring is more effective than manual checks.
Network Connections: Connections to known mining pools or unusual outbound traffic patterns. Common Monero mining pools use predictable ports and hostnames.
Power Consumption: Increased electricity costs and thermal output from systems running at sustained high CPU loads.
Process Behavior: Legitimate process names consuming unusual CPU resources, or processes that suspend when monitoring tools are opened.
Recommendations for Security Teams
Organizations can implement the following controls to prevent and detect cryptojacking attacks:
1. Endpoint Detection and Response (EDR): Deploy EDR solutions capable of detecting process injection, suspicious CPU patterns, and connections to mining pool infrastructure.
2. Network Monitoring: Block known mining pool domains and monitor for Stratum protocol traffic commonly used by cryptocurrency miners.
3. CPU Usage Baselines: Establish normal CPU utilization baselines and alert on sustained deviations, particularly during non-business hours.
4. Application Whitelisting: Implement application control policies to prevent unauthorized executables from running on endpoints.
5. Patch Management: Maintain current patches to reduce the attack surface for initial access vectors that distribute cryptomining malware.
Indicators of Compromise (IOCs)
The following indicators are associated with KATREUS Miner based on forum advertisements:
Developer Handle: IsEmptyOrNull (RAMP forum)
Target Cryptocurrency: Monero (XMR)
Payload Size: ~48.5 KB
Architecture: x64 only
Codebase: Pure C + Assembly with custom CRT
Target OS: Windows 8.1 through Windows 11, Windows Server 2012 R2 through 2025
CIS Exclusion: Malware does not execute in CIS (Commonwealth of Independent States) countries
What Security Teams Can Keep in Mind About KATREUS Miner
KATREUS Miner represents a feature-rich addition to the cryptojacking malware ecosystem. Its compact size, comprehensive evasion capabilities, and configurable persistence mechanisms make it well-suited for long-term, stealthy mining operations. The developer’s own sales pitch reveals the fundamental economics of cryptomining malware: even with 5,000 compromised hosts, daily profits only reach $100-$200.
This translates to mere cents per infected machine, meaning profitable cryptojacking operations require massive scale and continuous uptime. For organizations, this underscores the importance of both prevention and detection. A single infected endpoint may show minimal performance impact, but cryptojacking at scale represents significant electricity costs, hardware wear, and potential indicators of broader network compromise.
The $4,999 license fee and limited availability suggest KATREUS is targeting experienced botnet operators who already control or have access to large numbers of compromised machines. Organizations should ensure their monitoring and detection capabilities can identify the subtle indicators of modern cryptojacking malware that actively evades casual observation.
Monitor for External Threats with Flare
The Flare Threat Exposure Management solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors. Our platform automatically scans the clear & dark web and prominent threat actor communities 24/7 to discover unknown events, prioritize risks, and deliver actionable intelligence you can use instantly to improve security.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. See what external threats are exposed for your organization by signing up for our free trial.