
By Assaf Morag, Cybersecurity Researcher
Soccer fans worldwide are susceptible to the mobile malware pipeline, carefully crafted by threat actors: a scaled, multi-layered mobile-first infrastructure blending illegal betting, fake platforms, and malware delivery. Major sporting tournaments have consistently served as high-impact lures for fraud, phishing, and malware campaigns, and threat actors are already mobilizing to exploit the surge in online activity, fan engagement, and financial transactions tied to the 2026 FIFA World Cup.
In this article, we focus on a critical stage in the attack chain: lure infrastructure designed to push users toward malicious or high-risk mobile applications.
About this World Cup Series
The United States, Canada, and Mexico have been selected to host the 2026 FIFA World Cup. As of early April, the lineup of all 48 teams set to compete in the final stage is now complete.
How are threat actors responding? What’s already emerging across deep and dark web communities?
This blog is part of Flare’s World Cup 2026 Cybercrime Series, a collection of focused research pieces examining the evolving threat landscape surrounding the tournament. The series explores key areas including phishing infrastructure, fraud and scams, infostealer attacks, illegal streaming services, illicit betting platforms, insider threats, and other cybercriminal activities targeting the 2026 World Cup.
Key Findings About the World Cup Mobile Malware Ecosystem
- Flare identified a massive mobile malware infrastructure of at least 600 IP addresses hosting thousands of domains, all using a consistent template format to distribute malicious Android applications. The infrastructure is not FIFA-specific; it covers betting, gaming, productivity, leisure, and cryptocurrency apps, with World Cup themes used as one of many interchangeable lures.
- A coordinated APAC campaign spanning 64 IP addresses targets Chinese-speaking users with fake soccer betting apps, using domain rotation, disposable TLDs, and psychological pressure tactics to push users into downloading applications outside trusted app stores. The campaign employs multi-stage redirect chains and explicitly instructs users to disable security controls before installation.
- Trojanized APKs are being distributed under FIFA branding. One app disguised as a “FIFA Crypto” platform was flagged by 15 antivirus engines on VirusTotal as a malicious mobile trojan. There is no official FIFA cryptocurrency; the “FIFA Coin” concept referenced in these campaigns does not exist as a launched product.
- Sports-tech branding is being weaponized. The AYX sports data company’s branding and past club partnerships (Atletico de Madrid, AS Roma) are being used across dozens of domains to lend credibility to betting and app download funnels, blurring the line between legitimate marketing and fraud infrastructure.
Detect Malware Infrastructure Exploiting Your Brand
Flare identifies large-scale lure infrastructure, trojanized apps, and fraudulent domains weaponizing brand identities to distribute malware, enabling security teams to disrupt campaigns before they reach customers.
Hunting FIFA-Related Mobile Malware Campaigns
Our research targeted a specific stage in the attack chain: the lure websites (for desktop and mobile) that promise something enticing and end with the user downloading malware. We found several live infrastructures, including ones that specifically target soccer fans.
APAC Mobile Malware Campaign: 64 IPs Targeting Chinese-Speaking Users
The first infrastructure is constructed of 64 distinct IP addresses with Hong Kong geo-location all hosting the same Chinese-language template, Based on the language and regional targeting, we assess this campaign targets Chinese speaking users, with infrastructure based in Hong Kong. When accessing the website, users are redirected to an intermediate page.
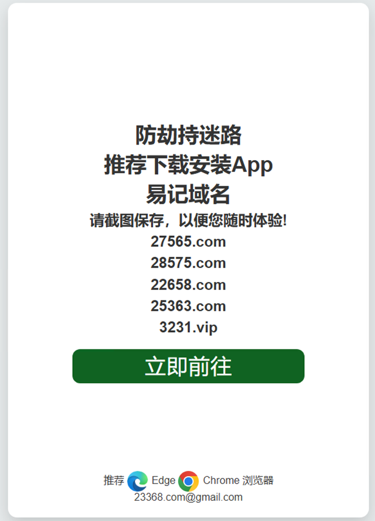
Malicious mobile app landing webpage
The page translates to:
“Prevent hijacking and getting lost
Recommended to download and install the App
Easy to remember domain name
Please take a screenshot and save it so that you can experience it at any time!”
The page in this sequence uses psychological pressure to encourage victims to install the application with claims that it will protect the user from malware (ironically), and help them reach the website faster.
This reveals some information about the infrastructure behind the campaign: it acts as a resilience and redirection layer by explicitly instructing users to download an app to “avoid blocking,” while providing a rotating list of domains. This is a hallmark of mature cybercriminal operations: domain rotation, disposable TLDs (e.g., .vip), and multi-entry access points to maintain availability despite takedowns. The inclusion of browser recommendations, simple UI, and even a contact email further reinforces the illusion of legitimacy while supporting operational continuity for the attackers.
Clicking the green download button advances to a more polished advertisement for betting.

The following webpage looks like a soccer app to attract victims
The image uses well-known soccer imagery, fabricated “official partner” claims, and high-pressure incentives (bonuses, high win rates) to create a sense of legitimacy and urgency. This is a common tactic: blending recognizable sports branding with financial incentives to lure users into clicking, registering, or downloading an application. The presence of multiple domains and strong calls to action such as “Download App” or “Play Now” indicates that the primary goal is to move users off the web and into controlled environments where fewer security controls exist.
From a linguistic and regional perspective, the use of Chinese language suggests targeting of specific user segments or affiliation with established offshore betting networks, many of which operate in loosely regulated environments. However, the visual elements (global soccer stars, World Cup references) are intentionally universal, allowing the same infrastructure to be repurposed across geographies. Combined with piracy sites, Telegram distribution, and malvertising channels, these campaigns form a scalable funnel from user acquisition to fraud, credential harvesting, and potential malware delivery. In the context of major events like the World Cup, this ecosystem becomes even more effective, leveraging hype and urgency to convert victims at scale.
APAC Sports-Tech Infrastructure: 25 IPs, Inconclusive Intent
A large and suspicious mobile app infrastructure was recently created. We observed 25 dedicated IP addresses all pointing to a newly registered domain (aiyouxisport[.]com[.]cn). The infrastructure is hosted on servers of a US-based hosting company, FEDERAL ONLINE GROUP LLC.
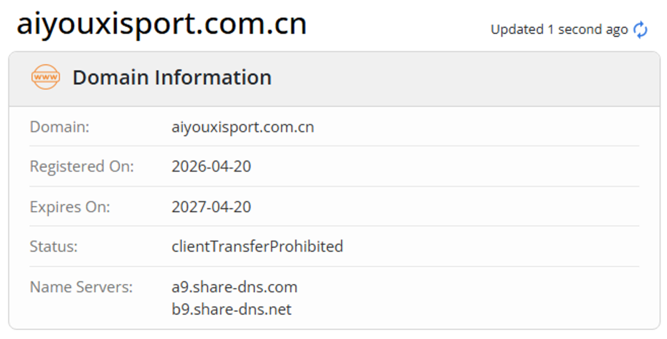
Whois registration details for the aiyouxisport[.]com[.]cn domain
The website is built with the same static Chinese-language template, presenting a dedicated platform that combines both data and statistics about soccer, tightly linked to the Chinese company AYX Sport.


Screenshots of the website of the newly registered domain
This isn’t suspicious on its own. AYX is an Asia-based company, mainly positioned as a sports-tech and entertainment company, and there are also some publications that position the company as adjacent to betting infrastructure. This makes it relevant from both a business and cybersecurity perspective, especially in scenarios involving scams, phishing, or large sporting events where such platforms can be leveraged as trust-building entry points.
It develops platforms that deliver live match data, interactive content, and data-driven experiences for sports audiences, often working with clubs and brands to expand their presence in Asian markets.

AYX and Atletico de Madrid were official partners between 2021 and 2023

AYX and AS Roma were official partners between 2021 and 2022
For instance, if we look for the title appearing on the website template we found “爱游戏体育官网 | 亚洲领先的综合体育竞技与足球数据平台” (translated as iGame Sports Official Website), the results that are strongly connected to AYX.
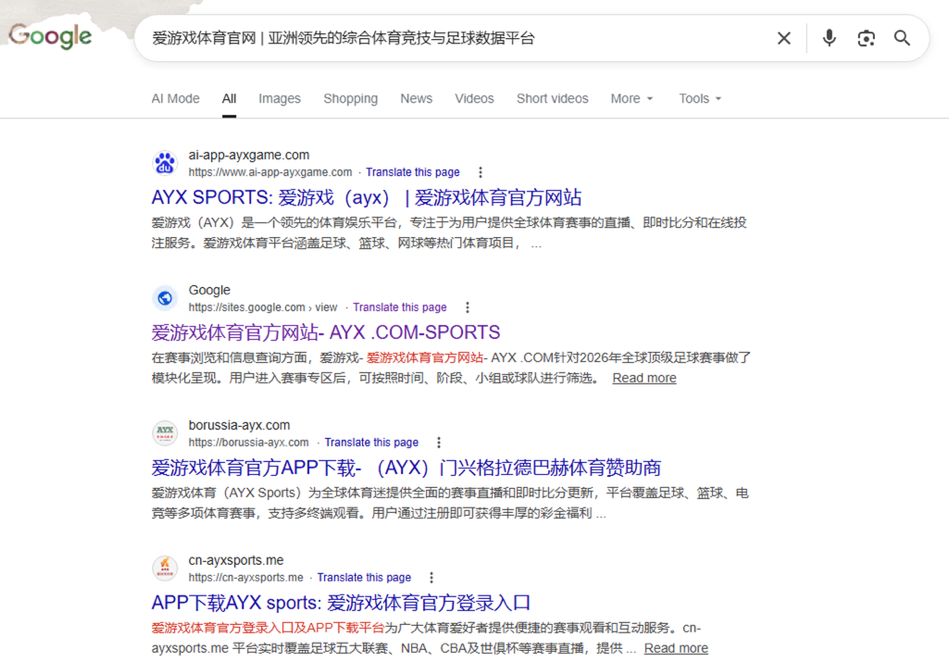
Google search for the website template title
Almost all these results include AYX in the domain name (except the Google based site). If we chose the “borussia-ayx[.]com” domain, it may refer to Borussia Dortmund, but we couldn’t find any official connection between the German club and AYX. The website itself is designed for sports betting with the AYX logo.

The domain borussia-ayx[.]com leads to a betting site
The site acts as a gateway or landing page for gambling platforms targeting Chinese-speaking users, with banners promoting “欧冠冠军盘” (Champions League betting market) and “免单55888元” (a bonus of up to ~55,888 RMB), which are typical gambling incentive messages.
We also inspected the Google site that appeared in the same search above. It contained a link to another AYX-linked domain, positioning itself as the “2026 World Cup Official Recommendation Platform.”
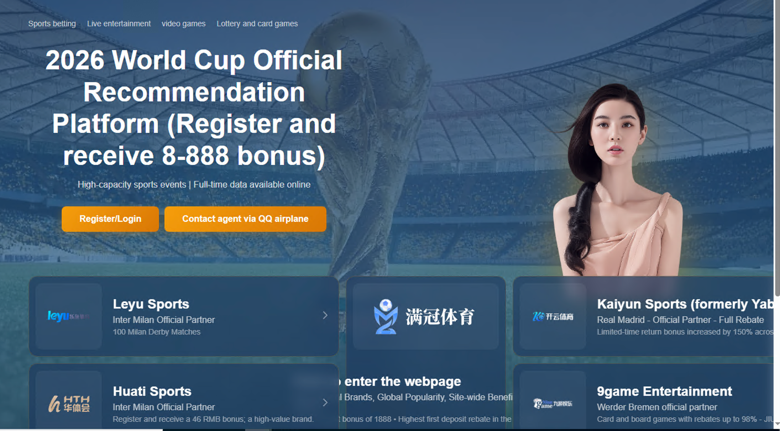
An AYX-betting related website
Following one link led to redirections through many other links, featuring images of various current and past iconic soccer players such as Erling Haaland, Lautaro Martínez, and Karim Benzema.


Images of famous soccer players used to promote betting websites
One of the landing pages included a link to download a mobile app, encouraging users to use a device that doesn’t contain China’s “National Anti-Fraud Center” application for security and privacy reasons.
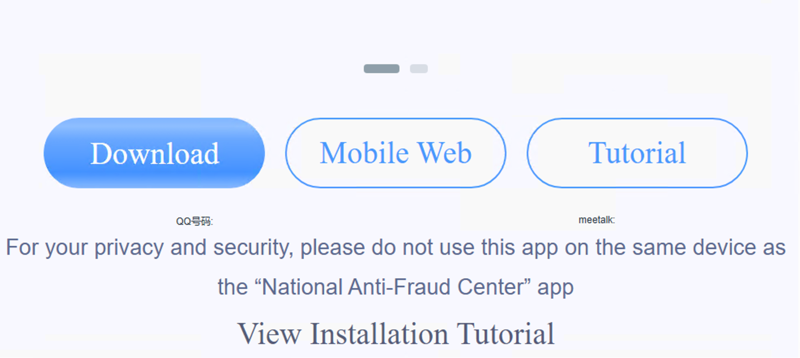
Users are encouraged to use devices that don’t run the National Anti-Fraud Center app
The same page included instructions on how to circumvent download and installation blockers.

Instructions to disable network controls before installing
For context, the National Anti-Fraud Center is a Chinese fraud prevention and reporting mobile application developed by the Ministry of Public Security, that published an app in March 2021. It blocks suspicious content, provides channels for reporting online fraud, and raises fraud awareness. These manipulative instructions are surely meant to bypass either a malware blocking mechanism or an illegal gambling blocking mechanism.
We downloaded the APK and sent it to VirusTotal. It wasn’t indexed on VirusTotal, and our scan only returned one detection (by Sophos), flagging it as a potentially unwanted application or malicious. It’s possible that this application is benign, or the app is effective at hiding malicious intent and evading detection.
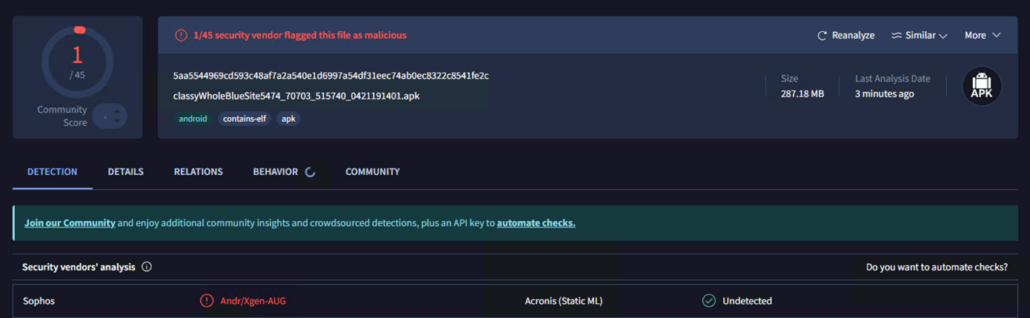
VirusTotal detections for the downloaded APK
Opportunistic Campaign: Fake FIFA Crypto App
One interesting finding was a website that encouraged downloading a “Crypto-FIFA” app.
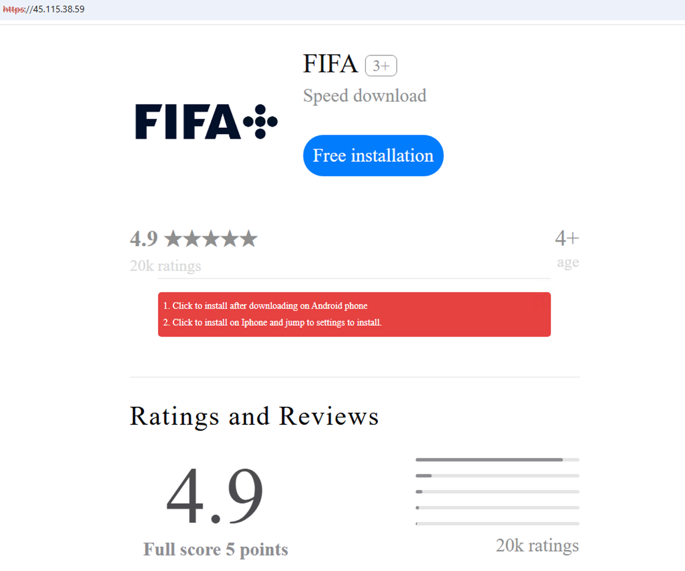
FIFA Crypto coin related website offering a malware-laden download
We downloaded the file (app.apk; MD5: d73aae8b7c3f1dec14ae06a861ac296b) and submitted it to VirusTotal, which had 15 detections, marking it as a malicious mobile trojan by most engines.
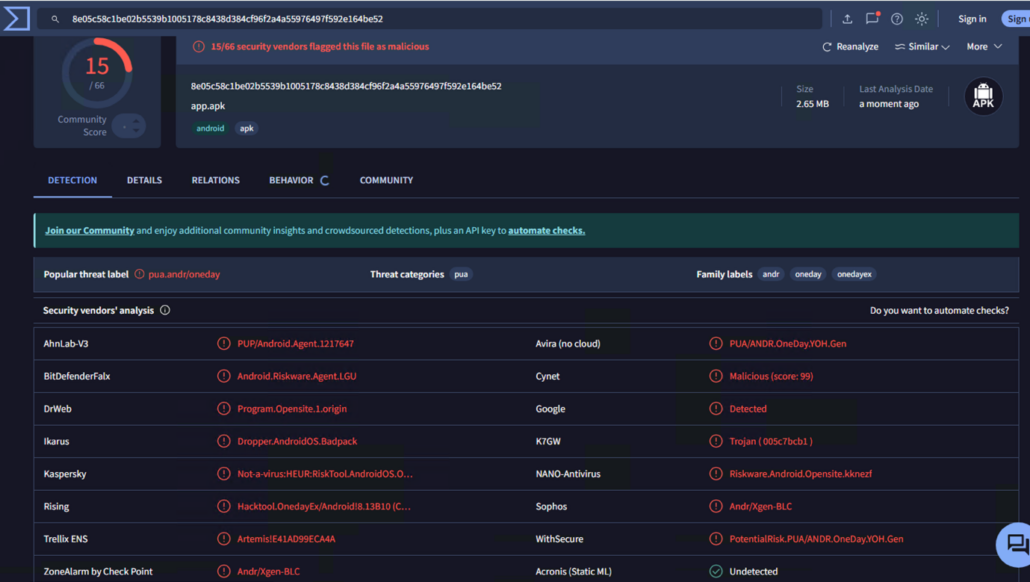
VirusTotal detections for the downloaded APK
Using distinct markers from this sample, we expanded our search and identified a massive infrastructure of at least 600 different IP addresses with thousands of listed domains, all with the same format. This is not a FIFA-dedicated infrastructure, and is a non-specific Android application malware distribution infrastructure, covering leisure application, betting, productivity, games, and anything you could imagine, with the FIFA crypto coin serving as one of the lures.
What is the FIFA Crypto Coin?
As of 2026, there is no officially launched FIFA cryptocurrency, despite public statements in 2025 by FIFA President Gianni Infantino indicating that the organization is exploring the idea of a global “FIFA Coin.” FIFA’s current involvement in blockchain is focused on initiatives like FIFA Collect, which offers digital collectibles and fan engagement experiences rather than a tradeable token. There is no confirmed launch date, no official coin available for purchase, and most assets labeled online as “FIFA Coin” or similar are unofficial, speculative, linked to scams or malicious malware delivery, like in the example we found.
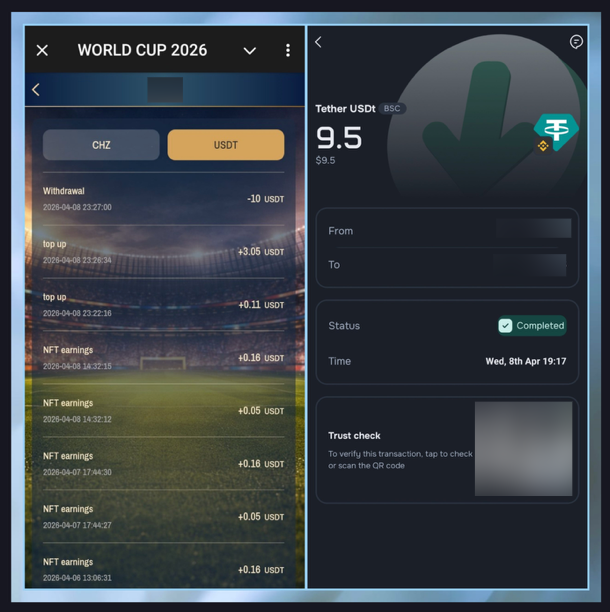
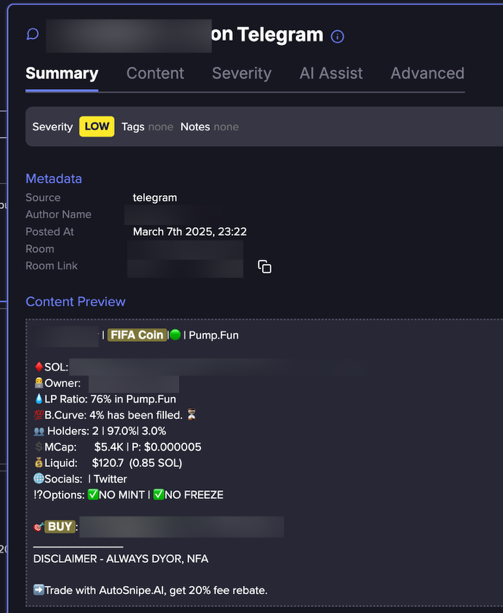
World Cup 2026 related crypto operation, most likely a scam (Flare link to post, sign up for the free trial to access if you aren’t already a customer)
The screenshots above show a very promising ad that promises users easy profits by investing small amounts to earn daily returns in “CHZ coins,” along with bonuses, referral rewards, and World Cup–themed NFT income opportunities. It contains common indicators of crypto Ponzi schemes: guarantees fixed returns, relies on referrals, impersonates the Chiliz ecosystem, and operates through Telegram bots.
Now is the Time to Detect and Disrupt Mobile Malware Campaigns
Our investigation reveals a multi-layered and rapidly evolving threat landscape leveraging World Cup themes to drive user acquisition into malicious and gray-market ecosystems.
We identified large-scale infrastructures, ranging from tightly coordinated APAC-based campaigns to opportunistic global malware distribution networks, all using consistent templates, domain rotation strategies, and psychologically engineered lures.
These campaigns frequently rely on sports branding, fabricated partnerships, and financial incentives to build trust, while ultimately directing users to download mobile applications outside trusted ecosystems. In some cases, these applications appear to be linked to illegal betting operations or remain inconclusive in intent, while others are clearly malicious, including trojanized APKs disguised as FIFA-related crypto or fan platforms.
The blending of legitimate-looking sports-tech branding (such as AYX-related ecosystems), betting funnels, and malware delivery highlights a convergence of fraud, monetization, and cybercrime infrastructure operating at scale. For organizations in sports, media, finance, and digital services, the window to detect and disrupt these campaigns is now.
Detect Malware Infrastructure Exploiting Your Brand
Flare identifies large-scale lure infrastructure, trojanized apps, and fraudulent domains weaponizing brand identities to distribute malware, enabling security teams to disrupt campaigns before they reach customers.





