On December 4th, 2025, a user operating under the handle “Student” posted what they called “the deepest state tax fraud guide that exists anywhere on the planet right now.” According to the post, the author had executed 127 fraudulent tax filings between September and December 2025, yielding $1,927,400 in stolen refunds across 15 states. The guide included success rates by US state, average payouts, and processing timelines: operational data from what the poster claimed were real filings.
California alone allegedly averaged $17,800 per fraudulent return with a 97% success rate. Texas processed refunds in as little as three to nine days. The guide ranked states by “max that still lands clean,” or in other words, the highest refund amount a criminal could claim without triggering additional scrutiny. California’s threshold sat at $24,000. New York at $22,000.
Five years ago, tax fraud was simpler: steal an SSN, file a return, hope for the best. What the “Student” guide describes is something different. The author demonstrates detailed knowledge of IRS validation logic, including which credits stack without raising flags, which states still process refunds with minimal verification, and which employer identification numbers (EINs) pass validation checks. The guide reads like technical documentation, not opportunistic crime.
Underground forums now host detailed guides explaining IRS cross-checking procedures, state-by-state vulnerability assessments, and the specific data fields required to construct a return that passes automated screening. Separate marketplaces trade in “fullz,” or complete identity packages containing Social Security numbers, dates of birth, addresses, and prior-year income figures harvested from data breaches and insider theft.
If the “Student” post is accurate (and the technical specificity suggests at least partial authenticity), a single operator testing 127 identities across multiple states and generating nearly $2 million in fraudulent refunds represents a standard operational model, not an outlier. Multiplied across dozens of active criminal groups, the aggregate loss becomes staggering. This is no longer petty fraud. This is an organized criminal economy with documented ROI, supply chains, and technical specialization.
Key Takeaways from the Underground Tax Fraud Economy
- Threat actors can “credit stack” to exploit multiple tax credits in combination.
- Accounting platforms are a high-value target as they possess: client tax returns, W-2 forms, bank account information, and QuickBooks records.
- The IRS and state systems operate in siloes, and fraudulent filings can fall through the cracks. Organizations can build better systems to build a better safety net.
- Organizations can protect W-2 data through separating HR systems (with W-2 data) from general network access, implement MFA on payroll systems, and add controls for flagging suspicious W-2 requests.
Anatomy of Modern Tax Refund Fraud: How Criminals Exploit the System
Fraudulent tax returns succeed or fail based on plausibility. The IRS doesn’t just validate that data exists; it validates that data makes sense together. A $200,000 W-2 from a janitor in rural Mississippi triggers immediate review. A $14,000 refund for a warehouse worker in Dallas does not. This distinction explains why modern tax fraud requires what underground markets call “fullz.”
An SSN alone is not enough information. Threat actors need the Social Security number, date of birth, current address with ZIP+4 code, prior-year adjusted gross income (AGI), and ideally W-2 information showing employer name and EIN. The prior-year AGI is critical because the IRS requires it for e-file PIN verification. Without it, the return fails at the first validation gate.
The SSN must pass SSA Death Master File checks. The name must match SSA issuance records. The address must be USPS-verified and align with income norms for that ZIP code. Filing status must be plausible; claiming “Head of Household” without dependents triggers flags. The W-2 data must reference a valid employer EIN that matches the claimed occupation and region. A fraudulent return claiming $18,000 in wages from a nonexistent company fails immediately.
State systems layer additional verification. California requires matching W-2 data showing state withholding. New York requires NYC address verification for child credit claims. Texas, however, has no state income tax and performs minimal checks, which helps explain why it ranks third nationally for fraudulent refund success, despite lower average payouts.”
Credit stacking is where sophistication emerges. Criminals exploit the Earned Income Tax Credit (EITC), child tax credits, and state-specific bonuses in combination. The “Student” guide explicitly ranked states by which credit combinations “still land clean.” California’s optimal stack combined CalEITC, Renter’s Credit, and dependent claims. Illinois layered EITC with K-12 credits. Each credit adds plausibility. A single mother claiming EITC plus three dependent children with matching SSNs and ages is far less suspicious than an isolated refund claim.
The verification gap exists because IRS and state systems operate in silos. The IRS validates against SSA records and employer W-2 submissions. State systems validate against their own W-2 databases and address records. Neither system cross-checks with the other in real time. A criminal can file a federal return claiming $18,000 in wages from Company X and simultaneously file a state return claiming $22,000 from Company Y. Both pass initial screening because each system only validates against its own records.
This fragmentation is structural. The IRS processes roughly 150 million returns annually. Real-time cross-state verification would require infrastructure that doesn’t exist. Criminals exploit that gap methodically.
Data Breach Pipeline: From Corporate Compromise to Tax Fraud
The threat actors executing $1.9 million in fraudulent refunds didn’t generate their own data. They bought it.
In October 2025, a threat actor posted a 2GB archive from an accounting firm to a cybercrime forum. The contents were client ledgers, bank statements, and financial records. For tax fraud operators, this was gold. Bank statements reveal prior-year income. Client ledgers show employer names and EINs. Combined with SSN and address data from other breaches, these records become complete “fullz” packages ready for filing.
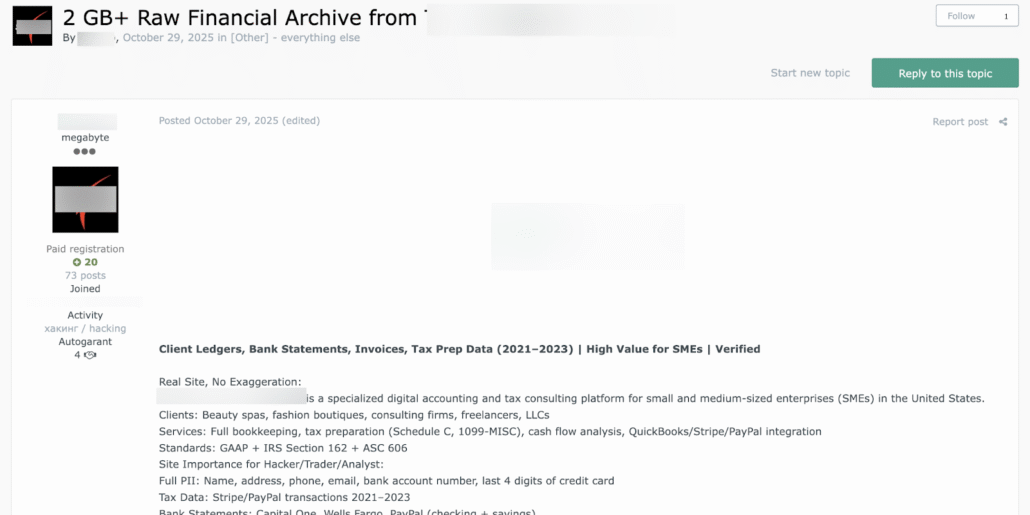
Cybercrime forum post about data from an accounting firm
Accounting platforms represent the highest-value targets. These firms maintain client tax returns, W-2 forms, bank account information, and QuickBooks records: essentially the complete identity profile a threat actor needs. A single breach of a mid-sized accounting firm can yield thousands of viable packages. The data is already organized. The income figures are verified. The employer information is legitimate.
The cybercrime marketplace has responded with specialization. Sellers now advertise “fullz” by quality tier. Basic packages (SSN plus date of birth) sell for $5 to $15. Mid-tier packages adding current address and phone number command $25 to $50. Premium packages including prior-year AGI, W-2 employer details, and bank account information sell for $100 to $300.
The “Student” guide’s 127 successful filings likely drew from premium inventory. Validation happens in real time. Buyers test packages against SSA records before committing to large purchases. Sellers maintain reputation scores based on package viability. The market operates with the efficiency of any legitimate e-commerce platform, except the product is stolen identity data.
Government employee compromises add another layer. In late 2025, access to a Vietnam tax authority employee mailbox appeared for sale on breach forums. Tax authority credentials grant access to filing systems, verification databases, and internal communications. A compromised government email account doesn’t just provide data; it provides infrastructure. An operator using legitimate tax authority credentials can file returns that bypass standard scrutiny entirely.
This pipeline, from breach to marketplace to filing, operates continuously. Each major data exposure feeds the tax fraud economy. Each accounting firm’s compromise generates thousands of viable packages. The supply of stolen identity data has become the binding constraint on tax fraud scale, not the demand.
Detection Evasion: The Technical Infrastructure Behind Tax Fraud
Filing a fraudulent return from your home IP address is operational suicide. The IRS logs every filing source. State tax systems track geographic patterns. Underground guides are explicit about this.
Residential proxies sold by IPRoyal, Bright Data, and Smartproxy are useless for tax fraud, according to forum discussions. All major residential proxy providers log user activity and comply with U.S. subpoenas. In a tax fraud investigation, that audit trail becomes evidence. Threat actors instead compromise small business networks via RDP breaches or phishing, then route filings through the victim’s static business IP. A business connection carries higher trust scores in IRS systems. It leaves no third-party logs. The exit node belongs to someone else entirely.
Geographic consistency matters. An IP address geolocating to Dallas filing a return for a taxpayer claiming residence in Dallas is normal. The same IP filing returns for 47 different addresses across 12 states triggers immediate review. Sophisticated operators maintain separate compromised business networks for different geographic regions, rotating between them to match claimed addresses.
Browser fingerprinting evasion follows similar logic. A fresh Chrome profile with no extensions, no telemetry, and no history of prior filings looks legitimate. According to the “Student” guide, criminals use retail Windows 10 licenses, not server editions or virtual machines. IRS systems flag virtual machine artifacts, including TTL values and network stack signatures. The filing environment must appear to be a normal taxpayer’s computer.
Timing matters. The first two weeks of January see massive filing volume. A return filed on January 3rd blends into millions of legitimate submissions. A return filed on July 15th stands out. The “Student” guide documented that California refunds arrived within 4 to 10 days when filed in early January. The same state took 30+ days for mid-season filings, suggesting increased scrutiny.
Proxies, VPNs, and Tor are insufficient. Threat actors use compromised business infrastructure because it’s the only method that survives forensic analysis.
The 2026 Tax Season: Emerging Threats and Systemic Vulnerabilities
The “Student” guide ranks 15 states by refund payout and success rate. California leads at $17,800 average refunds with 97% success. Texas processes claims in three to nine days. Florida, lacking state income tax, requires almost no verification. These aren’t theoretical vulnerabilities. According to the post, they’re operational data from tested identities.
The IRS has tightened federal verification, but states have not kept pace.
Underground forums now host step-by-step guides covering data sourcing, return construction, verification evasion, and cashout mechanics. These aren’t written for experts. They’re written for anyone with access to stolen identity data and basic technical competence. The barrier to entry has collapsed. A threat actor with a “fullz” package and a compromised business IP can file a return in an afternoon.
Synthetic identity fraud represents the next evolution. Rather than stealing a complete identity, criminals blend real data (valid SSN, actual address) with fabricated elements (fictional W-2s from shell companies, invented dependents). This hybrid approach exploits the gap between federal and state verification systems. The IRS checks SSN validity. States check address consistency. Neither system validates whether the W-2 actually exists until after the refund is issued.
Business tax fraud is shifting from individual returns to corporate filings. A fraudulent Form 1120-S (S-corporation return) claiming $500,000 in losses generates refunds through carryback provisions. These filings receive less scrutiny than individual returns because they’re less common. The verification infrastructure is thinner.
The systemic gap remains unchanged: the IRS processes returns first, verifies data second. Criminals exploit this sequence. A return filed on January 3rd reaches the cashout stage before verification flags it as fraudulent. By the time the IRS identifies the fraud, the refund has been transferred through multiple accounts and converted to cryptocurrency.
Federal improvements have created a false sense of security. The real threat has migrated to state systems, synthetic identities, and business filings. The 2026 tax season will test whether defenses can evolve faster than the fraud itself.
Defensive Measures Against Tax Fraud for Organizations and Individuals
W-2 data is a high-value asset to businesses. Here are what organizations can do to treat them as such:
- HR systems storing W-2 information can be segregated from general network access.
- Implement multi-factor authentication on payroll platforms (if it’s not there already).
- Add controls that flag suspicious W-2 requests, particularly requests from unfamiliar IP addresses or outside normal business hours. A criminal filing a fraudulent return needs the actual W-2 data the IRS will cross-check against. If your W-2 system logs access attempts, you can detect reconnaissance before the fraud occurs.
Accounting firms hold complete identity packages: tax returns, bank statements, W-2s, and client addresses. A breach of an accounting platform is a breach of thousands of viable fraud packages simultaneously.
These firms can:
- Encrypt client data at rest and in transit
- Monitor access logs for bulk exports or unusual query patterns
- Establish protocols for detecting suspicious filings using their client data, such as a return filed from an unfamiliar IP, claiming a different address, or filed before the client typically files
Individuals have limited options but several effective ones. The IRS Identity Protection PIN program generates a unique six-digit code required to file returns. Criminals cannot file using your SSN without this PIN. Enrollment takes minutes and prevents the most common attack vector. Credit monitoring services alert you when new accounts are opened in your name, catching identity theft before it reaches the tax system. Filing early, within the first week of January, creates a race condition. If you file legitimately before a threat attempts fraud using your SSN, the IRS system flags the fraudulent return as a duplicate.
Tax authorities must move beyond static verification. Real-time cross-state data sharing would prevent the same SSN from filing in multiple states simultaneously. Enhanced verification for high-refund claims, requiring biometric authentication or callback verification, would eliminate the passive filing environment criminals currently exploit. The IRS currently processes returns and verifies data afterward. Reversing that sequence would catch fraud before refunds are issued.
HR and finance teams can be better equipped by recognizing the social engineering patterns criminals use. Requests for W-2 data from “payroll vendors,” urgent requests for employee SSNs to “verify records,” or inquiries about filing procedures from unfamiliar contacts are reconnaissance. These requests precede fraud by weeks or months. Training employees to report suspicious requests costs nothing and catches attacks in progress.
For 2026, here are the overarching immediate actions across different stakeholders:
- Employers can audit W-2 access logs and implement controls flagging bulk requests.
- Accounting firms can detect returns filed from unfamiliar locations using their client data.
- Individuals can enroll in the IRS Identity Protection PIN program.
- Tax authorities can share breach intelligence and cross-state filing data.
Looking Towards the 2026 Tax Season
A single operator tested 127 stolen identities across 15 states and landed $1.9 million in fraudulent refunds between September and December 2025. If the “Student” post is accurate, this wasn’t a sophisticated operation requiring specialized expertise. It was a methodical application of publicly available guides, stolen data, and infrastructure gaps that remain unfixed despite years of warnings.
Tax fraud is a symptom of broken identity infrastructure. Until that infrastructure is rebuilt with verification at its core rather than its periphery, criminals will continue exploiting the gap between filing and validation. The 2026 tax season will reveal whether the system can adapt faster than the threat.
Monitor for Cybercrime Activity with Flare
The Flare Threat Exposure Management solution empowers organizations to proactively detect, prioritize, and mitigate the types of exposures commonly exploited by threat actors. Our platform automatically scans the clear & dark web and prominent threat actor communities 24/7 to discover unknown events, prioritize risks, and deliver actionable intelligence you can use instantly to improve security.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. See what external threats are exposed for your organization by signing up for our free trial.





