
By Christopher Budd, Cybersecurity Evangelist
What is the state of the dark web right now?
The guiding theme is: the dark web isn’t static, it functions as a market economy with new sites and shops going up and down on a routine basis. And it presents unexpected, unforeseeable developments.
Eric Clay (CMO) and Mathieu Lavoie (CTO), who co-lead Flare Research, along with Tammy Harper, Senior Threat Intelligence Researcher specializing in ransomware; Chris d’Eon, Threat Intelligence Researcher focusing on North Korea (DPRK); and Oleg Lypko, Cyber Threat Intelligence Researcher focusing on Russian-speaking cybercrime, recently spoke of their work in monitoring cybercrime in the annual State of the Dark Web panel.
Keep reading for the highlights plus additional research our team has added since the panel. Better yet, join the Flare Academy Discord to access the full training to get all the info, including tips and tricks not included in this recap. Even if you’re seen the training, you’ll want to read this for the new information that expands what we covered there.
Stay Ahead of a Dark Web That Never Stands Still
As forums splinter, infostealers shift toward enterprise identity, and Telegram channels proliferate, Flare continuously monitors the sources that matter, alerting your team to exposed credentials, stealer logs, and threat actor activity targeting your organization.
Key Takeaways for Cybercrime in 2026
- The Russian invasion of Ukraine continues to shape trends in the Russian-speaking cybercrime ecosystem, driving both increased Western-Ukrainian law enforcement cooperation and Russia’s growing instrumentalization of cybercrime.
- Takedowns produce value beyond their initial disruption: While some question the long-term effectiveness of takedowns because the XSS takedown resulted in the forum coming back online under new management and a creation of another forum, other less obvious impacts of takedowns, including fractured communities and eroded trust, show that disruption is effective.
- The fall of Lumma stealer illustrates sometimes law enforcement isn’t the cybercriminals biggest risk, other cybercriminals can be.
- Infostealer malware remains an evolving threat even with Lumma stealer gone: enterprise identity credentials are increasingly at risk.
- Telegram remains the dominant platform for threat actors: more than 90% of the stealer logs that Flare sees is found on Telegram!
Russian-Speaking Cybercrime Ecosystem
There’s an important distinction to be mindful of regarding the Russian-speaking cybercrime ecosystem: Russian-speaking doesn’t mean Russian-born or Russian-national.
The map below shows the geographic distribution of Russian as-a-first-language speakers in and around Russia in Eurasia, the Middle East, and Europe.
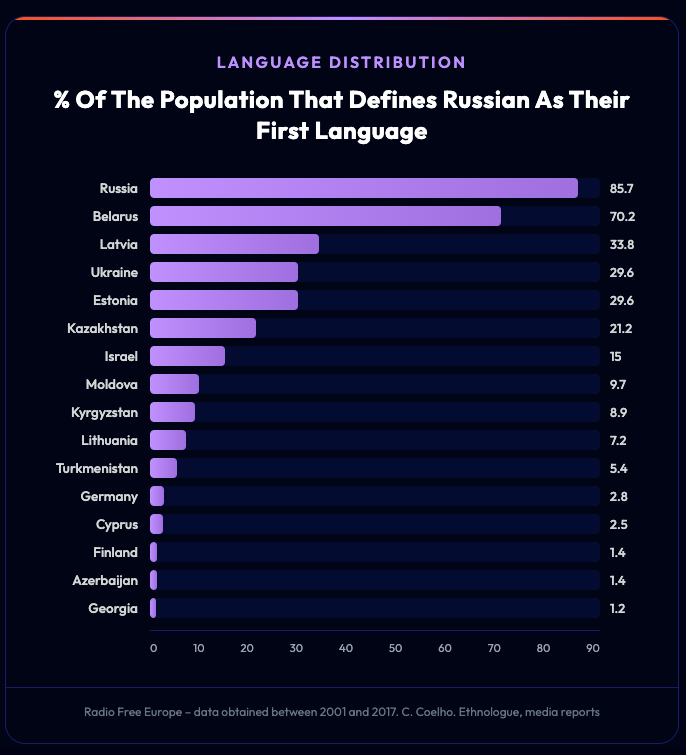
Percentage of population that defines Russian as their first language
The geographic spread of Russian speakers illustrates why this distinction matters. Russian is the first language for 85.7% of Russia’s population, but also for 70% in Belarus, 34% in Latvia, 30% in Ukraine and Estonia, and 21% in Kazakhstan. And also note the 700,000 Russian speakers in China.
Russian-Language Does not Equal Russian, a Case Study
Victoria Dubranova provides a documented example of a Russian-language threat actor who is neither in Russia nor Russian-born.
Dubranova, also known as Vika, Tory, and SovaSonya, is a Ukrainian national whose personal allegiance is closer to Russia. According to CyberScoop, she was indicted in December 2025 as “part of two Russian state-sponsored hacking operations that targeted water systems, food processing facilities and government networks across the United States and allied nations.” Dubranova is alleged to be part of the CyberArmyofRussia_Reborn (CARR), also known as Z-Pentest, and NoName057(16). Dubranova serves as an excellent example of several of the Russian-speaking cybercrime trends we examine. The fact that she is not Russian by birth or nationality only serves to further emphasize our point that Russian-language speaking does not equal being a Russian national.
Do Threat Actors Use Language to Complicate Attribution?
This is relatively rare, and most attackers use the languages they need to conduct business and be accepted in their communities. Our researchers have seen only a single case of someone deliberately mixing broken Russian and English to obscure analysis, but this was the exception.
What is more common is using coded language within a linguistic community. We found an example of this in Chinese-speaking cybercrime circles, where threat actors have been seen using characters with similar pronunciations but different tones to evade content filters. For example, writing the word for gambling (博彩, bó cǎi) as 菠菜 (bō cài, literally “spinach”) to bypass keyword searches.
Major Trends in the Russian-Language Cybercrime Ecosystem
The major trends in Russian-language cybercrime in the past year are shaped by one overwhelming factor: the war in Ukraine. These trends are tied to two shifts.
First, there’s continued, increasing cooperation between western law enforcement and Ukraine. Second, there’s the continued decreasing cooperation between western law enforcement and Russia, which goes hand in hand with Russia’s increased “instrumentalization” of cybercrime.
Increased Cooperation between Western Law Enforcement and Ukraine
We’ve already seen one clear example of the closer cooperation between western law enforcement and Ukraine: the extradition of Dubranova. In addition to this example there are several others that demonstrate the results of increasing cooperation between Ukraine and western law enforcement over the course of the past year: Operation Endgame, the arrest in Kyiv of the alleged admin of the forum XSS, and Operation Eastwood are all the results of the closer work between Ukraine and western law enforcement.
Operation Endgame was the largest operation ever against dropper botnets like IcedID, SystemBC, Pikabot, SmokeLoader, and Bumblebee. Ukrainian law enforcement conducted three of the operation’s four arrests and supported searches on Ukrainian territory. The coordinated international effort also seized over 100 servers and approximately 1,300 domains used in the malware infrastructure.
The arrest of “Toha” (the alleged handle of Anton Gannadievich Medvedovskiy), the alleged XSS forum administrator, took place in Kyiv in July 2025, with full support from Ukrainian authorities. XSS has operated since 2018, hosted approximately 50,000 accounts, and facilitated more than $7 million in illicit profits as a marketplace where criminals sold malware, traded access to compromised systems, and advertised ransomware-as-a-service platforms.
Operation Eastwood, also carried out in July 2025, was an operation carried out by Europol and Eurojust with support from 12 countries against a pro-Russian threat actor group named NoName057(16). BleepingComputer describes the group as “a pro-Russian hacking group that launched in March 2022 after the war in Ukraine began.” It’s also worth noting that NoName057(16) is one of the two groups that Dubranova is alleged to be a part of.
As of the end of 2025, according to the takedown operation’s site, the operation has involved nearly 20 countries and resulted in over 100 Distributed Denial of Service (DDoS) servers being disrupted.
Operation Eastwood is a particularly powerful example of the relevant trends because it shows not only the increased cooperation between Ukraine and western law enforcement, but it also shows how the shift on the Russian side naturally brings those two sides together as both cybercrime and “instrumentalization” of cybercrime by Russia increase.
Decreasing Cooperation from Russia and Instrumentalization of Cybercrime
The countervailing forces on the Russian side in the equation of ramifications from the war in Ukraine are actually represented by two separate but intimately related trends: decreased law enforcement cooperation and instrumentalization of cybercrime.
Russia enables its cybercriminal ecosystem to attack Western countries, while cooperating less and less with arrests of Russian threat actors.
The Russian government, and sometimes the Ukrainian and Belarusian governments (at least in the past), have instrumentalized cybercriminal communities and leaders for financial gain and political motivations.
Instrumentalization represents a junction point between nation-state and cybercriminal threat actors. Nation states can benefit from the capabilities and expertise of cybercriminals to carry out operations on their behalf. Cybercriminals meanwhile get tolerance or protection from the local authorities, which can extend to obstructing law enforcement activities that would otherwise have yielded cooperation in the past.
Dubranova’s case serves as an excellent example. The EPA’s press release regarding Dubranova’s indictment lays out simply and clearly how CARR allegedly operated and how instrumentalization works. “CARR was founded, funded, and directed by the Main Directorate of the General Staff of the Armed Forces of the Russian Federation (GRU). CARR has conducted dozens of destructive cyberattacks around the world, including attacks against critical infrastructure in the United States.” In other words, CARR is established and directed by Russian state actors, but populated by non-state actors and, in Dubranova’s case, Russian-speaking cybercriminals who aren’t Russian citizens.
In addition to the benefits already discussed, instrumentalization gives nation states a way to achieve their goals while maintaining “plausible deniability.”
Instrumentalization isn’t new. In fact, one of the best known examples of cybercrime instrumentalization comes from the Clinton email server hack in 2016. The threat actor behind the attack on US presidential candidate Hillary Clinton’s email was the administrator of a cybercrime forum and hired by two FSB agents to carry out this attack.
Learn more about Russian-language forums to monitor Russian cybercrime & state militarization.
Takedowns: Measuring Effectiveness Beyond the Initial Disruption
Takedowns always prompt questions about long-term effectiveness. The events of 2025 and early 2026 offer a richly nuanced answer, one that goes beyond the binary of “success” or “failure.”
The XSS Splintering
Even after Toha’s arrest, XSS is not gone as of this writing. The operation triggered a splintering that created two forums where there had been one.
Within days, a contested new administrator whose identity could not be verified by the existing moderation team, relaunched XSS on new infrastructure. This unknown figure banned veteran moderators, installed low-reputation staff with virtually no posting history, and relaunched the forum’s clearnet presence under the domain xss[.]pro, now bearing a Russian flag in the logo.
In a politically charged move, the site’s new administration also stopped considering Ukraine a Commonwealth of Independent States (CIS) country, effectively lifting the long standing prohibition on selling offensive material targeting Ukrainian entities, a rule that XSS had enforced for years alongside other major Russian-language forums. These changes fueled persistent rumors that the forum had become a law enforcement honeypot, or, conversely, that it had been captured by actors aligned with Russian state interests.
On August 2, 2025, eight ousted moderators collectively launched DamageLib as the “real” successor. The name was a deliberate nod to DaMaGeLaB, the original forum that Toha had relaunched as XSS in 2018. In interviews, one of the founders explained that XSS had functioned as an “infrastructure provider for ransomware business,” and that DamageLib would deliberately prohibit all commercial activity to avoid drawing the same law enforcement pressure.
The community split along trust lines. By late August 2025, DamageLib had attracted roughly 33,500 registered accounts, about two-thirds of XSS’s user base of around 51,000. However, engagement remained far lower: only 248 threads and about 3,100 posts in its first month, compared to over 14,400 messages on XSS during the month preceding the seizure. Traffic to the Exploit forum surged by nearly 24% as actors hedged their bets across multiple platforms, and over $6 million in user deposits remained contested, further poisoning relationships. DamageLib’s deliberate absence of a marketplace and escrow system may protect it from law enforcement, but it also limits the economic incentives that drive forum loyalty. The net result was not elimination, but fragmentation and a deep erosion of trust.
The RAMP Seizure: A Different Pattern, Same Outcome
Six months later, a different scenario unfolded. On January 28, 2026, the FBI seized the Russian Anonymous Marketplace (RAMP), a forum that had operated since mid-2021 as one of the few underground spaces explicitly welcoming ransomware-as-a-service promotion. RAMP had emerged precisely because forums like XSS and Exploit had banned ransomware content following the Colonial Pipeline fallout, and it became a critical hub for groups such as LockBit, ALPHV/BlackCat, Qilin, and DragonForce. Despite this outsized role, RAMP remained a comparatively small community: roughly 300 active users and just over 3,000 messages in 2023, illustrating how a niche forum can punch well above its weight in the ransomware ecosystem.
The seizure replaced both RAMP’s clear web and Tor sites with an FBI banner that pointedly mocked the forum’s tagline. It was conducted in coordination with the US Attorney’s Office for the Southern District of Florida and the DOJ’s Computer Crime and Intellectual Property Section, and DNS records confirmed full law enforcement control of the domains. One of RAMP’s original founders, Mikhail Matveev (also known as Wazawaka), had already been arrested in Russia in 2024.
Unlike the XSS case, RAMP’s remaining administrator, known as “Stallman,” a well-known figure on XSS and Exploit, publicly confirmed the takedown and stated unambiguously that there were no plans to rebuild. His reluctance likely stemmed from fear of arrest: RedSense co-founder Yelisey Bohuslavskiy assessed that Stallman was now a “void asset for the Russian services” and likely next in line for detention following the wave of cybercriminal arrests in 2025.
Yet even without a direct successor, the ecosystem adapted. The removal of a major hub forced migration rather than elimination, and those transitions were “often chaotic, opening new risks for threat actors: loss of reputation, escrow instability, operational exposure, and infiltration.”
Ransomware actors quickly dispersed across two divergent paths:
- Rehub, an open-membership forum where DragonForce registered the very day RAMP went offline
- T1erOne, a more exclusive, invitation-only platform targeting higher-value actors
Activity also shifted toward Telegram, where operational security is harder to monitor. The immediate effect was both psychological and to a lesser extent operational: a collapse of trust in shared infrastructure and the realization that even long-standing platforms can disappear overnight. Moreover, the demise of repositories like RAMP, which served as a useful resource for newcomers, has created a more significant operational hurdle. Threat actors and RaaS groups that are not well connected and established in the ransomware ecosystem now face increased difficulty in acquiring initial access and finding new affiliates.
The Fall of Lumma Stealer
The disruption playbook is not limited to forums. Russian-speaking cybercrime, takedowns, and infostealers converge in one of the year’s most instructive stories: the turbulent decline of Lumma Stealer.
Lumma was a Russia-developed Malware-as-a-Service (MaaS) used to steal credentials, cookies, and crypto wallet tokens. Between March 16 and May 16, 2025, Microsoft identified 394,000 infected Windows computers, while the FBI estimated 10 million infections globally, making Lumma the most significant infostealer threat at the time.
In May 2025, Microsoft’s Digital Crimes Unit (DCU), the US Department of Justice, the FBI, Europol, and Japan announced a coordinated global takedown, seizing approximately 2,300 malicious domains and redirecting more than 1,300 domains to Microsoft-controlled sinkholes. Flare’s telemetry showed only a minor, temporary drop in Lumma traffic following the operation. Within weeks, the operators had rebuilt their infrastructure and resumed operations, remaining highly active through the summer.
If the law enforcement takedown was only a temporary setback, what caused Lumma’s actual disruption?
Rival threat actors. Starting in late August 2025, an underground site called “Lumma Rats” published a full doxxing of five alleged core Lumma operators, including names, passports, bank accounts, and other operational details. The campaign’s consistency and depth suggested insider knowledge or access to compromised accounts. On September 17, Lumma Stealer’s Telegram accounts were also reportedly compromised, severing the operators’ primary communication channel with customers. Unlike the brief dip after the May takedown, this triggered a sharp and sustained drop in both new sample detections and command-and-control infrastructure activity beginning in September 2025. Customers began migrating to rival platforms such as Vidar and StealC.
An important caveat: the accuracy of the doxxed information and the actual involvement of the named individuals have not been independently verified. The campaign may have been motivated by competitive grudges, could be a disinformation operation, or even an exit scam by the Lumma operators themselves; attribution should be treated with caution.
The Broader Pattern
These cases are not isolated, nor are they specific to the Russian-speaking ecosystem. BreachForums, the prominent English-language cybercrime forum, has been seized multiple times since 2024: first in May 2024 under Baphomet’s administration, then again after a chaotic cycle of relaunches and disruptions through 2025 that saw arrests of key figures including IntelBroker and several ShinyHunters members, culminating in an October 2025 takedown of its latest incarnation, which had been repurposed as a data extortion portal by the Scattered Lapsus$ Hunters group. Each iteration came back shorter-lived and with diminished trust.
What XSS, RAMP, Lumma, and BreachForums share is a common pattern: takedowns do not fail simply because criminal activity continues. They succeed by imposing compounding costs on the ecosystem, fragmenting communities, destroying accumulated reputation and escrow systems, forcing actors into unfamiliar environments where operational security is weaker, and sowing the kind of pervasive mistrust that makes criminal collaboration riskier and less efficient. We often think of chaos as a tool that favors cybercriminals, but the disruption that law enforcement injects into the ecosystem generates chaos that works against them, too. The true measure of a takedown is not whether it stops crime, but whether it degrades the trust infrastructure that enables it at scale.
Infostealers: Fewer Infections, Yet Greater Impact
Lumma may be gone, but infostealers as a category remain a significant and growing threat, one that is rapidly shifting from consumer credential theft toward high-impact enterprise identity compromise.
Infostealers infect systems and systematically exfiltrate credentials, session tokens, browser-saved passwords, autofill data, and active session cookies to command-and-control (C2) infrastructure. Unlike phishing or large-scale data breaches, a single infostealer infection gives attackers a complete, current snapshot of a victim’s digital identity, often yielding dozens of enterprise credentials that are then passed around or sold in the cybercrime ecosystem, primarily on Telegram.
The scale of the problem is staggering. According to our 2026 State of Enterprise Infostealer Exposure report, which analyzed 18.7 million stealer logs collected throughout 2025, more than 2.05 million infections exposed enterprise Single Sign-On (SSO) or Identity Provider (IdP) credentials.
That means more than one in ten infostealer infections now potentially grant attackers access to corporate email, cloud infrastructure, SaaS platforms, and internal systems.
Preliminary data from late 2025 shows this figure surging to 16% of infections, well above earlier projections and signaling rapid acceleration.
What makes these findings even more alarming is that they emerged despite a roughly 20% year-over-year decline in total infostealer infections. Fewer machines are being compromised, but each compromise is far more consequential. This divergence points to a structural shift in attacker economics: infostealers are increasingly landing on systems that already hold high-value enterprise access, and attackers know it. If current trends hold, one in five infostealer infections could expose enterprise credentials as early as Q3 2026.
Why Centralized Identity Makes It Worse
The growing impact of infostealers is inextricable from the way organizations now manage identity. As enterprises consolidate authentication around centralized platforms like Microsoft Entra ID, Okta, and AWS IAM Identity Center, a single compromised credential can unlock dozens of connected systems. This concentration of access is precisely what infostealers exploit.
The numbers bear this out. According to our report:
- Microsoft Entra ID appeared in 79% of enterprise identity logs, making it the most frequently exposed identity provider by a wide margin, with AWS in second place appearing in 12% of enterprise identity logs.
- More than 18% of enterprise identity logs contained credentials for multiple identity providers, significantly increasing the blast radius of a single infection.
- Over 1.17 million logs contained both enterprise credentials and active session cookies, enabling attackers to bypass multi-factor authentication (MFA) entirely and gain immediate access without triggering login challenges.
Infostealers, in other words, are not just stealing passwords. They are harvesting the keys to entire enterprise environments.
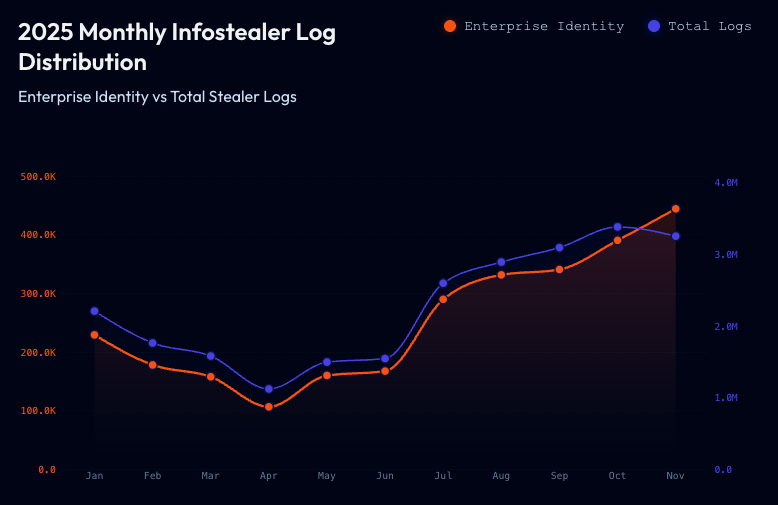
Stealer log distribution by month in 2025, comparing enterprise identity with all logs
The Gateway to Larger Attacks
Critically, infostealers are not just an end in themselves but a means to other ends. They serve as enablers and facilitators for attacks like ransomware by providing attackers with the valid credentials they need to simply log in. According to Verizon’s 2025 Data Breach Investigation Report, stolen credentials are involved in 88% of basic web application attack breaches. CrowdStrike’s 2025 Global Threat Report puts the average e-crime breakout time at just 48 minutes, meaning that once an attacker has working credentials, the window for defenders to respond is vanishingly small.
Case Study: The 2024 Snowflake Data Breach
The 2024 Snowflake data breach demonstrates how infostealers enable cascading, supply-chain-style attacks. Threat actors used stolen credentials from stealer logs to access Snowflake customer environments directly rather than targeting Snowflake itself. A single category of stolen data mushroomed into successful attacks against numerous downstream companies. The breach has been variously attributed to UNC5537, Scattered Spider, and ShinyHunters.
How Infostealers are Distributed and Monetized Today
A common question is whether threat actors still manually review individual stealer logs or rely primarily on bulk, aggregated data. The answer is both, depending on the attacker and the attack. Targeted operators still comb through individual logs to gain access to specific high-value accounts. Meanwhile, an increasing share of stolen data is collected, aggregated, and sold in bulk on underground platforms and forums.
This market has also undergone its own disruption. Genesis Market, once the premier marketplace for infostealer data, is now defunct. Russian Market continues to operate. But the broader trend has been a migration away from centralized forums and toward Telegram, where more than 90% of the stealer logs we observe now appear. On Telegram, a large number of aggregator channels repackage username-login-password (ULP) combo lists and stealer logs into ZIP files, forming bulk collections most commonly used for password-spraying attacks, where threat actors test large volumes of credentials against services to see which ones still work.
With 46% of personal device infostealer logs now containing corporate credentials, the line between personal and professional exposure has effectively disappeared. A single employee’s compromised personal laptop can hand attackers the keys to an entire corporate environment.
Explore an interactive stealer log below:
Infostealer Log Structure
EDUCATIONALClick folders to expand, files to view contents. All data is fictional.
Telegram: Maintaining Its Preeminence in Cybercrime, Despite Russian Political Pressure
Telegram continues to play a central role in all major cybercrime trends, the distribution of infostealers, and the adaptability of criminal communities in the face of disruption. Telegram functions as a sprawling underground marketplace where stolen credentials, malware, phishing kits, and fraud services are traded at scale. Threat actors are also leveraging Telegram’s API as backend infrastructure for malware command-and-control, using bots to automate the exfiltration of stolen data directly from infected machines.
While the arrest of Pavel Durov in France in August 2024 raised questions about the platform’s stability and prompted Telegram to announce increased cooperation with law enforcement, the platform is now facing a far more structural and direct political threat emanating from Russia.
The Escalation of the Political Crisis in Russia
The Russian government has intensified its campaign against Telegram, with a consensus among analysts and legislators indicating a high probability of a complete platform block in 2026, likely between April and September. This pressure comes from Roskomnadzor (RKN), which accuses Telegram of non-compliance with Russian laws, specifically concerning data localization and the refusal to comply with content removal requests, with over 150,000 cited crimes since 2022. The original April 2018 court order to block Telegram was never formally reversed and remains technically valid.
The government’s approach has been one of “phased pressure.” On February 10, 2026, RKN began actively throttling Telegram nationwide via TSPU, deep packet inspection boxes installed on every major Russian ISP’s network. The system identifies Telegram’s MTProto protocol by signature and throttles traffic down to approximately 128 KB/s, degrading media file delivery by roughly 55% while text messaging remains functional. This followed earlier restrictions: voice and video calls were blocked in August 2025, and partial throttling began in October 2025.
Key Duma officials have signaled a full block is the intended trajectory. Deputy Chair of the Information Policy Committee Andrey Svintsov predicted a full block within six to eight months and floated possible designation of Telegram as an extremist organization. Deputy Speaker Mikhail Delyagin described a full block as likely by September 2026, timed to regional elections. Analyst Denis Kuskov (Telecom Daily) stated outright that the decision to shut Telegram down has already been made.
Beyond technical restrictions, Durov himself is now targeted by a criminal investigation under Article 205.1 of the Russian Criminal Code (facilitation of terrorist activity, up to 15 years), based on FSB materials. In response, Durov declared on February 5 that Telegram has never disclosed “a single byte” of message data and would shut down rather than comply. These actions are taking place in a broader context of reduced cooperation with the West and the instrumentalization of cybercrime by the Russian state.
The government is simultaneously pushing MAX, a state-backed “super-app” developed by VK, as the designated replacement. MAX is legally required to integrate with SORM-3, providing the FSB with comprehensive backdoor access to user communications and metadata, a design that should deter any actor with basic operational security concerns.
The Reaction of Russian-Speaking Malicious Actors
Despite this escalating threat, Russian-speaking malicious actors do not appear to show undue concern for the moment. There is little in-depth discussion in Russian-speaking cybercriminal spaces about the need to migrate or what the community will do in the event of a total block. The primary reason is that current technical workarounds still allow those who need Telegram to continue using it without major interruption.
The Russian civil society and technical community has deployed increasingly sophisticated circumvention methods against the throttling, often adopting tools originally developed by civil society in China or Russia:
- MTProto proxies using Telegram’s built-in proxy settings
- Self-hosted “stealth” proxies that masquerade as regular HTTPS websites to defeat DPI probing
- Local DPI bypass tools (GoodbyeDPI, zapret) that manipulate TCP packets to trick throttling equipment
- Obfuscated VPN protocols like Xray/VLESS Reality that disguise tunneled traffic as visits to popular websites
These workarounds are well-documented and actively maintained across Russian technical communities, particularly on Habr. The legal status currently protects users: Telegram is throttled but not formally banned, and using VPNs for lawful purposes remains permitted. However, from March 1, 2026, RKN gained expanded centralized control powers over the Russian internet, and the technical community expects further tightening.
Regarding MAX, it appears unlikely that threat actors will adopt it as an operational platform. While we have observed that some threat actors are already buying and selling MAX accounts (signaling Russia-focused scam activity targeting its user base), no cybercriminals have been observed sharing MAX contacts or setting up commercial channels on this platform. Currently, MAX only allows verified users to create broadcast channels, and the Russian government’s open end-to-end control makes it fundamentally unsuitable for criminal operations.
Malicious actors are primarily pragmatic and commercially oriented: they continue to use Telegram because no viable alternative has emerged, and available circumvention tools keep their operations running. This is consistent with broader analysis of the Sovereign RuNet’s impact, which shows that while Russia’s expanding censorship and surveillance capabilities have created psychological pressure among threat actors, they have not significantly hindered their ability to conduct cybercrime. Russian-speaking cybercriminals have not yet started seriously solving the migration problem, a clear sign that existing workarounds are sufficient for now.
Adaptation and Continued Dominance
Despite increased post-Durov moderation, Telegram continues to thrive as an illicit ecosystem. Our research confirms that Telegram remains the dominant messaging platform in the cybercriminal underground. Some communities have begun branding Telegram as “not safe” following the moderation changes, and Netcraft observed a decline in its use for credential exfiltration via phishing sites. Nevertheless, criminal use of the platform persists. Following disruptions, whether from forum closures, infostealer takedowns, or moderation waves, malicious actors adapt by creating private, invitation-only channels restricted to trusted members.
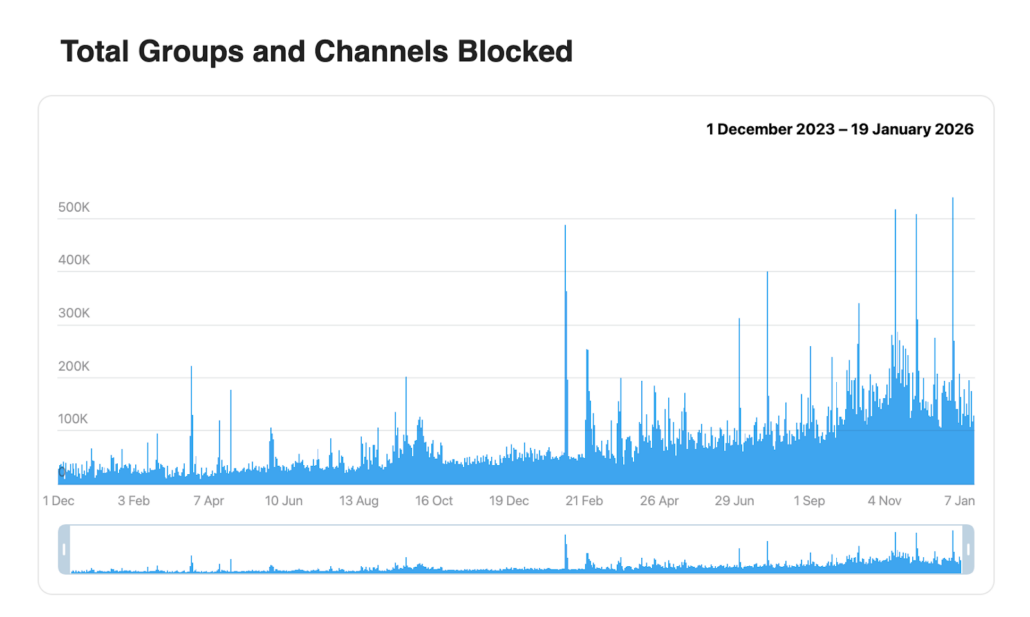
Telegram moderation activity shows continued growth in activity (Source: Telegram)
The often-cited alternative, Signal, is not used in the same way by cybercriminals. Signal presents two major drawbacks for illicit operations: its groups are invitation-only, making community discovery impossible without a direct link, and it lacks Telegram’s Bot API, channels, and open ecosystem that enable the automation and scalability cybercriminals depend on. Our research confirms that while Signal saw a slight uptick after Telegram’s policy changes, it remains marginal in the cybercriminal ecosystem, with Discord and Session playing more significant but still niche secondary roles.
Close monitoring must continue, with readiness to adapt quickly. If a full block materializes, technically sophisticated actors will likely maintain access through obfuscated tunneling, while less technical actors may fragment across multiple platforms, making the ecosystem harder to monitor but not displacing Telegram’s central role. In all scenarios, Telegram’s preeminence in cybercrime is unlikely to be seriously challenged in the near term.
What Security Teams Should Keep in Mind for 2026
Through natural evolution, takedowns, and cybercriminals turning on one another, 2025 brought significant changes to the Russian-speaking cybercrime ecosystem, online forums, and the infostealer landscape.
In the Russian-speaking cybercrime ecosystem, law enforcement cooperation between the West and Ukraine has intensified, yielding significant victories including the arrest of “Toha” and the disruption of XSS’s thirteen-year run. Russia’s decreasing cooperation and instrumentalization of cybercrime counterbalances those gains with new risks.
The most compelling insight from the past year may be that takedowns produce value well beyond their initial disruption. The ripple effects, shattered escrow, fractured communities, rival doxxings, can prove more damaging than the takedown itself. Disruption may be the most realistic outcome, and it is a meaningful one.
Telegram has survived the 2024 arrest of its co-founder and appears to be thriving, absorbing the market for infostealer data that once lived on centralized marketplaces.
The dynamism that characterizes the dark web shows no signs of slowing.
For full analysis, demonstrations, and additional resources, see the complete training on Discord. Join the Flare Academy Discord to access the full presentation.
Stay Ahead of a Dark Web That Never Stands Still
As forums splinter, infostealers shift toward enterprise identity, and Telegram channels proliferate, Flare continuously monitors the sources that matter, alerting your team to exposed credentials, stealer logs, and threat actor activity targeting your organization.





