This article was updated on April 9, 2026 and originally published on June 13, 2023.
Phishing remains one of the most prevalent forms of cybercrime.
Threat actors count on phishing campaigns to provide initial access to targets’ networks and devices, which lays the groundwork for future attacks and breaches.
With such high stakes, understanding and detecting phishing domains has become a critical component of any robust cybersecurity strategy. But the rise of phishing kits, pre-built toolkits that allow anyone to stand up a convincing phishing site in minutes, has made detection harder than ever. Understanding how these kits work also reveals their weaknesses, and those weaknesses are what defenders can exploit.
Learn more about phishing kits based on our analysis of 8,600+ chats in our report: The Phishing Kits Economy in Cybercrime Markets.
Track Phishing Kits Before They Target Your Organization
Flare monitors dark web forums, criminal marketplaces, and Telegram channels where phishing kits are sold and traded, giving your team early visibility into new kits, stolen credentials, and campaigns targeting your brand.
What is a Phishing Domain?
A phishing domain is a counterfeit website or portal designed by cybercriminals to trick users into believing that they are interacting with a legitimate site. The goal is to deceitfully acquire sensitive information such as login credentials, credit card details, or other personal data that can be exploited for fraudulent purposes.
One common example of a phishing domain might resemble your bank’s login page. It looks nearly identical to the original, from the logo to the form fields requesting your username and password. However, once you enter your information, it doesn’t go to your bank. Instead, it lands in the hands of a malicious actor who now has access to your financial account.
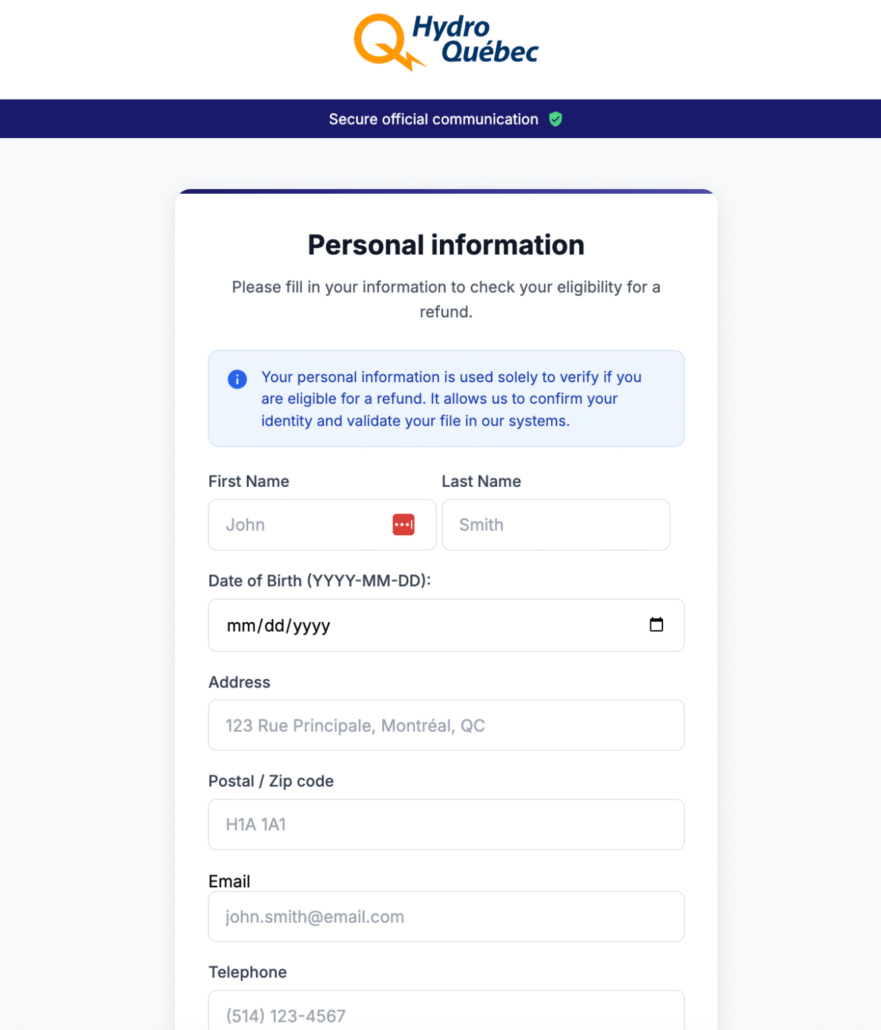
Example of a phishing site mimicking utility provider’s site
A few years ago, it was easier to spot the telltale signs of a phishing domain; because threat actors built malicious sites from scratch, there were often clear signs that a site wasn’t the real deal. Think misspellings and suspicious URLs. If a threat actor wasn’t great at building sites or writing, you’d be able to tell if a site was malicious.
Now, however, phishing kits are creating malicious sites that are difficult to discern from the sites they are meant to imitate.
What is a Phishing Kit?
Phishing kits are pre-built, downloadable kits that any threat actor can purchase and deploy to create a believable, professional-looking phishing domain. These domains usually appear to be a page from Microsoft, Instagram, PayPal, or another legitimate site. The stolen data is then exfiltrated to Discord or Telegram.
A phishing kit comes with everything a threat actor needs to make its own credential harvesting operation, all tidily bundled into zip files:
- Cloned HTML pages of legitimate, trusted sites
- JavaScript to hide client-side code and behavior
- PHP to exfiltrate stolen credentials to remote servers or email
Phishing kits are sold and traded on underground forums, making phishing campaigns available to threat actors who might not have the skills to build their own site.
They also work fast; a kit can go from purchase to live in minutes. A threat actor can also reuse the same kit several times, but this can work in your favor. Because kits are deployed repeatedly with minimal changes, they leave consistent, detectable patterns that defenders can track.
How to Detect Phishing Kits
Phishing kits are reusable by design, which means defenders can spot them across multiple campaigns, even when attackers rotate domains, hosts, or delivery methods.
1. Identify static code artifacts
Most phishing kits reuse the same JavaScript, CSS, and PHP files with minimal changes. Your team can search for:
- Unique variable names
- Obfuscation patterns and techniques
- Repeated favicon or image hashes
These identifiable code snippets act as kit-level IoCs, which are far harder for attackers to change than domain names.
3. Track credential exfiltration endpoints
Nearly all phishing kits include code that sends captured credentials back to the attacker.
Common indicators include:
- Reused command-and-control URLs
- Identical webhook destinations or API endpoints
- Telegram bot tokens
Finding these patterns allows your team to connect multiple phishing sites to the same kit.
4. Monitor hosting patterns and infrastructure reuse
Although attackers register new phishing domains frequently, they often reuse items. Look for repeats of :
- VPS providers
- ASN ranges
- Filenames and directory paths
Infrastructure reuse can help cluster phishing domains into campaigns tied to a specific kit or operator.
5. Analyze anti-detection and anti-sandbox features
More advanced phishing kits include evasion logic such as:
- Blocking traffic from cloud providers or known security vendor IP ranges
- Redirecting bots away from the phishing content
- Requiring specific referrer or user-agent headers to display the malicious page
These patterns are often unique to each kit family, making them powerful detection markers.
6. Leverage threat intelligence
Phishing kits are widely sold and traded on dark web forums, Telegram channels, and criminal marketplaces. Monitoring these sources helps organizations:
- Identify newly released kits before they are deployed
- Understand kit capabilities and evasion techniques
- Track updates, add-ons, or variants
- Preemptively log indicators tied to popular kits
Shifting the Focus from Monitoring Phishing Domains to Phishing Kits
Phishing domains are not going away, and phishing kits are making them easier to create, harder to distinguish from legitimate sites, and faster to deploy at scale. But the same reusability that makes kits efficient for attackers also makes them trackable for defenders. By shifting focus from individual phishing domains to the kits behind them, security teams can detect campaigns earlier, connect seemingly unrelated incidents, and disrupt operations at their source rather than chasing one domain at a time.
Track Phishing Kits Before They Target Your Organization
Flare monitors dark web forums, criminal marketplaces, and Telegram channels where phishing kits are sold and traded, giving your team early visibility into new kits, stolen credentials, and campaigns targeting your brand.